Code42 is a Minneapolis-based cybersecurity software company specializing in insider risk management. It was founded in 2001 as an IT consulting company before transitioning into a cybersecurity company. Code42 provides a data loss prevention (DLP) service that helps companies automatically identify and protect their sensitive information.
Bottom Line
Incydr and CrashPlan are two cloud-based data protection systems created by Code42. With Code42 DLP, employees can collaborate in real time on confidential documents and store files safely in appropriate locations without interrupting productivity. Through encryption, policy enforcement and automatic auditing, Code42 DLP’s flexible platform ensures end-to-end protection of your most critical company data across physical, virtual, or hybrid environments.
Key Features
Detection
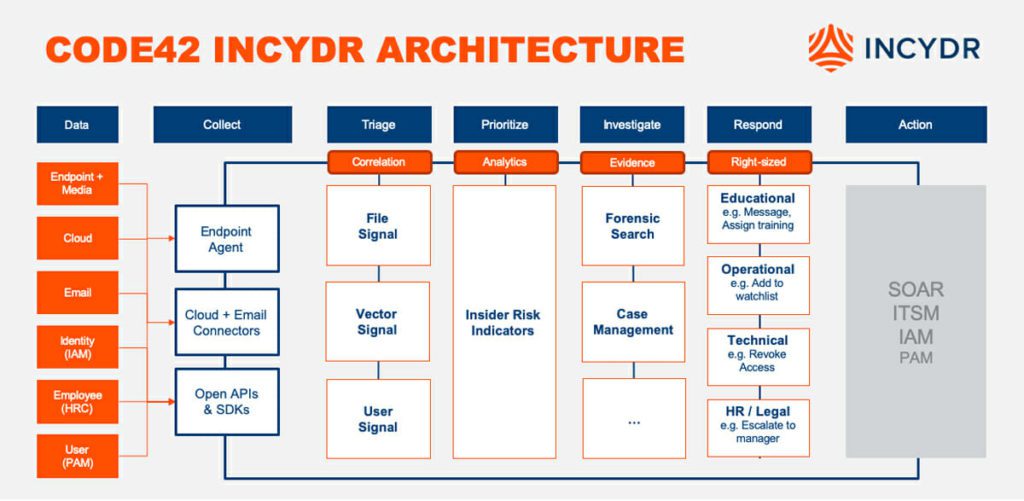
Insider risk may be reduced by using file, vector, and user signals. Incydr identifies data security threats on PCs, in the cloud, and through email. All file activity on corporate Mac, Windows, and Linux machines is continually monitored by an agent. It has three major categories: risk exposure dashboard, risk detection lenses, and high-fidelity alerts.
Investigation
Investigate data exposure and exfiltration incidents as soon as possible. Incydr provides simple investigative procedures and thorough information to help you identify and react to risk rapidly. It is composed of three layers: user profiles, forensic search, and security information and event management (SIEM) integrations.
Response
Take action on insider risk incidents with a reaction that is appropriate for your business. With Incydr flows, you can contain current data breaches, reduce time to resolution, use education to prevent future data leaks, and trigger reaction controls.
Incydr enables teams to effectively mitigate exfiltration risks and file exposure while maintaining the integrity of legitimate collaborations. Additionally, it may be used to keep track of numerous file operations such as creation, modification, migration, and deletion.
Also read: Data Loss Prevention (DLP) Best Practices & Strategies
Code42 Incydr
Code42’s Incydr is a SaaS data risk detection and response solution. Enterprise security teams can use Incydr to identify and react to insider risks to data that might lead to data leaks, data loss, and insider threats.
Using Incydr
The Risk Exposure dashboard
Incydr enables enterprises to distinguish between harmless usage of private accounts and potentially harmful activity, such as copying a file from the company’s computer for malicious purposes. The risk exposure dashboard gives Code42 visibility into who is accessing what, and if an employee appears to be copying sensitive data to a high-risk device or location, that event can be investigated further with targeted email notifications or monitoring tools.
The tool also provides reports about which employees have accessed data via unmanaged devices or from countries that are considered risky from a compliance perspective.
Departing Employee Lens
With the departing employee lens, you can get detailed information about recently departed employee accounts without disrupting day-to-day workflows or draining your resources. This feature is a great way to make sure that a former employee’s account is properly closed while also making sure important company data remains secure. The result is increased visibility into users who are transitioning out of an organization. It enables IT professionals to enforce data retention policies, ensure GDPR compliance, or protect against malicious behavior by investigating all file activity on endpoint devices.
Endpoint File Activity
The ability to detect a file’s endpoint location means instant visibility into which users are transferring data—from a hard drive to a removable disk or from a home computer onto a work machine—or even sharing data with employees who have no authorization to access it. This provides unprecedented control over your most sensitive corporate assets. Further, since you can set policies based on role, department, location, device type, etc., you know exactly how much each person is accessing company information.
User Profile
The user profile contains basic employee details and designation, as well as their activities. It displays four major categories:
- File activity by destination
- File activity by file category group
- Endpoint file activity
- Cloud file activity
Also read: Data Loss Prevention: Forcepoint vs. Symantec
Code42 CrashPlan for Small Business
CrashPlan is a cloud backup and recovery software for small businesses. CrashPlan automates the process of backing up data to remote servers or hard drives. With CrashPlan, data is encrypted, password-protected, and stored in a proprietary format.
Code42 DLP Use Cases
- Data exfiltration: An Incydr data risk detection and response solution that enables security teams to efficiently manage file exposure and exfiltration threats without interfering with team collaborations.
- IP theft: It helps in the prevention of intellectual property theft when enterprise assets are endangered by associating three risk dimensions: files, vectors, and users.
- Departing employees: Code42 links three aspects of risk associated with files, vectors, and users in order to identify and react promptly and correctly when employees try to steal data as they leave.
- Remote workforce: When employees work from home, it provides you the visibility you need to reduce data risk.
- High-risk employees: To classify and alert personnel, Incydr may be integrated with your identity management, HR, or other systems. A few of the risks to consider include flight risk, elevated access privileges, and performance concerns among others.
- Contractors: Identify and react to data security threats posed by contractors, interns, and other temporary employees as well as permanent staff.
- Shadow IT: Discover unauthorized programs used by workers to transfer or exfiltrate data.
- Security policy validation: Identify data security blindspots that expose you to insider risk.
Supported Platforms
Code42’s Incydr is a SaaS solution with open APIs and many pre-built integrations.
- Operating Systems: Windows, Mac, Linux
- Cloud Services: Microsoft OneDrive, Google Drive, Box
- Email: Microsoft Office 365 and Gmail
Pricing/License
Licensing packages start at 500 users. There is no pricing detail available for Code42 Incydr. However, you can contact the sales team for quotes tailored to your company’s needs.
Code42 Incydr Data Loss Prevention Summary
| Vendor | Code42 |
| Title | Incydr |
| Company website | www.code42.com |
| Category | Data Loss Prevention, and Backup |
| DLP features | Threat Protection Policy Management Incident Management Sensitive Data IdentificationData BackupData Leak Detection |
| Deployment type | SaaS/Web/CloudInstalled—WindowsInstalled—MacInstalled—Linux |
| Customer type | Large EnterprisesMedium BusinessSmall Business |
| Pricing model | Quote-based |
| Integration & deployment with other apps | Yes |
| API availability | Yes |
| DLP advanced detection | Yes |
| Data management | Yes |
| Reporting | Yes |
| Breach detection | Yes |
As cyber-attacks escalate and security breaches become more commonplace, it has never been more important to safeguard enterprise data. By ensuring control over all aspects of DLP—from policy creation to deployment—Code42 DLP not only protects your organization from inadvertent exposure but also provides an optimal level of governance for day-to-day file management within your business.



