As remote work continues to solidify its presence in our modern-day business environment, organizations are confronted with the critical task of providing secure access to internal network resources such as applications, databases, and servers for their remote workforce.
While traditional methods relied heavily on virtual private networks (VPNs) for remote connectivity, a growing trend towards zero trust network access (ZTNA) solutions is reshaping the landscape of secure network access. While both ZTNA and VPNs offer secure remote access, they differ in various aspects, making them suitable for different use cases.
So, which of these network access methods should you go for? This comparison piece will help you find out.
- VPNs: Best for providing versatile remote access to corporate resources and enabling connectivity across multiple locations.
- ZTNA: Best for implementing a zero-trust security model with granular access controls that ensure enhanced security for organizations prioritizing data protection.
Table of Contents
What’s the difference between ZTNA and VPNs?
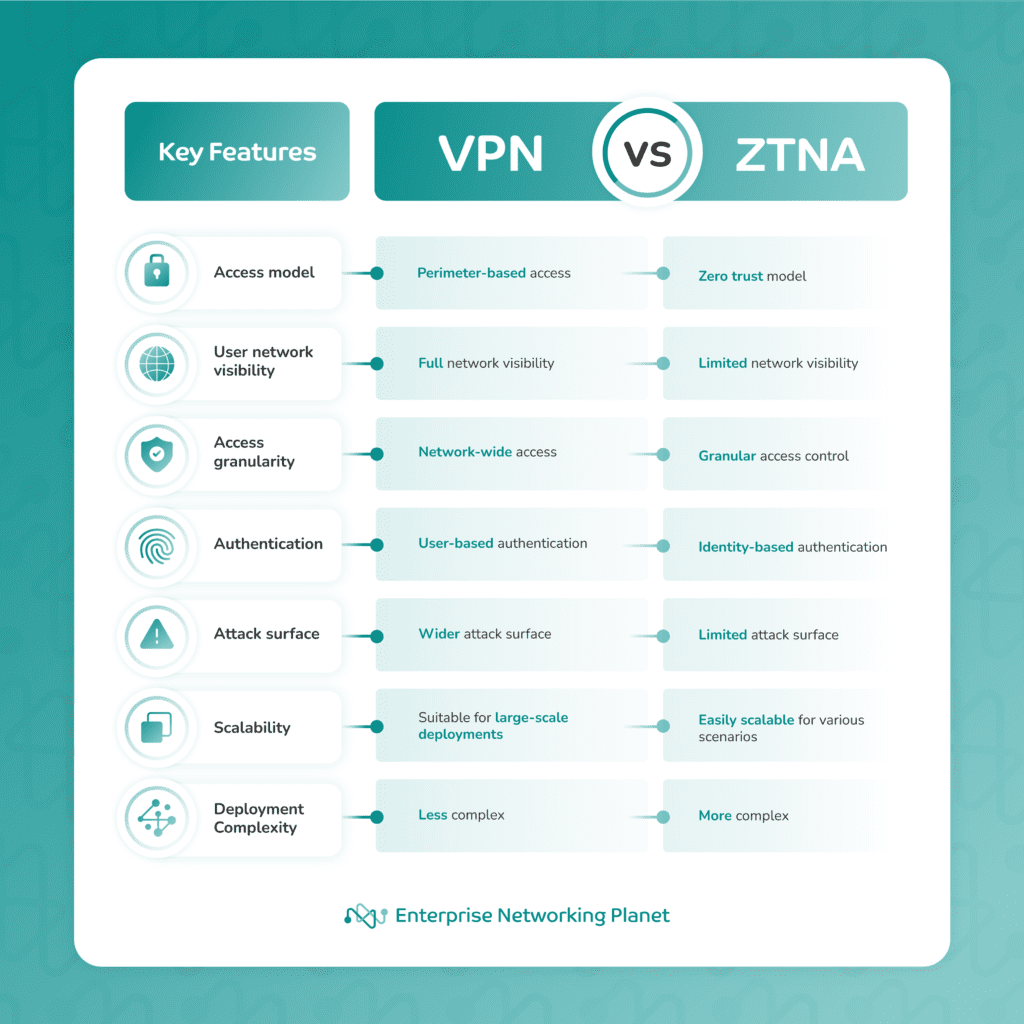
ZTNA provides individualized access to specific organizational resources, while VPNs grant remote users access to an entire network. To help you understand their differences, here is a quick comparison chart summarizing the key features.
What is a virtual private network (VPN)?
A VPN is a security solution that establishes a secure connection between the user’s device and the corporate network over the public internet. It creates an encrypted tunnel that protects data transmission from unauthorized access and interception.
VPNs have been widely used to provide versatile remote access, allowing employees to connect to their organization’s resources from anywhere, even outside the office premises.
Advantages of VPNs
- Versatile remote access: VPNs allow users to securely connect to corporate resources from anywhere.
- Enhanced privacy: VPNs encrypt data, protecting it from unauthorized access.
- Network-wide access: Users can access resources across the entire corporate network.
- Compatibility: VPNs work on various devices and operating systems.
Disadvantages of VPNs
- Trust-based model: Once inside the network, users are trusted to access any resources they encounter, which can present a security risk.
- Network performance impact: VPNs can introduce latency and reduce network speeds.
- Full network visibility: Users have visibility into the entire network, potentially exposing sensitive components.
What is zero trust network access (ZTNA)?
ZTNA is a security framework that focuses on maintaining strict access controls based on user identity and other contextual factors. Instead of granting network-wide access, ZTNA follows the principle of “verify first, access later.”
ZTNA represents a more modern approach to network security and operates under a zero trust model, where user access is granted on a per-session and per-application basis. Instead of relying solely on network perimeter security like VPNs, ZTNA emphasizes identity-based authentication, granular access controls, and continuous monitoring.
This approach aims to minimize the attack surface and mitigate potential risks by only granting access to authorized users based on their identity, device health, and other parameters, such as time of access, device type, and network conditions.
Advantages of ZTNA
- Zero trust security: ZTNA follows a strict authentication and access control model, reducing the attack surface.
- Granular access control: ZTNA allows for fine-grained access based on user identity and several other parameters.
- Reduced exposure: Users only see and access the specific resources they need.
- Compliance readiness: ZTNA helps organizations meet regulatory requirements with strong access controls.
Disadvantages of ZTNA
- Implementation complexity: Setting up ZTNA requires configuration and integration efforts, especially in complex environments.
- Scalability challenges: Scaling ZTNA for diverse access scenarios can be complex.
- Identity management dependency: ZTNA heavily relies on identity management systems for accurate user authentication.
- Impact on user experience: ZTNA may affect user experience and increase frustration due to additional authentication steps and checks.
- Cost: ZTNA adoption can be costly, especially for organizations with limited budgets.
Who should use ZTNA vs. VPNs?
Both ZTNA and VPNs offer great security options. The answer to which one you should go for at your organization depends on your specific budget, needs, and infrastructure.
Who should use ZTNA?
- ZTNA is a great option for enterprises with a lot of critical data and applications that require user-centric access controls — and have the IT resources to support them.
- ZTNA’s identity-based authentication and granular access controls make it an excellent choice for companies with distinct user groups using different apps and resources.
- If your employees primarily work remotely and require secure access to specific resources, ZTNA provides a more tailored and secure solution.
Who should use VPNs?
- VPNs offer network-wide access, making them suitable for companies with multiple departments and sites that need seamless connectivity across the entire network.
- If you have a lot of remote employees who need access to a wide range of resources and services across the network, VPNs allow for unrestricted access.
- VPNs are a great option for smaller businesses with few employees, since they’re easy to set up and scale with your business.
ZTNA and VPN: You don’t have to choose
While choosing either a VPN or ZTNA to protect your business’s network will be sufficient for many organizations, those looking to take the next step in network security may want to combine the two solutions.
Companies like Array Networks offer SSL VPNs based on zero trust principles, with granular controls so IT can secure access at the endpoint while providing specific, role-based permissions across the network. These sorts of dual solutions — also offered by ExpressVPN and Fortinet, among others — are ideal for businesses with enterprise-wide remote access needs, or for cloud service providers looking to offer the widest range of access options for their customers.
As business security needs continue to grow both more complex and stringent, expect to see more of these combined ZTNA VPN solutions appearing on the market.
Bottom line: Choosing between VPN and ZTNA for your network
Understanding the differences between ZTNA and VPNs is crucial before making any decisions about switching.
While VPNs have been around for many years, ZTNA represents a modern security approach under the zero trust model. ZTNA’s emphasis on identity-based authentication, granular access controls, and limited network visibility can significantly enhance security, minimize the attack surface, and better protect against evolving cyber threats.
Although both solutions have their merits, ZTNA stands out for organizations that prioritize robust security and have a lot of sensitive data to deal with. On the other hand, a VPN is ideal for organizations with less sensitive data and lower security risks, as well as organizations that want to provide full network access to their remote users.
Whichever solution you choose to go with, we’ve got you covered: read our guide to the best VPN services and the best ZTNA solutions available today.



