The Open Systems Interconnect (OSI) model is a seven-layer visual model that describes the networking system and how apps can communicate with each other.
In the earlier days of computing, devices from diverse manufacturers were not interoperable. To facilitate that, the International Organization for Standardization created the OSI model in 1984, providing a set of common standards for different equipment to communicate with each other.
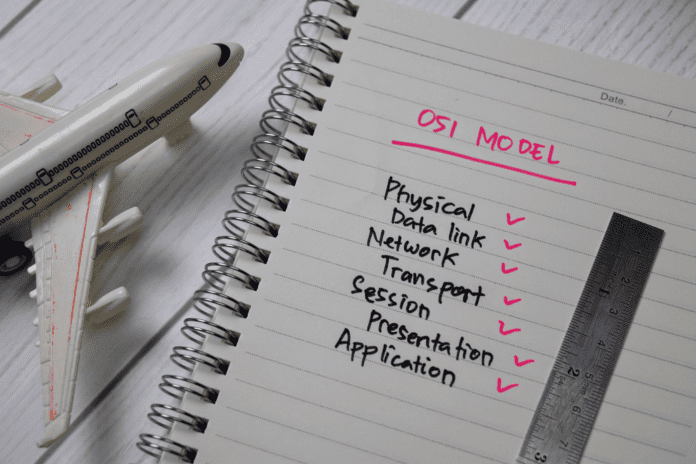
Starting from the bottom, the seven layers are:
- Physical layer
- Data link layer (DLL)
- Network layer
- Transport layer
- Session layer
- Presentation layer
- Application layer
Each of the seven layers performs a specific function and communicates with the layer above and below it.
Today, the OSI model is primarily used as a reference model to teach computer professionals the basics of computer networking.
Table of Contents
7 layers of the OSI model
Breaking up networking functions into layered functionalities helps network engineers understand the workings of their networks better and helps them zero in on the problems more quickly. Here’s how each layer serves that purpose.
Layer 1: Physical layer
Layer 1 is the physical layer and also the lowest layer of the OSI model. This layer transmits information in the form of bits (1s and 0s) from one node to the next. Components of the physical layer include cables, power plugs, connectors, network interface cards (NICs), and other hardware.
Layer 2: Data link layer (DLL)
The data link layer (DLL) is the second layer and handles the node-to-node transfer of data. Its primary function is to ensure that the transferred data is error-free.
DLL comprises two sub-layers: logical link control (LLC) and media access control (MAC). LLC handles multiplexing and demultiplexing signals as well as node flow control and error management, while MAC handles hardware interactions with the network.
Layer 3: Network layer
The network layer is responsible for routing data packets from a source host to a destination host. It does so by selecting the shortest possible path. This layer is also responsible for packet forwarding and logical addressing. Necessary protocols used in this layer are ICMP, ARP, RIP, IPv4/v6, and IPsec.
Layer 4: Transport layer
The transport layer is responsible for transferring data from hosts to users. The most frequently used protocols in the transport layer are User Datagram Protocol (UDP) and Transmission Control Protocol (TCP). While TCP enables data transfer between computing devices, UDP is designed for speedy data transmission.
Layer 5: Session layer
The session layer is responsible for controlling, managing, and terminating the connections between computers. Functions include token management, creating dialog units, synchronizing data flow, and efficiently using available network resources.
Layer 6: Presentation layer
The presentation layer handles information related to data coding and encoding. It’s also called the syntax layer.
Layer 7: Application layer
The application layer is the one that is most familiar to end users, as it governs communication with software housed on their host PCs. Note that this layer doesn’t include the actual software or application itself, but only the protocols that manage them.
How the OSI model works
The OSI model works by segmenting all transmitted data through a seven-layer abstraction in order to more efficiently and securely parse and deliver the data to its destination.
To better understand this process, here’s an example of the OSI model’s abstraction process in operation. Let’s say you decide to send an email from computer (A) to computer (B).
Your email application client resides on layer 7. When you send the email, the layer 7 application protocol encapsulates or places a header on your messages and sends it to layer 6.
Layer 6 compresses the data and transfers it to layer 5. It also encrypts the data before sending it forward.
Layer 5 opens a session between your computer and the outgoing server. It also decides which data packet belongs to which file. Finally, it adds an appropriate header and transfers the data to layer 4.
When layer 4 receives data from layer 5, it segments it and assigns each segment a destination and source port number to ensure the data gets delivered to the correct service. Layer 4 also enforces security controls.
Layer 3 breaks the data into packets and transmits it over multiple paths. The packets contain destination and source IP addresses for easier identification of end devices.
Then the data is sent to layer 2, where the DLL adds MAC addresses to the packets, which are then grouped into frames. To deliver to the correct destination, the LLC sublayer adds control information to each frame.
Finally, the frames are transmitted to layer 1 in the form of 1s and 0s. That binary data is then transferred to device B either through electric pulses (Ethernet), radio waves (Wi-Fi), or light pulses (Fiber optics).
Layer 1 ensures bit synchronization so that, as the data reverses its abstraction through each layer at the destination, the end user receives the information in a readable format—just as it was intended.
Why the OSI model is still relevant
Although the TCP/IP model is the preferred model for IT professionals and is used in most modern computers, the OSI model remains relevant for its easy troubleshooting, flexible nature, and continued use as a teaching tool.
Easy troubleshooting
The OSI model enables IT teams to classify their asset inventories into easily digestible chunks at each layer. In case of a problem, spotting and identifying problems within the layers is relatively easy thanks to their specificity—especially at the top three layers, which are all collapsed into one in the TCP/IP model.
Flexibility
The OSI model supports both connectionless services as well as connection-oriented services, making it highly flexible in nature.
Acts as a teaching aid
The OSI model serves as an excellent teaching aid as it provides users with a clear understanding of how software and hardware work together. By breaking down networking concepts into layers, it removes ambiguity and provides network professionals with a clear picture of networking.
Drawbacks of the OSI model
Although the OSI model does have benefits, it does fall short in some areas, including practicality, popularity, and complexity.
Theoretical model
Compared to TCP/IP, OSI functions as more of a theoretical framework that doesn’t offer many solutions for practical implementation.
Less popular
While the OSI model was developed at the same time as the TCP/IP model, it couldn’t compete with the popularity of TCP/IP. IT professionals generally preferred TCP/IP protocols more; as a result, the OSI model fell increasingly out of favor.
More complex
The OSI model is quite complicated and thus has implementation problems. In contrast, the TCP/IP model is more effective and easier to operate.
Duplication
There’s a lot of duplication of services in the OSI model. For instance, both the transport and the data layer provide similar services. To add to it, several layers, like the presentation or the session layer, are barely used, which is in part why they were collapsed into the application layer in TCP/IP.
OSI vs. TCP/IP model
The Transmission Control Protocol/Internet Protocol (TCP/IP) is a communication protocol that shows how a particular computer can connect to another over the internet. The model has a four-layer architecture and is designed to ensure the transmission of error-free data in the form of packets across networks.
From top to bottom, the four layers of the TCP/IP model comprise the application layer, transport layer, internet layer, and network access layer.
While both OSI and the TCP/IP model have a layered architecture and provide almost the same functionalities, they have several dissimilarities. They include:
- OSI is a conceptual framework, while TCP/IP is a connection-oriented protocol
- TCP/IP has 4 layers, while OSI has 7 layers
- OSI uses the session layer, presentation layer, and application layer to demarcate the upper layers, while TCP/IP uses only the application layer
- Layers 1 and 2 are separate in the OSI model, but in TCP/IP they are combined
- The layers in the OSI model are highly interdependent. So, if the lower layer fails, there is a probability that the upper layers will also not work well either. In contrast, TCP/IP offers a more flexible architecture.
OSI and TCP/IP layers compared
The below table shows how the TCP/IP model simplifies the layering system compared to OSI’s more granular and complex model.
| OSI layers | TCP/IP layers |
|---|---|
| Application | Application |
| Presentation | |
| Session | |
| Transport | Transport |
| Network | Internet |
| Data link | Data link |
| Physical | (Hardware) |
What does the future of the OSI model look like?
Given the strong preference of network administrators for the TCP/IP model and its massive usage, it may be tempting to assume OSI’s days are numbered.
However, although the OSI model may no longer be popular, there’s no denying that it serves as a reference model for thousands of IT experts, aiding them in designing more efficient and reliable systems.
In fact, even today, the OSI model is referenced in product manuals and certification exams. So even if it’s unlikely that the OSI model will experience a resurgence in practical usage, it’s equally unlikely to disappear from common theoretical application altogether.
Bottom line: How the OSI model is used today
Despite not being used much in practice today, network engineers and vendors still reference the OSI model to have a complete overview of computer networking and to learn about its functions. While the TCP/IP protocol is implemented more by modern networks, still the OSI model is used as a guide by networking professionals to get clarity on data abstraction paths and processes.
We evaluated the top enterprise Wi-Fi solutions and found the five best choices for your network.