Classless Inter-Domain Routing (CIDR) is an IP addressing system that replaced the previous system of using Class A, B, and C networks. CIDR was developed to help alleviate the shortage of available IP addresses by allowing more efficient address allocation using more unique and granular identifiers for networks and individual devices.
To break that down into a simpler explanation, think of IP addresses as home addresses. Just like how you have a house address to receive mail, computers need IP addresses to communicate with each other.
Before CIDR, IP addresses were assigned in groups called classes. It was like having a house address that was only 3 digits long. This meant that there were a very limited number of addresses available.
CIDR is like having a house address that is 10 digits long. This means that there are more house addresses available and they can be assigned with more efficiency and specificity.
Table of Contents
What’s the purpose of CIDR?
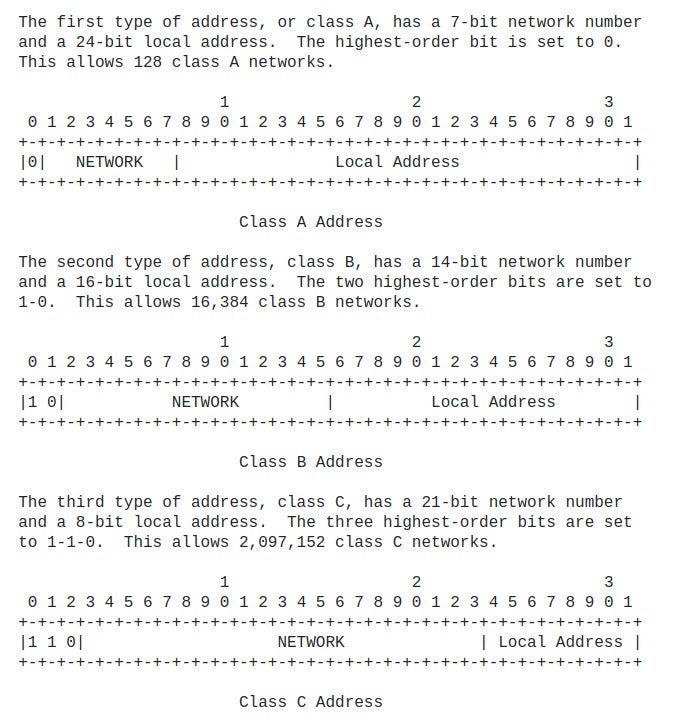
In 1993, CIDR was released as a solution to the looming scarcity of IPv4 addresses. By allotting to networks more precise and nuanced CIDR blocks that consume fewer resources, CIDR has been able to extend the lifespan of this precious resource. It replaced the now obsolete classful network system based on classes A, B, and C as summarized in IETF’s rfc943:
Disadvantages of the classful system
The classful system, while well suited to its time, had drawbacks that outdated it quickly, including inefficiency, poor structure, routing issues, and lack of scalability.
1. Inefficiency
The classful system was inefficient in terms of the number of addresses it allocated. It was also inflexible: with only three sizes available, it did not allow networks to be easily changed or split up.
CIDR solves these issues by making it easier to divide and allocate IP addresses more efficiently.
2. Structuring
When CIDR is used, an IP address may contain a prefix which describes the network and a suffix which describes a particular device or host on that network.
CIDR also allows for CIDR blocks, which are defined as a certain number of IP addresses that can be allocated to a single organization.
Classful IP addresses didn’t allow either of these options.
3. Routing issues
The classful system necessitated that each independent network be listed on its own, forming larger routing tables.
To combat this problem, CIDR devised a notation plan to group networks together, significantly reducing the entries on these large routing tables.
4. Lack of scalability
Soon after the introduction of the Domain Name System (DNS), the classful system quickly became untenable because of the sheer size and scale of the internet.
CIDR solved this problem by allowing specific CIDR blocks to be allocated efficiently throughout the internet, improving scalability.
How CIDR works
By employing CIDR notation, administrators can aggregate networks in a way that minimizes the number of entries in a routing table. This method involves assigning CIDR blocks to organizations and subdividing these blocks into smaller, more manageable segments. As a result, IP addresses can be dynamically allocated to users based on specific rules and requirements.
The Internet Assigned Number Authority (IANA) shoulders the responsibility of managing CIDR block assignments. In this manner, CIDR streamlines the process of allocating IP addresses dynamically according to pre-established guidelines, ensuring a more organized and efficient system for network administration.
CIDR structuring
CIDR is structured using blocks containing prefixes, suffixes, and route notation.
Blocks
CIDR blocks are defined as a certain number of IP addresses that can be allocated to a single organization. CIDR blocks are divided into smaller chunks, which makes it easier to divide and allocate IP addresses more efficiently.
Prefix/suffix
CIDR blocks are denoted by the prefix and suffix. The prefix indicates the network and the suffix indicates a particular host within that network.
Notation
CIDR notation pairs an IP address with a specific network mask. For instance, consider the following format: 192.168.129.23/17—where 17 reflects how many bits are in the address itself.
IPv4 addresses can include up to 32 of these bits, while IPv6 is more extensive and permits 128 possible bit combinations. Put simply, CIDR provides you with maximum control over routes between your computers and networks.
Subnet masks
CIDR is an efficiency-oriented system rooted in the concept of subnet masks. These 32-bit numbers act as a filter for IP addresses, logically partitioning them into network and host portions that enable devices to quickly discern how best to communicate with one another. With this efficient division of elements, data can be swiftly transferred between hosts without confusion or delay.
CIDR is an alternate method of representing a subnet mask and is made up of the binary representation of the network address followed by a slash and a suffix that declares the total number of bits reserved that need to be matched in the address.
What does a CIDR address look like?
A CIDR address consists of two parts: the prefix and the suffix. The prefix is the network address. It’s followed by a slash and the suffix which denotes the CIDR block size in bits.
For example, if you have an IP address of 192.168.1.1 and a subnet mask of 255.255.255.0, the CIDR notation would be 192.168.1.1/24. The /24 indicates that the first 24 bits of the IP address are used for the network address, and the remaining 8 bits are used for the host address.
The CIDR address can be written in IPv4 or IPv6 notation. For example 192.168.1.0/24 for IPv4, or 2001:db8::/32 for IPv6.
2 examples of CIDR conversion
Converting CIDR addresses to IP addresses and vice versa is quite simple; however, certain rules need to be followed when doing so. For example, CIDR notation must have a suffix (the CIDR block size) between 0 and 32 for IPv4 addresses and 0 to 128 for IPv6 addresses.
There are two primary means of converting IP addresses to CIDR: subnetting and supernetting.
Subnetting
Subnetting is the process of dividing a network into smaller subnetworks to improve network performance and security.
Subnetting is done by borrowing bits from the host ID portion of the IP address. For example, if you have a Class C network address of 192.168.1.0 and you want to create 4 subnets, you would borrow 2 bits from the host ID portion of the IP address. This would give you 4 subnets, each with 64 hosts.
Supernetting
Supernetting, otherwise known as route summarization or route aggregation, is a method of condensing numerous contiguous subnets into one large network. This process is completed by carefully selecting bits from the IP address network ID portion to generate an aggregated representation.
For example, if you have 8 subnets, you can summarize them into a single subnet by borrowing 3 bits from the network ID portion of the IP address. This would give you a single subnet with 8 subnets, each with 256 hosts.
An example of a practical application of this would be when a company wants to turn several office locations with corresponding routers into one super network.
Featured IT Software
Bottom line: Using CIDR in enterprise networks
CIDR’s original purpose was to regulate the growth of routing tables on routers around the world and reduce their size. It has exceeded expectations. In addition to minimizing router table sizes, it has helped boost security and enhance scalability and performance. Long after its initial intent was fulfilled, CIDR remains an indispensable instrument for network administrators today.
Keep your corporate network in peak performance with one of the best enterprise Wi-Fi solution providers on today’s market.






