Network Access Control (NAC) solutions are network security and privacy solutions designed to reduce risks and improve performance. Businesses use NAC to enforce policies on the devices that can access the network.
NAC technologies typically use a combination of hardware, software, and policy to control access to a network. However, cloud NAC has also become increasingly popular. Policies may be based on authentication, endpoint configuration (posture), or users’ role/identity.
There are two main reasons why NAC solutions are trending. First, the digital surface has expanded with a significant number of new devices connecting to networks, such as IoT, Industrial IoT, and Bring-Your-Own-Device (BYOD). Secondly, organizations must respond with solid security technologies against the global wave of sophisticated cyberattacks and malware network spread.
Here are our top picks for NAC solutions in 2023:
- Cisco Identity Services Engine (ISE): Best for large enterprises with advanced requirements
- Forescout Platform: Best for organizations with user and device diversity
- Aruba ClearPass: Best for small and medium-sized businesses (SMBs)
- Fortinet FortiNAC: Best cloud-based NAC solution
- Extreme Networks ExtremeControl: Best for integrating NAC solutions to existing infrastructure
Table of Contents
Top Network Access Control (NAC) software comparison
Several features are essential to all NAC solutions. When choosing a vendor, businesses must evaluate features offered against their operational needs to determine whether the technology fits.
From policy enforcement to user profiling, vulnerability scanning and customer support and pricing, find below a comparison chart to help you choose the best NAC solution for your enterprise.
| Policy enforcement and session control | Vulnerability scanning and malware detection | Scalability and integration | User profiling and reporting | Customer support | Licensing and pricing | |
| CISCO ISE | Advanced: Provides compliance | Advanced: Some components have an extra cost | Easy to scale and integrate | Advanced | 24/7/365: Support via web, email, chat, and phone | Complex licensing. Prices available upon request |
| Forescout | Good: Provides compliance through device monitoring | Advanced: With a focus on device monitoring | Scaling and integration may be complex | Advanced: Device diversity is its main strength | 24/7/365: Support via web, email, chat, and phone | Pricing not available online. |
| Aruba ClearPass | Advanced: Includes compliance and incident response | Advanced | Easy to scale. Powerful integration capability | Good | 24/7/365: Support via web, email, chat, and phone | Pricing not available online. |
| Fortinet FortiNAC | Good | Advanced: Cloud-based incident response | Seamless cloud scaling | Advanced: Cloud reports accessible from anywhere | 24/7/365: Support via web, email, chat, and phone | Complex licensing. Prices available upon request |
| Extreme Networks | Good | Good | Advanced | Advanced | 24/7/365: Support via web, email, chat, and phone | Available upon request |
Featured Network Access Control (NAC) Software
1. Cisco Identity Services Engine (ISE)
Best for large enterprises with advanced requirements

CISCO ISE Logo. Source: CISCO.
Cisco Identify Services Engine (ISE) is one of the top NAC solutions in the market. The technology is popular among large enterprises with sophisticated network requirements. ISE is a comprehensive, next-generation NAC solution, rich in features.
Companies using ISE can provide highly secure network access to users and devices while having complete visibility across wired, wireless VPN, and 5G connections. It also provides users with information on apps installed and running and vital contextual data, such as user and device identities, threats, and vulnerabilities.
The company differentiates itself from the competition by being a one-stop solution. It also offers self-service onboarding features for BYOD policies, automated device-compliance checks, and central network device management. Cisco offers separate NAC solutions for the industrial Internet of Things (IIoT), operational technology (OT), and industrial controls for medical devices.
Pricing
CISCO ISE pricing can not only be expensive but difficult to understand. The CISCO ISE licenses plans are numerous, and components and services may only be available with additional costs, depending on the number of users in the network. The new Tier Licenses include Essentials, Advantage, and Premier. Details of each can be found here. Prices are available upon request.
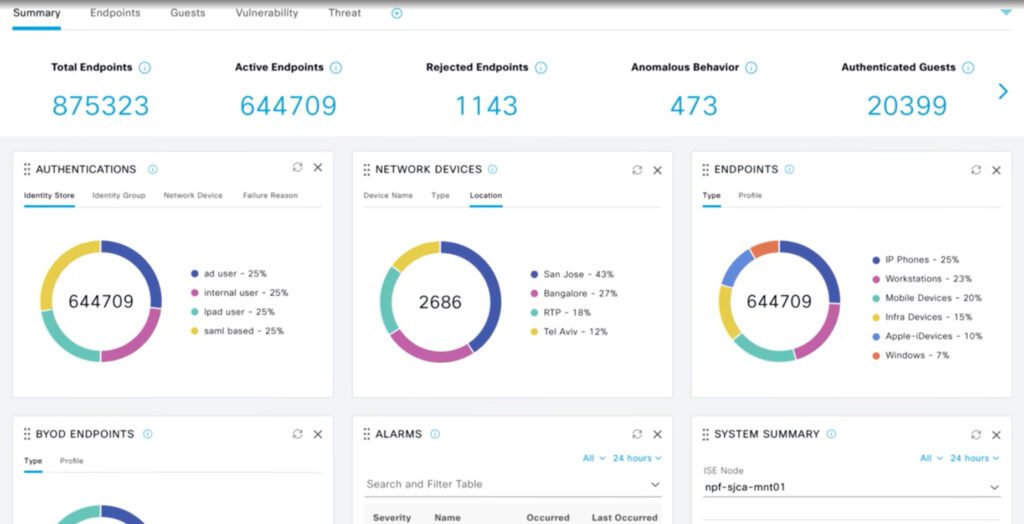
CISCO ISE central visibility dashboard. Source: CISCO.
Features
- Centralization, visualization and management: Administrators can configure and manage profiles, postures, compliance, users, and authentication and authorization services in a single web-based GUI console.
- Integrations: The service can integrate with external identity repositories such as Microsoft Active Directory (On-Prem or Azure AD), Lightweight Directory Access Protocol (LDAP), RADIUS, RSA One-Time Password (OTP), certificate authorities for both authentication and authorization, Open Database Connectivity (ODBC) and SAML providers.
- Attributes: Includes user and endpoint identity, posture validation, authentication protocols, device identity and other external attributes.
- Highly secure environment customized with company policies: Provides features to enforce a highly secure access policy that matches the identity’s business role with attributes such as user, time, location, threat, vulnerability and access type.
- Streamlined network visibility: Stores a history of all endpoints that connect to the network and users, including guests, employees, and contractors, as well as applications and firewalls.
- Advanced policy enforcement: Allows users to apply access rules that meet changing requirements.
- Automated device-compliance checks: Using the Cisco AnyConnect Unified Agent, users can access advanced VPN services for desktop and laptop compliance checks.
- Seamless onboarding for BYOD and guest policies: Provides IT staff with automated device provisioning, profiling, and posturing to comply with security policies, while BYOD devices can self-onboard without IT support.
- Reports and real-time tracking: Provides administrators with real-time visual flows, tracks access across the network for security and compliance, and runs advanced reports.
- Device profiling: Offers predefined device templates for many types of endpoints, such as IP phones, printers, IP cameras, smartphones, and tablets. Additional templates for specialized devices such as medical, manufacturing, and building automation are available.
Pros
- Advanced capabilities for large enterprises that require sophisticated NAC technology.
- One-stop solution, rich in features.
- Provides features for industrial networks and specialized use cases.
- Excellent consolidation and visualization through centralized dashboards.
- Enables zero trust architectures.
- Provides compliance.
- Seamless onboarding for BYOD devices.
Cons
- It can be expensive.
- Requires expert knowledge to operate.
- Has a steep learning curve.
- Pricing and licensing can be confusing.
2. Forescout Platform
Best for organizations with user and device diversity
Forescout Logo. Source: Forescout.
Since 2021 when Forescout was recognized as the Customer Choice by Gartner Peer Insights’ “Voice of the Customer” NAC report, the company has consolidated its reputation for offering a robust solution to manage all types of devices.
With an easy-to-use platform and seamless deployment, sided with good support, companies can implement Forescout zero trust access on their networks for a vast array of devices and connected things — including employee devices returning to the office post-COVID, remotely connected devices, transient devices, guest/BYOD devices, and IoT, OT, and smart devices.
Additionally, the company provides modern NAC features, including automated remediation, access control implementations, monitoring, and management and insights.
Pricing
Forescout does not provide online pricing information. The company does offer a licensing guide that details the hardware and software products. The platform can be deployed on physical on-premises or cloud and edge virtual appliances, as well as smaller use cases licenses.
Forescout products include:
- XDR
- eyeSight
- eyeInspect
- eyeSegment
- eyeControl
- eyeExtend
- Forescout Medical Device
- Multifactor Risk Scoring
- Forescout Timeline
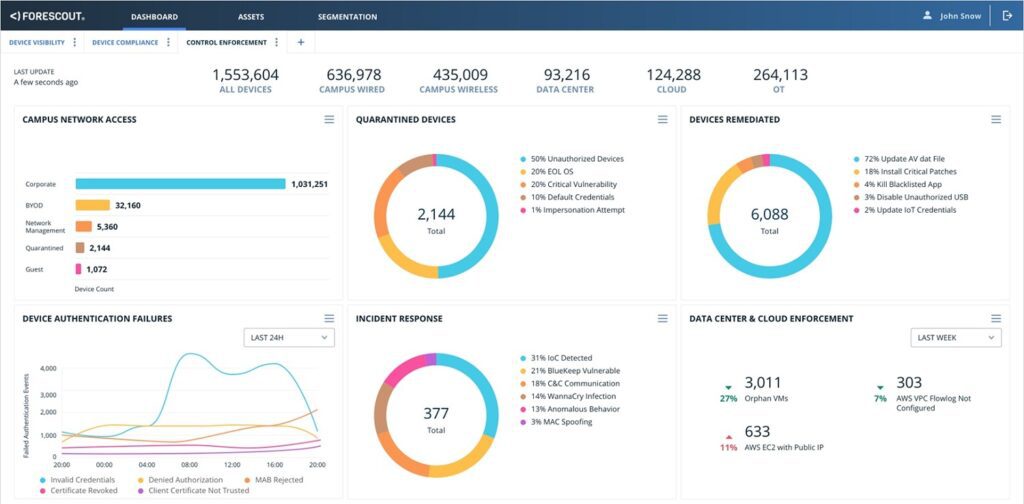
Forescout dashboard. Source: Forescout.
Features
- Visibility: 100% real-time visibility of all devices connected to extended networks.
- Zero trust: Zero trust for all connecting devices. Continuous agentless monitoring and a unified policy engine that dynamically segments and isolates all connecting devices.
- Discover, classify, and inventory: 100% real-time visibility of all IP-connected devices the instant they access the network. Provides an accurate, real-time asset inventory. Users can choose from 20+ active and passive discovery and profiling methods.
- Device diversity: 12M+ device fingerprints available in the Forescout Device Cloud for device classification. Determine device function, OS, vendor and model, and more.
- Compliance: Detects device noncompliance, posture changes and vulnerabilities. Find and fix managed devices with missing, broken, or nonfunctional agents from your existing security tools.
- Threat detection: Detects weak credentials, IoCs, spoofing attempts, and other high-risk indicators, all without agents. Monitor unmanaged devices.
- Access policies: Provisions least-privilege access to enterprise resources based on user role, device type, and security posture. Prevent connection of unauthorized, rogue, and impersonating devices.
- Forescout Platform: Delivers visibility and automation across all types of assets — IT, IoT, IIoT, and OT.
Pros
- Easy to use.
- Can rapidly identify and deploy a vast array of devices.
- Provides NAC advanced features for visualization, security and vulnerabilities.
Cons
- Pricing is not disclosed online.
- Complexity: Forescout solutions can be complex to deploy and manage. They require a significant investment in time and resources and can be challenging to scale to large environments.
3. Aruba ClearPass
Best for SMBs

Aruba HPE. Source Aruba ClearPass.
Aruba Clearpass, a Hewlett Packard Enterprise company, is popular among SMBs looking to authenticate, authorize, and enforce secure network access control with role-based network policies based on zero trust security.
The solution innovates with AI-powered visibility, robust integrations and state-of-the-art security. ClearPass is available as hardware or as a virtual appliance. It is also a vendor-agnostic technology that works seamlessly with third-party network devices. Besides its Clearpass solution, Aruba offers network switches, access points, and cloud-based technologies. Its ease of use and price make it an SMB favorite.
Pricing
There are three significant licenses for Aruba ClearPass: Platform Licenses, Base Applications, and add-on Applications. Platform licenses and base applications are required for deployment, while add-ons extend functionality and are optional.
The solution can be purchased as virtual technology or as hardware. For a detailed explanation of ClearPass licenses, you can watch the following official video. The company does not provide pricing information online; it is only available upon request.
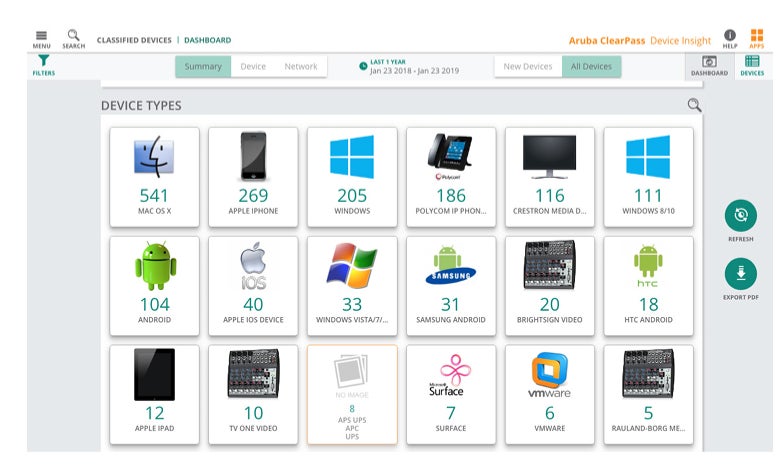
Aruba ClearPass device insight dashboard. Source: Aruba.
Features
- Robust Network Access Control: Aruba ClearPass Policy Manager (CPPM) provides robust network access control with role-based policies for authentication, authorization, continuous monitoring, and enforcement.
- Automated BYOD provisioning and device compliance: Users can easily deploy BYOD workflows to authorize employees and contractors.
- Customized visitor experience: Companies using Clearpass can implement secure guest access and build customized web portals for visitors.
- Automated device configuration: ClearPass Onboard automatically configures and provisions both PCs and mobile devices — Windows, macOS, iOS, Android, Chromebook, and Ubuntu — enabling them to securely connect to enterprise networks supporting BYOD initiatives.
- Vendor agnostic: Supports Windows, macOS, iOS, Android, Chromebook, and Ubuntu operating systems
- Automation: Automates the configuration of network settings for wired and wireless endpoints
- AI-powered visibility: ClearPass has built-in AI-driven device discovery and profiling features.
- Policy enforcement: The system can detect and respond to security vulnerabilities and breaches from various security, network, and IT sources.
Pros
- Integrations: Provides more than 140 security-based partner solutions.
- Easy to use and deploy.
- Identifies and reacts to breaches and suspicious activity.
- Cost-effective.
- Popular among SMBs.
Cons
- It may not be suitable for sophisticated network requirements.
- Troubleshooting can be complex.
4. Fortinet FortiNAC
Best for cloud-based NAC solution

FortiNAC logo. Source: Fortinet.
FortiNAC is a comprehensive NAC solution that provides visibility, control, and security for all devices connecting to your network. Although it can be deployed on-premises or in the cloud, its cloud version leads in the market due to its rapid deployment, scaling, and management.
The solution is a good option for organizations of all sizes. It is easy to deploy and manage and it offers a wide range of features and capabilities that can help you protect your network from various threats.
Pricing
FortiNAC pricing can be complex as it varies depending on what products and services the customer needs. The company offers hardware and virtual machines for network controls.
Additionally, its platform can be acquired under three plans, Base, Plus, or Pro. Licenses can be perpetual or subscription-based and depend on the number of endpoints in the network. Details are explained in this official guide on FortiNAC licenses.
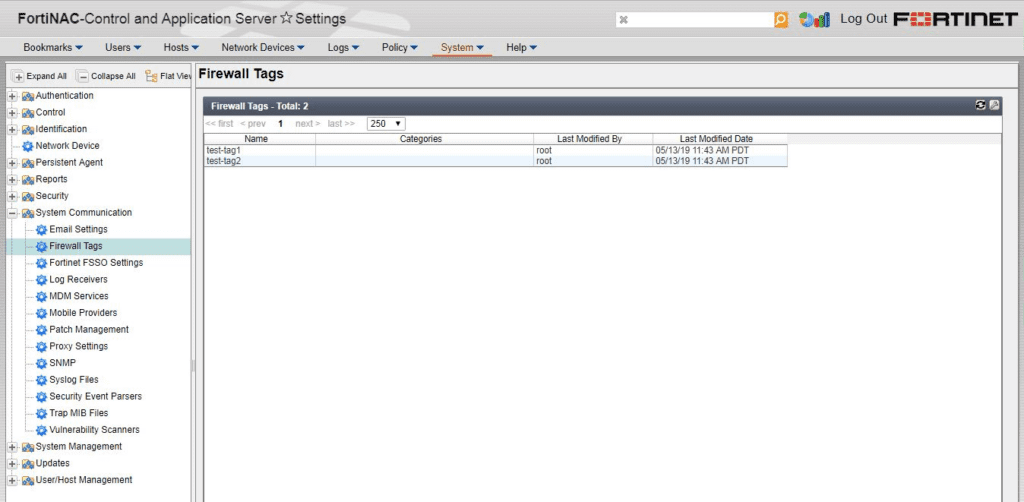
FortiNAC Control and Application Server Settings dashboard. Source: Fortinet
Features
- Device identification and profiling: FortiNAC can identify and profile all devices connecting to your network, including their operating system, software versions, and security settings. This information can be used to identify unauthorized devices, devices out of compliance with security policies, and devices that pose a security risk.
- Policy-based access control: The platform allows users to define granular access policies based on user identity, device type, and other criteria, ensuring security policies and compliance.
- Compliance reporting: FortiNAC can generate reports that can be used to demonstrate compliance with industry regulations, such as HIPAA, PCI DSS, and SOX.
- Vulnerability assessment and incident response: The technology can scan devices for known vulnerabilities and provide remediation recommendations. It can also help users respond to security incidents by providing information about the devices involved in the incident and the actions that can be taken to mitigate the incident.
- Cloud-based reporting and remediation: Fortinet NAC leverages cloud technology to generate reports that can be accessed from anywhere. The vendor also automatically remediates security vulnerabilities found on devices, reducing the risk of an attack.
Pros
- Compliance: FortiNAC can help organizations comply with various security regulations, including HIPAA, PCI DSS, and SOX.
- Security: FortiNAC is a solution of Fortinet, a company known for its cybersecurity technology.
- Cloud-based features allow for remediation, rapid updates, visualization, and more.
Cons
- It can be complex to operate.
- Steep learning curve.
- Licensing can be tricky for beginners.
5. Extreme Networks ExtremeControl
Best for integrating NAC solutions to existing infrastructure

Extreme Networks ExtremeControl Logo. Source Extreme Networks.
ExtremeControl, a product of Extreme Networks, is a flexible and scalable technology that can be deployed in a variety of ways, making it the best for integrating NAC solutions to existing infrastructure.
ExtremeControl can be deployed on-premises, in the cloud, or a hybrid environment. ExtremeControl can also be integrated with other security solutions, including firewalls, intrusion detection, and identity management systems.
Pricing
Pricing information is only available upon request. Plans and licenses vary depending on the customer’s on-premises technology or cloud needs. ExtremeControl can be purchased as a perpetual license or in subscription models. Prices vary depending on the number of users and features required.
ExtremeControl Extreme Networks. Source Extreme Networks.
Features
- Identify and authenticate devices: ExtremeControl can identify and authenticate all devices connecting to the network, including their OS, software versions, and security settings.
- Define granular access policies: Administrators can define granular access policies based on user identity, device type, and other criteria.
- Network Visibility: Administrators have full visibility into all devices and users on the network, including their identity, device type, and security posture. This information can be used to identify security threats and to improve security posture.
- Unauthorized access: ExtremeControl helps companies protect networks from unauthorized access by enforcing access policies and identifying and remediating unauthorized devices.
Pros
- Flexible deployment options: ExtremeControl can be deployed on-premises, in the cloud, or a hybrid environment.
- Scalable solution: Can be scaled easily up or down to meet demands.
- Easy to integrate with other security solutions: ExtremeControl can be integrated with various other security solutions, including firewalls, intrusion detection systems, and identity management systems.
Cons
- The wide range of features and capabilities may be overwhelming for beginners.
- Like all NAC, ExtremeControl can have a negative impact on network performance, especially when running the system on large networks.
Key features of NAC software
As a rule, NAC software should include policy enforcement and session controls, vulnerability scanning and malware detection, and user profiling and reporting capabilities. You’ll also want to consider each solution’s scalability, customer support, and of course its pricing matrices.
Policy enforcement and session control
Enforcing policies on devices connecting to the network is a fundamental feature of all NAC technologies. This can include policies such as requiring devices to be patched, requiring devices to be encrypted, or requiring devices to be registered with the network.
Vulnerability scanning and malware detection
NAC solutions scan devices for known vulnerabilities. This information can be used to block devices with known vulnerabilities, quarantine devices until they are patched, or remediate vulnerabilities.
Scalability and integration
Networks are ever-changing environments that can scale up or down and NAC solutions must be able to pivot rapidly, offering customers easy-to-use scalability. When traffic increases, NAC tools must be able to manage it by scaling without affecting performance or compromising security.
Additionally, integration is essential in the modern digital era. NAC platforms and hardware must integrate with other security solutions, such as firewalls, intrusion detection systems, and antivirus software.
User profiling and reporting
Profiling users and devices is another crucial component of NAC systems. They should offer visibility into performance, risks, vulnerabilities, and network status. Administrators can block unauthorized devices, quarantine infected devices, or remediate vulnerabilities by profiling users.
Reporting is also fundamental. It can be used to make data-driven decisions about the network, present compliance and security reports, and better understand users, credentials, certificates, and more.
Customer support
NAC solutions can be highly advanced, therefore having solid, dependable customer support can make a big difference.
Pricing
As a rule of thumb, NAC vendors do not disclose pricing online. Their products, services, solutions, and licenses can also be complex. To understand the costs, and whether they align with your company’s budget, you’ll need to reach out to each vendor’s sales team and do your research.
How to choose the best NAC software for your business
Choosing the best NAC software for your business depends on several factors, including your organization’s size, industry, and security needs. Before taking the leap, consider what NAC solutions are the best for your business size and network demands.
Also take into consideration your industry. Some vendors offer specialized NAC technology for healthcare and IIoT for manufacturing. The number of users, contractors, and guests on your network will also be a defining factor.
No matter which NAC solution you choose, it is important to ensure it is properly implemented and configured. Do your research, get quotes from multiple vendors, make sure the service and products align with your business goals, and consider your needs and compatibility.
Frequently Asked Questions (FAQs)
What are NAC technologies?
NAC stands for Network Access Control. Companies offering NAC solutions usually sell software, licenses, hardware, cloud platforms, and virtual machines to create a security framework that helps organizations control who and what can access their networks.
NAC solutions typically use a combination of policies, enforcement mechanisms, and profiling tools to assess the security posture of devices and users before granting them access to the network.
What is policy enforcement?
Policy enforcement in NAC ensures that devices and users comply with the organization’s security policies.
Policy enforcement is an essential part of NAC because it helps to protect the network from unauthorized access, malware, and other threats. By enforcing security policies, users can ensure that only authorized devices and users can access the network.
Why are user and device profiling important in NAC solutions?
The number of devices connecting to a network has increased exponentially in recent years. This creates a problem, as the digital attack surface of companies keeps increasing, giving cybercriminals more chances to find vulnerabilities.
Knowing which devices and users are connected also allows administrators to manage traffic and privacy and gain critical insight into a network. Companies can enforce security and authentication by identifying and profiling users and devices, preventing malware infections, and shutting down unauthorized users.
How do NAC solutions help companies stay compliant?
From GDPR to the Payment Card Industry Data Security Standard (PCI DSS), the Health Insurance Portability and Accountability Act (HIPAA), and other national and international laws, NAC solutions can help companies stay compliant with regulations by enforcing security policies, preventing unauthorized access and providing visibility.
Additionally, some NAC technologies offer compliance reporting capabilities that companies can leverage when presenting reports to authorities.
Why do NAC solutions rarely provide pricing online?
There are a few reasons why NAC solutions rarely provide pricing online. But most importantly, NAC technologies vary greatly depending on the needs of an organization, including the type of network, if they need hardware or software, and how many users and devices the network has.
Many NAC solutions are sold as part of a larger security suite, which includes other security products such as firewalls, intrusion detection systems, and antivirus software.
Do I still need threat detection if I have a NAC solution running?
While NAC technology can run vulnerability scanning and malware detection, you still need threat detection. Threat detection solutions can help to identify and respond to threats that have already bypassed NAC controls. Furthermore, NAC solutions work together with threat detection technologies providing a multilayered approach to network security.
What are the benefits of NAC?
NAC can help to improve the security and performance of a network in several ways, including:
- Preventing unauthorized access to the network.
- Protecting the network from malware and other threats.
- Enforcing security policies on devices and users.
- Providing visibility into the network and its users.
What are the challenges of NAC?
NAC can be complex and challenging to implement.
Some of the challenges of NAC include:
- Integrating NAC with existing security solutions.
- Managing NAC policies and enforcement.
- Educating users about NAC.
Methodology
We looked into the best-performing vendors and alternatives to write our review and evaluate the top NAC solutions and features. We examined sites that compile aggregate data based on verified user reviews. We also reviewed demos on vendor sites, test-drove the software when possible, and scoured through the official sites of the featured vendors to evaluate their features, customer service, user-friendliness, price, and scalability.
Bottom line: Protecting your network with NAC
Driven by the global digital transformation that followed the post-pandemic era, NAC solutions have become vital privacy and security solutions. NAC technology manages and monitors devices, enforces policies, identifies security weaknesses and leverages automation and AI to make your networks better and safer.
If you are looking to gain visibility in your network, reduce data breaches, enforce policies, reduce costs, and increase performance and security, NAC solutions can help you to achieve these goals.
For more tips on improving your network security profile, here’s a quick guide to conducting a network security audit at your organization.



