Vulnerability management is a comprehensive process involving identifying, prioritizing, mitigating, and monitoring security weaknesses in your organization’s IT systems, applications, and infrastructure. It’s a proactive strategy to reduce risk and protect against cyberthreats.
A robust vulnerability management program leverages threat intelligence to swiftly address risks, ultimately working to minimize your organization’s overall risk exposure. Given the constantly evolving threat landscape and ever-changing environments, continuous vulnerability management is not just beneficial but imperative.
By applying vulnerability management along with other security measures, you can maximize protection on your network. It helps you identify and rank the most likely threats and reduce their exposure to attacks.
Table of Contents
Why is vulnerability management important?
Vulnerability management is critical to network security because it empowers you to protect your organization from a variety of digital threats, including data breaches, unauthorized access, and system compromises.
The consequences of data breaches can be severe, including financial losses, operational disruptions, damage to trust and reputation, and legal issues. Businesses rely on various software solutions to maintain competitiveness, but these are prone to vulnerabilities. Neglecting vulnerability management can result in these consequences.
How vulnerability management works
Vulnerability management works by following a process that protects organizations from different types of cyberattacks. This process has four steps: identification, assessment and prioritization, remediation, and monitoring.
4 steps of the vulnerability management process
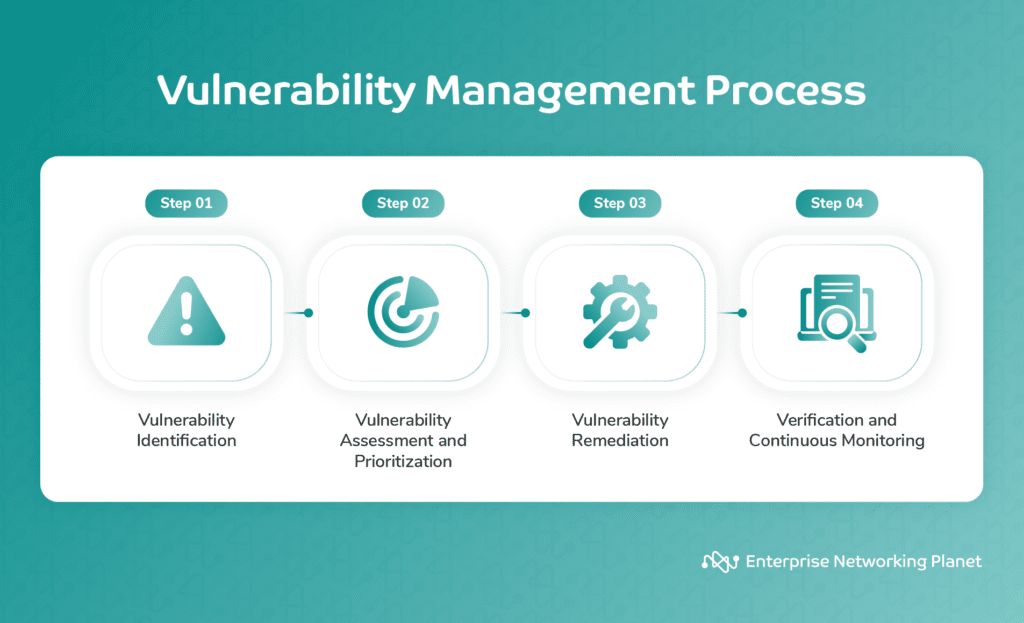
1. Identification
This step consists of discovering vulnerabilities in software, configurations, and network devices using automated scanning tools or manual methods.
2. Assessment and prioritization
In this step, analyze any identified risks based on their severity, potential impact, and likelihood of exploitation using various data sources, such as business, exploitation, threat, and risk data. You can use this information to rank vulnerabilities and determine which ones should be addressed first.
Prioritize vulnerabilities based on their urgency and importance using a scoring system or a matrix. This will help you focus on the most urgent issues first and avoid overlooking serious threats.
3. Remediation
Next, you’ll want to develop and implement solutions to fix vulnerabilities, such as applying patches, reconfiguring systems, or adding more security controls. This step may also include testing the effectiveness of the software and verifying that the vulnerabilities are resolved.
4. Monitoring
Finally, monitor new vulnerabilities and emerging threats using continuous scanning tools or periodic reports. This helps you stay vigilant and adjust to the ever-changing cybersecurity landscape.
Components of vulnerability management
Vulnerability management employs a variety of tools and solutions to prevent and address cyberthreats. A reliable vulnerability management software typically includes tools for conducting vulnerability scans, discovering and inventorying assets, managing patches, configuring systems, overseeing security incidents and events, performing penetration tests, utilizing threat intelligence, and conducting risk assessments.
Vulnerability scanning
Vulnerability scanners identify various systems in a network, including laptops, desktops, servers, databases, firewalls, switches, and printers. It probes them for specific attributes like OS, open ports, software, user accounts, file structures, and configurations.
Scanners use a database of known vulnerabilities and exploits to associate vulnerabilities. They conduct tests to uncover weaknesses, such as exploiting known vulnerabilities, guessing passwords, or accessing restricted areas.
However, vulnerability scanners aren’t perfect; they have low but nonzero false-positive rates. You can use penetration testing to filter out false positives to address this and focus on real vulnerabilities.
Asset discovery and inventory
Asset discovery and inventory are the bedrock of vulnerability management. They present the context and data necessary for vulnerability scanning, risk assessment, prioritization, and remediation efforts. Without an accurate and up-to-date inventory of assets, your vulnerability management process would be incomplete and less effective at addressing security risks.
Patch management
Patch management software helps your network and systems stay secure by automatically applying software updates. This helps to protect against vulnerabilities and data breaches.
Configuration management
Security configuration management (SCM) software secures devices by tracking and approving changes and ensuring compliance with security policies. It can also scan for vulnerabilities, track remediation, and generate reports.
Security incident and event management (SIEM)
Security incident and event management (SIEM) software collects and analyzes security logs and events in real-time. It provides you with visibility into their entire digital estate, including IT infrastructure, network traffic, and user activity.
Penetration testing
Penetration testing (or pentesting) serves a significant role in vulnerability management by identifying and exploiting vulnerabilities to aid you in discovering weak points that real-world attackers could potentially target.
Threat intelligence
Threat protection software allows you to track, monitor, analyze, and prioritize potential threats. It collects data from multiple sources, including network traffic, email, and endpoint devices, to identify trends and patterns that could indicate a future security breach or attack. You can then use this data to create alerts and notifications so that you can take action to mitigate the threat.
Risk assessment
Risk assessment lets you evaluate the potential impact and likelihood of vulnerabilities, and ultimately prioritize which vulnerabilities to address based on their potential risks.
What is vulnerability lifecycle management?
While the vulnerability management process represents the broader concept of managing vulnerabilities, the vulnerability management lifecycle offers a structured methodology for executing the process effectively, ensuring consistency and repeatability in vulnerability management practices. This lifecycle includes phases for discovery, asset prioritization, vulnerability assessment, reporting, remediation, and verification.
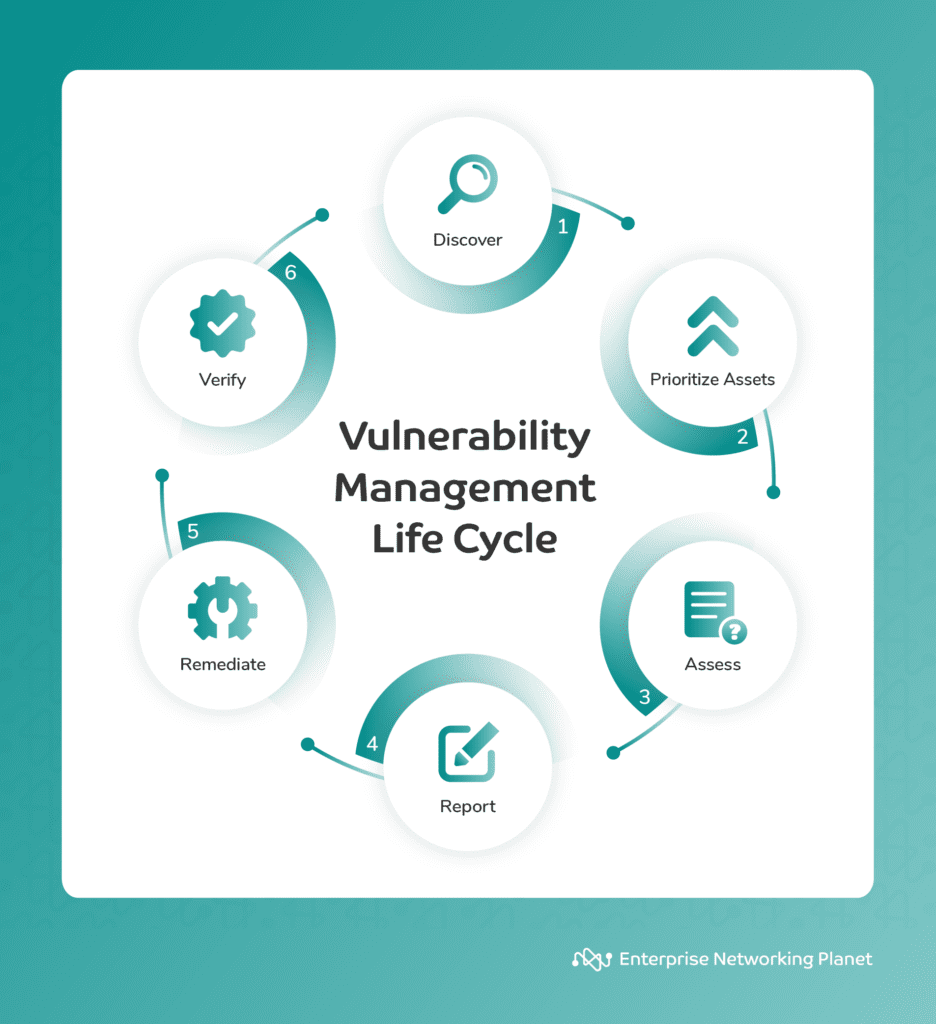
Discovery
This phase comprises identifying and cataloging all the IT assets in your network, such as servers, workstations, devices, applications, and databases. It facilitates creating an inventory of assets and their attributes, such as OS, software version, IP address, and owner. This step also covers scanning the assets for known vulnerabilities using tools like vulnerability scanners or agents.
Asset prioritization
Asset prioritization is the process of ranking your assets based on their significance and value. This helps to identify which assets are most at risk of being targeted by attackers or causing the most damage if compromised. It’s good to consider the following factors when prioritizing assets:
- Criticality: How important is the asset to your organization’s operations?
- Sensitivity: How sensitive is the asset to unauthorized disclosure?
- Exposure: How vulnerable is the asset to attack?
- Likelihood of exploitation: How likely is the asset to be targeted by attackers?
Once you’ve prioritized these assets, you can protect them accordingly.
Assessment
During the assessment phase, security experts evaluate vulnerabilities to determine their severity, impact, and risk level. This evaluation aids in prioritizing the vulnerabilities and deciding which ones to address first. It is also crucial in the assessment stage to use various data sources, such as business information, exploitation data, threat intelligence, and risk information, to examine the vulnerabilities.
Reporting
This step involves documenting and communicating vulnerability assessment results to the relevant stakeholders, such as management, IT staff, or auditors. It heightens awareness and accountability for the vulnerabilities and their remediation. Reporting also includes offering recommendations and guidance on vulnerability mitigation or resolution.
Remediation
Remediation entails taking action to fix or mitigate the vulnerabilities found in the previous steps. This may include applying patches, updates, or configuration changes, installing security software or hardware, or removing or isolating vulnerable assets. This step aims to improve your security posture and reduce your attack surface.
Verification
The verification stage ensures the resolution of vulnerabilities and compliance with security standards and regulations. During this phase, you can confirm whether the corrective measures have been successful and have not introduced any new vulnerabilities or issues. This phase includes activities like rescanning assets, testing the functionality and performance of systems, and conducting audits or reviews.
7 benefits of vulnerability management
Implementing vulnerability management brings several benefits, including better security posture, decreased risk of cyberattacks, regulatory compliance, visibility and reporting, increased efficiency, cost savings, competitive advantage, and proactive defense.
Better security posture
Vulnerability management helps you identify and fix security risks before attackers can exploit them. You can make systems more secure by regularly vulnerability scanning and patching them.
Reduced risk of cyberattacks
Automated patch management identifies and fixes vulnerabilities promptly, reducing the risk of cyberattacks. By prioritizing and fixing vulnerabilities, you can protect data and systems. Some real-time vulnerability management solutions and vulnerability management as a service (VMaaS) providers perform integrated patch remediation, automating the remediation of recurring network vulnerabilities. This also optimizes the utilization of resources on new vulnerabilities.
Regulatory compliance
Effective vulnerability management enhances compliance with various security standards and regulations while providing valuable insights into your security risk posture and areas that need improvement. Compliance frameworks, such as the Payment Card Industry (PCI) and the Health Insurance Portability and Accountability Act (HIPAA), require some organizations to establish a vulnerability management program.
Increased efficiency
Businesses can minimize system downtime, protect data, and recover from incidents faster by understanding and mitigating security risks. Assessing vulnerabilities helps IT security experts prioritize remediation efforts and eliminate confusion. Furthermore, automating vulnerability management reduces the burden of ownership and maintenance, saving time and increasing efficiency.
Cost savings
Proactively addressing risks through successful vulnerability management is often significantly more cost-effective than dealing with the aftermath of a security breach, which can involve legal fees, fines, and reputation damage.
Competitive edge
A strong security posture and commitment to vulnerability management can help your organization stand out from the competition, build trust with customers and partners, and preserve its reputation.
Proactive defense
Vulnerability management allows you to be proactive in addressing potential threats and risks, reducing the need for reactive, less effective measures.
Vulnerability management best practices
Following vulnerability management best practices substantially lowers the risk of security incidents. Some of these practices include conducting regular vulnerability scans, prioritizing vulnerabilities, using automated tools, administering penetration testing, developing remediation plans, deploying security patches, and monitoring.
Perform regular vulnerability scans
The initial step in vulnerability management is to execute frequent vulnerability scans of your organization’s IT infrastructure. This will assist you in identifying any vulnerabilities that exist in your infrastructure. You can perform both internally and externally and on a regular basis.
Prioritize vulnerabilities
After conducting a vulnerability scan, you should rank the discovered vulnerabilities. This is important because not all vulnerabilities are equally serious. You should prioritize vulnerabilities based on the potential impact they could have on your organization.
Develop a remediation plan
After prioritizing the vulnerabilities, the next step involves developing a remediation plan. This plan must establish a timeline for addressing each vulnerability. It should also outline steps for testing and validating the fixes applied to the vulnerabilities. It’s vital to update the remediation plan as new vulnerabilities emerge and as new information becomes available about existing vulnerabilities.
Conduct penetration testing
Pentesting involves simulating an attack on an enterprise’s digital infrastructure to discover vulnerabilities. This technique can help uncover weaknesses that regular vulnerability scanning may not detect. Regular penetration testing is necessary to ensure the sufficiency of your security.
Apply security patches
Applying security patches promptly upon release by the software vendor is a crucial aspect of vulnerability management, as any delay in their implementation can expose your organization to potential attacks.
Monitor and review
Vulnerability management is an ongoing process that requires regularly monitoring systems and applications to detect new vulnerabilities and continually reviewing the vulnerability management process to pinpoint areas for enhancement.
Have a well-defined vulnerability management policy
The vulnerability management policy serves as a guiding framework, outlining the procedures, responsibilities, and standards for identifying, prioritizing, and remedying vulnerabilities within your organization. Enforcing a well-defined policy not only streamlines the vulnerability management process but also boosts your ability to proactively safeguard its digital assets against emerging cyberthreats.
Vulnerability management vs. vulnerability assessment
While both vulnerability management and vulnerability assessments are related to identifying and addressing the weaknesses in the IT environment, there are some key differences between them.
| Vulnerability assessment | Vulnerability management |
|---|---|
| Identifies and catalogs vulnerabilities. | Encompasses the entire vulnerability lifecycle. |
| Conducted at specific intervals (e.g., monthly or quarterly). | Ongoing and dynamic process. |
| Generates a list of vulnerabilities with risk ratings. | Offers a structured approach for remediation, progress tracking, and reporting. |
| Does not directly involve remediation or mitigation. | Actively involves mitigation and remediation efforts. |
| Delivers a point-in-time snapshot of the security posture. | Includes continuous monitoring and adaptation to evolving threats. |
| Typically uses automated scanning tools. | Incorporates vulnerability assessment as a part of the process. |
| Provides insights for further action. | Aims to reduce security risks and enhance overall cybersecurity posture. |
Patch management vs. vulnerability management
Patch management is an important element of the vulnerability management process. While both are integral to strong cybersecurity, they serve distinct roles.
| Patch management | Vulnerability management |
|---|---|
| Focuses on deploying patches to existing software. | Proactively identifies and mitigates vulnerabilities. |
| Reactive, responding to patch releases. | Involves vulnerability scanning, assessment, and remediation. |
| Limited scope to specific patching. | Broader scope across the entire IT environment. |
Top 3 vulnerability management solutions
There are many vulnerability management solutions available today, each with its own set of features. Some of the top solutions in 2023 are ManageEngine Vulnerability Manager Plus, Microsoft Defender Vulnerability Management, and Qualys Vulnerability Management (VMDR).

ManageEngine Vulnerability Manager Plus
ManageEngine Vulnerability Manager Plus is a one-stop shop for vulnerability management and compliance. It helps organizations of all sizes identify, assess, and remediate vulnerabilities across their IT infrastructure.
With its attacker-focused analytics, Vulnerability Manager Plus can identify the most critical vulnerabilities and help you prioritize remediation efforts. It also strengthens web servers, audits high-risk software, and addresses zero-day vulnerabilities. It does all of this through a single console, equipping you with comprehensive coverage, visibility, assessment, and threat remediation.
Microsoft Defender Vulnerability Management
Microsoft Defender Vulnerability Management uses risk-based scanning to identify and prioritize vulnerabilities. It gives real-time insights into software, certificates, hardware, and browser extensions. It also offers security recommendations and application-blocking capabilities.
It is worth noting that Microsoft Defender Vulnerability Management, while a powerful tool, can be difficult to set up. Nevertheless, its compatibility with a wide range of operating systems, including Windows, macOS, Linux, Android, iOS, and network devices, ensures its adaptability. Additionally, regular updates continuously advance its capabilities.

Qualys Vulnerability Management (VMDR)
Qualys VMDR is a comprehensive vulnerability management solution that streamlines the entire vulnerability management process, automating asset identification, risk-based assessments, and remediation actions. While it provides visibility for prioritizing vulnerabilities and assets based on business risk, some users may find its interface overwhelming.
However, despite its complexity, Qualys VMDR excels in integration. It seamlessly connects with configuration management databases (CMDBs), patch management systems, and IT service management (ITSM) solutions, ensuring a smooth and scalable remediation process. This adaptability extends to hybrid and multi-cloud environments, as well as containerized and serverless applications, making it a versatile choice for securing diverse IT assets.
Bottom line: Vulnerability management is key to a strong cybersecurity posture
Vulnerability management plays a pivotal role in establishing a robust cybersecurity posture. It ensures you can proactively identify and address potential weaknesses in your organization’s digital defenses. The vulnerability management process is complex but essential in securing your network and safeguarding your organization against cyberattacks.
By following the tips in this guide, you can take steps to bolster your defense and reduce the risk of a successful attack.
Ready to choose a vulnerability management software? Take a look at our rundown of the best vulnerability management solutions currently available.



