Encryption is a critical component of modern information security that transforms data into an unreadable format, safeguarding it from unauthorized access. The process involves turning readable data, known as plaintext, into an unreadable format called ciphertext using a specific algorithm and a key. Only those who possess the correct key can decrypt the ciphertext back into plaintext and read it.
There are two primary types of encryption: symmetric and asymmetric.
- Symmetric encryption: Commonly used for private communication, data storage, and high-performance network connections.
- Asymmetric encryption: Used for secure email communication, safeguarding email communication, authenticating with digital signatures, and protecting online transactions.
Table of Contents
Types of encryption: Symmetric vs. asymmetric encryption
What is symmetric encryption?
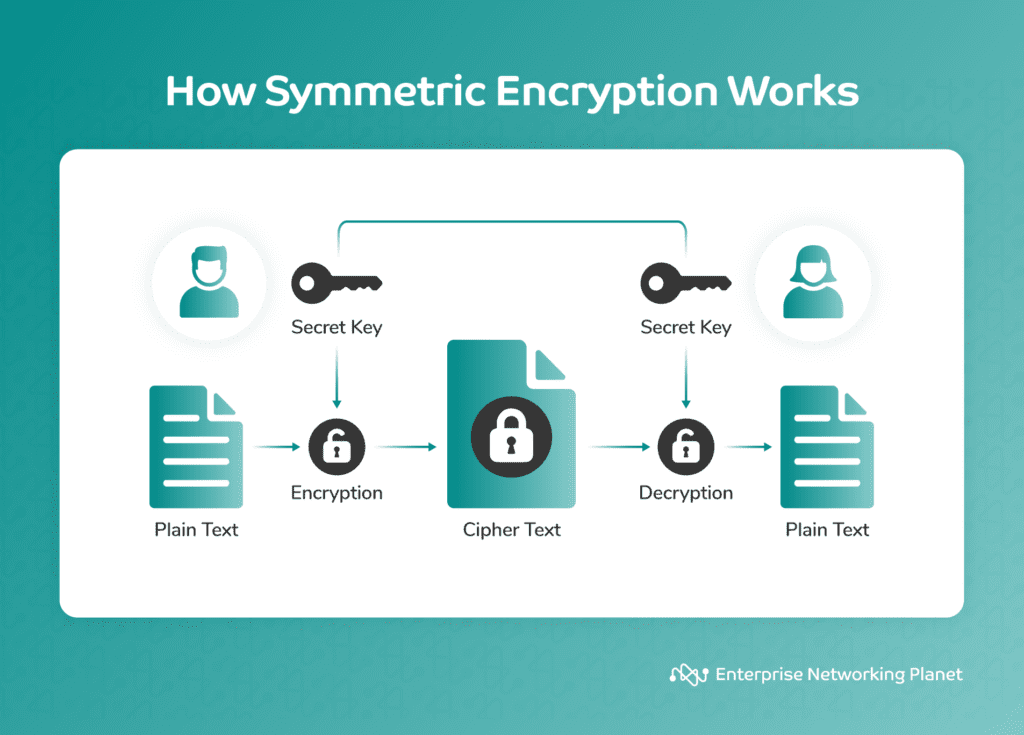
Symmetric encryption, also known as secret key encryption, involves the use of the same key for both encryption and decryption. It is fast and efficient, making it ideal for encrypting large amounts of data.
While this encryption method promotes speed and efficiency, it is less secure than asymmetric encryption because it uses a single key for both encryption and decryption. This makes it easier for hackers to break the code.
When is symmetric encryption used?
Symmetric encryption is the ideal choice for rapidly encrypting large amounts of data. It plays a key role in the Advanced Encryption Standard (AES) used by the U.S. government to encrypt classified information. It is also suitable for parties already sharing a secret key, especially when speed and efficiency are of utmost importance.
Real symmetric encryption examples
- Data storage: When you encrypt files on your computer or a USB drive using a password, it often involves symmetric encryption. The same password is used to both encrypt and decrypt the data.
- Secure Sockets Layer (SSL) and Transport Layer Security (TLS): These protocols use symmetric network encryption to protect data transmitted over the internet, such as during online banking transactions or when you log in to a secure website.
- Virtual Private Networks (VPNs): Many VPN services use symmetric encryption to secure the data transmitted between your device and the VPN server, ensuring privacy and security while browsing the Internet.
- Disk encryption: Whole-disk encryption tools like BitLocker (Windows) and FileVault (macOS) use symmetric encryption to protect the entire contents of a hard drive or solid-state drive (SSD).
- Messaging apps: Some messaging apps like WhatsApp use symmetric encryption to safeguard the messages sent between users, so that only the recipient with the correct decryption key can read the messages.
What is asymmetric encryption?
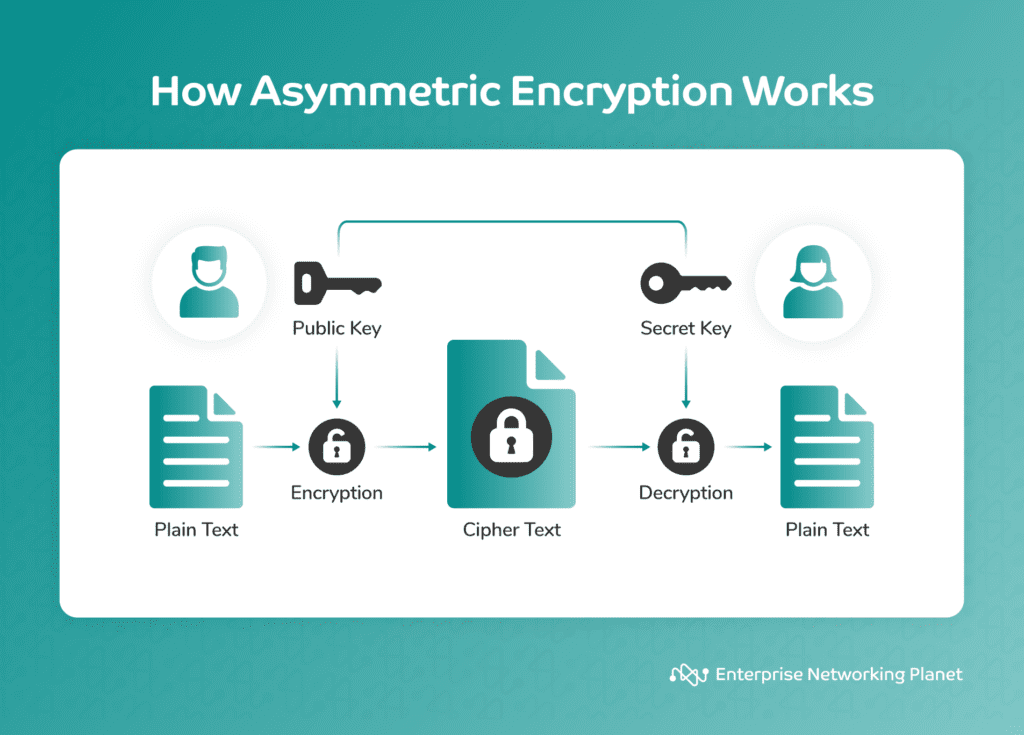
Asymmetric encryption, also referred to as public key encryption, employs two distinct keys: one for encryption, which is public, and another for decryption, which is private. Entities may use this encryption to protect data and key exchanges over open, insecure channels. They also use it to authenticate and ensure data integrity.
This encryption is slower and less effective compared to symmetric encryption, but offers heightened security due to the public key’s shareability while keeping the private key confidential.
When is asymmetric encryption used?
Asymmetric encryption is suitable for situations that require secure key exchange over an unprotected medium, like the internet. It finds common usage in secure email (PGP), secure websites (HTTPS), online transactions, and digital signatures.
This encryption provides a solution for two parties to communicate privately without the need to share a pre-established key.
Real asymmetric encryption examples
- Secure email communication: When you send an encrypted email using platforms like PGP (Pretty Good Privacy) or S/MIME (Secure/Multipurpose Internet Mail Extensions), you use asymmetric encryption. You use the recipient’s public key for encryption, and only their private key can decrypt the message.
- Digital signatures: Users leverage asymmetric encryption to generate digital signatures for documents or software. When you sign a document with your private key, others can verify its authenticity using your public key.
- Secure web browsing (HTTPS): When you visit a secure website with an “https://” URL, asymmetric encryption enables establishing a secure connection between your browser and the web server. This encryption actively secures the data transfer between you and the website.
- Secure Shell (SSH): SSH protocol uses asymmetric encryption to authenticate and secure remote logins and file transfers between computers. Authentication relies on the server’s public key, while data encryption involves generating a session key.
- Blockchain technology: Cryptocurrencies like Bitcoin and Ethereum employ asymmetric encryption for secure transactions and wallet management. Public and private keys are central to these blockchain systems.
Common encryption algorithms
Let’s look at the most popular encryption algorithms for symmetric and asymmetric encryption.
Symmetric encryption algorithms:
Symmetric encryption algorithms include AES, DES, 3DES, Blowfish, and Twofish.
Advanced Encryption Standard (AES)
AES is prevalent in secure communications, data storage, and various encryption tools. It uses block ciphers with key sizes of 128 bits, 192 bits, or 256 bits.
Used in:
- SSL and TLS protocols.
- Full-disk encryption for protecting the contents of hard drives and SSDs.
- File and folder encryption in operating systems like Windows and macOS.
- Encryption of sensitive data in databases.
Data Encryption Standard (DES)
Users widely relied on DES, a symmetric encryption standard, in the past. However, it has become less secure than AES and is vulnerable to brute-force attacks. It uses a 56-bit key, and most have replaced it with more secure algorithms.
Historically used in:
- Financial transactions and banking systems.
- Secure communication within government and military applications.
Triple Data Encryption Algorithm (3DES)
3DES is a more secure variant of DES. It applies the DES algorithm three times in succession with different keys, providing stronger encryption.
Used in:
- Older payment processing systems.
- Legacy banking applications that have not yet migrated to more modern encryption standards.
Blowfish
Various applications have used Blowfish, a symmetric-key block cipher known for its simplicity and speed. However, it’s less common today because more secure alternatives are available.
Used in:
- VPN protocols.
- Disk encryption software.
- Protected communication within some legacy systems.
Twofish
Some security-conscious applications have used Twofish, another symmetric-key block cipher, mainly as an alternative to AES. However, it did not achieve as wide adoption as AES.
Used in:
- Secure communication in certain VPN implementations.
- Sensitive data encryption in specific software and systems that prioritize security.
Asymmetric encryption algorithms
Asymmetric encryption algorithms include RSA, ECC, DH, ECDH, DSA, and EdDSA.
Rivest-Shamir-Adleman (RSA)
RSA is a widely used public-key encryption algorithm for secure data transmission. It relies on the mathematical properties of large prime numbers.
Used in:
- Secure email communication through technologies like S/MIME.
- Protected web communication and encryption of data transmitted over HTTPS (TLS/SSL).
- Digital signatures for authentication and data integrity in digital certificates.
- Key exchange in secure protocols such as SSH.
Elliptic Curve Cryptography (ECC)
ECC delivers strong security with relatively small key sizes, making it suitable for resource-constrained devices like smartphones.
Used in:
- Cryptocurrency and blockchain technologies (e.g., Bitcoin uses ECC for key management).
- Secure messaging applications.
- Mobile device encryption and secure communications.
- Internet of things (IoT) security.
Diffie–Hellman (DH)
This mechanism enables two parties to craft a shared secret key, even over an unsecured channel. This shared secret key forms the cornerstone of their secure communication.
Used in:
- Establishing shared secret keys in protocols like SSL/TLS for secure web communication.
- Protected email communication.
- VPNs for secure data transmission.
Elliptic Curve Diffie–Hellman (ECDH)
ECDH combines Diffie–Hellman with elliptic curve cryptography, offering reliable key exchange with strong security.
Used in:
- Private key exchange in encrypted messaging apps.
- Secure channel establishment in secure voice over IP (VoIP) applications.
Digital Signature Algorithm (DSA)
DSA is an asymmetric algorithm used for digital signatures to verify data authenticity and integrity.
Used in:
- Digital signatures in digital certificates for secure web communication (although it has been largely replaced by RSA and ECC for this purpose).
- Cryptographic authentication in certain government and military applications.
EdDSA (Edwards-curve Digital Signature Algorithm)
EdDSA is a more modern elliptic curve-based algorithm, known for its effectiveness and security in digital signature applications.
Used in:
- Cryptocurrency technologies, including the use of Ed25519 in some blockchain networks.
- Secure authentication and identity verification in private messaging and file sharing applications.
Bottom Line: When to use symmetric vs. asymmetric encryption
Symmetric and asymmetric encryption each play unique roles in data and network security.
Symmetric encryption excels in speed and efficiency, making it the go-to choice for encrypting large volumes of data and tasks like data storage and high-speed network communication.
Despite its slower speed, asymmetric encryption offers a robust security framework with its key distribution mechanism, proving essential for secure email, digital signatures, secure web browsing, and secure communications over untrusted networks.
The decision between symmetric and asymmetric encryption isn’t about which method is superior. Instead, it’s about choosing the right tool for the job to ensure optimal data security. This choice hinges on the specific security needs and operational requirements of a given system.
A well-designed security strategy might combine both encryption types to tackle diverse security challenges in the digital age. As security threats continue to grow, it becomes increasingly urgent to understand the strengths and weaknesses of these encryption methods. This understanding aids in making informed decisions about securing your organization’s sensitive information and communications.
Take the next step in your encryption journey and master encryption. Don’t miss out on our guide to the best encryption software to keep your data protected.



