Virtual private networks (VPNs) are software tools that ensure data is confidential and safe from potential breaches by creating encrypted tunnels between devices and servers.
As cyberthreats continue to become more daring, sophisticated, and frequent, there’s an ever increasing need for more secure and more private online connections, particularly with the increasing adoption of remote work today.
That’s where VPNs come in. VPNs have emerged as indispensable tools for businesses to safeguard their data from potential threats.
Here are our top enterprise and business VPN software picks for 2023:
- Surfshark: Best overall enterprise and business VPN (Read more)
- Private Internet Access: Best for competitive pricing (Read more)
- Proton VPN: Best for core features and integrations (Read more)
- NordVPN: Best for advanced privacy and security (Read more)
- CyberGhost VPN: Best for a user-friendly interface (Read more)
- IPVanish: Best customer support (Read more)
Top enterprise VPN software comparison
Here’s how our top 6 VPN software tools compare against each other across features and pricing.
| Privacy | Security | Speed | Logging | Number of servers | Number of server countries | Simultaneous connections | Split tunneling | Kill switch | Starting price (1-year) | |
|---|---|---|---|---|---|---|---|---|---|---|
| Surfshark | Yes | Yes | Yes | No | 3,200+ | 100+ | Yes | Limited | Yes | $3.99/mo. |
| Private Internet Access | Limited | Yes | Limited | No | 35,000+ | 84 | Yes | Yes | Yes | $3.33/mo. |
| Proton VPN | Yes | Yes | Limited | Yes | 2,988 | 69 | Yes | Yes | Yes | $6.55/mo. |
| NordVPN | Yes | Limited | Yes | Limited | 5,000+ | 60 | Limited | No | Yes | $4.99/mo. |
| CyberGhost VPN | Limited | No | No | Yes | 9,000+ | 91 | Limited | Yes | Limited | $2.19/mo. |
| IPVanish | No | Limited | Yes | No | 2,200+ | 50 | Yes | Limited | Yes | $3.59/mo. |
Jump to:
- Key features of enterprise VPN software
- How to choose the best enterprise VPN software for your business
- How we evaluated enterprise VPN software
- Frequently Asked Questions (FAQs)

Surfshark
Best overall enterprise and business VPN
Surfshark is our top pick for enterprise and business VPN. Not only does it offer great privacy features, but it also provides thorough security features that ensure users are protected online.
With its AES-256-GCM encryption and 3,200+ servers, Surfshark ensures fast and secure connections. Its commitment to user privacy is evident, with features like camouflage mode and VPN location changer making it a favorite for businesses and individuals alike.
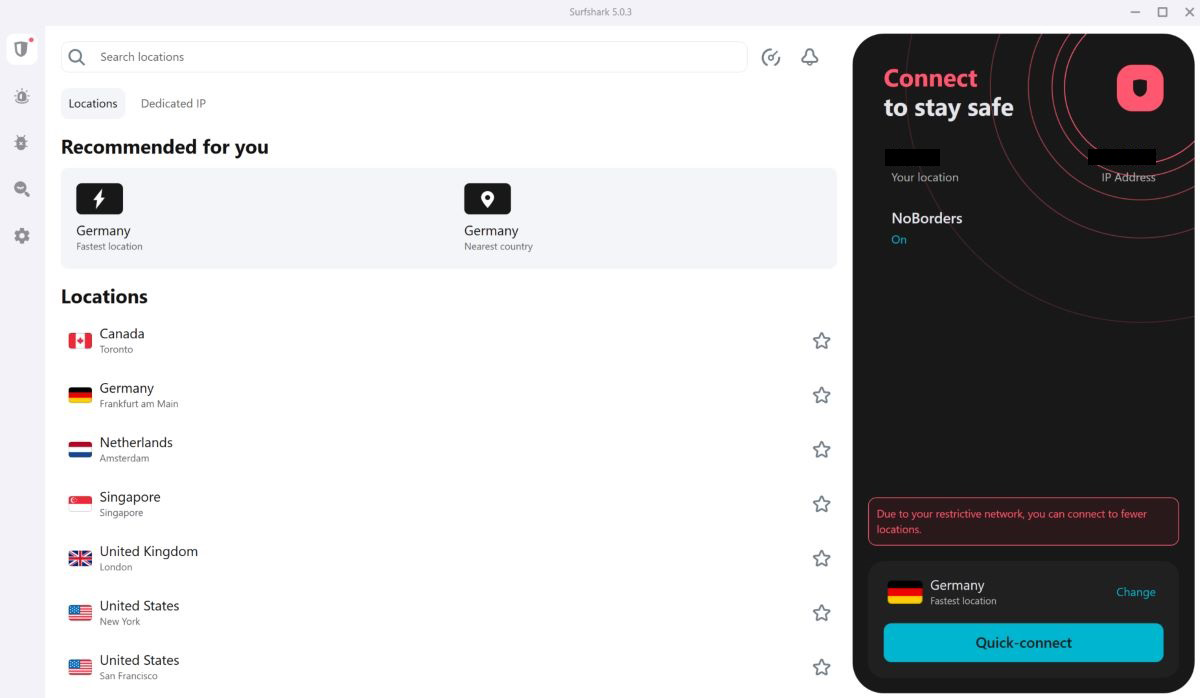
Pricing
Surfshark has no free version but offers a 30-day free trial. It offers 1-month, 1-year, and 2-year plans. The 1-year plan, Surfshark Starter, starts at $3.99 per month.
Features
- CleanWeb, which offers privacy features like tracker and ad blocking.
- Kill switch in case there’s a drop in your VPN connection.
- Bypasser to allow certain websites and apps to bypass the VPN.
- Camouflage mode ensures your ISP can’t tell you’re using a VPN.
Pros
- Supports unlimited devices and simultaneous connections.
- 3,200+ server locations.
- Strict no-logs policy.
- Vast integration options, such as with Xbox consoles.
Cons
- Less than 400 Mbps speed.
- Limited split tunneling options.
- No phone support.
- No free version.

Private Internet Access
Best for competitive pricing
Private Internet Access (PIA) stands out for its competitive pricing without compromising on security. PIA declares that it offers 100% open-source VPN apps, meaning its client source code is publicly available.
Aside from the core features you’d expect from a VPN, PIA offers streaming, gaming, and torrenting VPN features alongside advanced security features. Its wide variety of features ensures that users can browse the internet safely while getting value for their money.
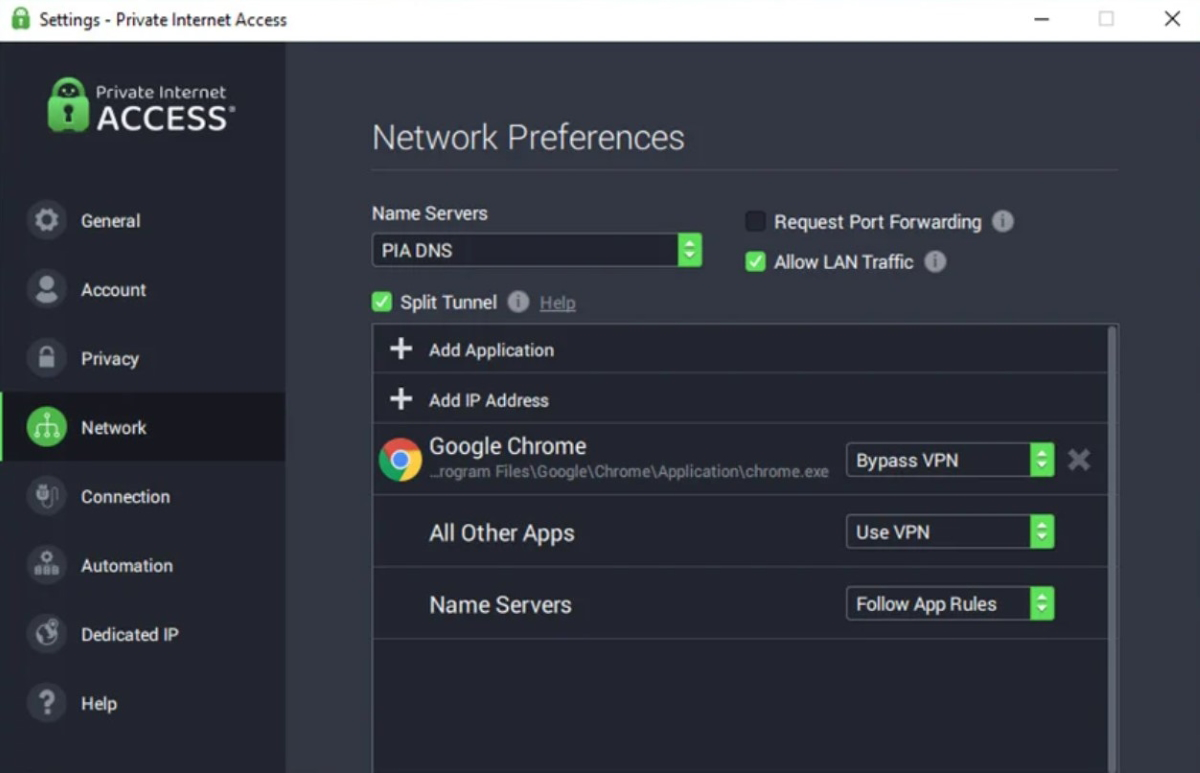
Pricing
PIA’s pricing starts at $3.33 per month billed annually. It has a 30-day free trial but no free version.
Features
- Advanced split tunneling features.
- PIA MACE, which blocks ads, trackers, and malware.
- No-logs policy covers digital tracks.
- Advanced kill switch to prevent data leaks.
Pros
- Affordable pricing plans.
- Unlimited device connections.
- Highly configurable VPN.
- 35,000+ servers.
Cons
- No phone support.
- No free version.
- Low average speed of 117 Mbps.
- Not the most intuitive user interface.

Proton VPN
Best for core features and integrations
Proton VPN is a renowned Swiss-based VPN operating on the pillars of freedom, privacy, and security. It stands out for its feature-rich offerings and extensive desktop, mobile, IoT, and web extension integrations.
It is also the only VPN on this list to offer a free VPN that’s ad-free, as the cost of the free VPN is subsidized by paid users.
Additionally, all Proton apps are open source, showing its commitment to transparency. Proton VPN has high-speed servers that can get to up to 10 Gbps.
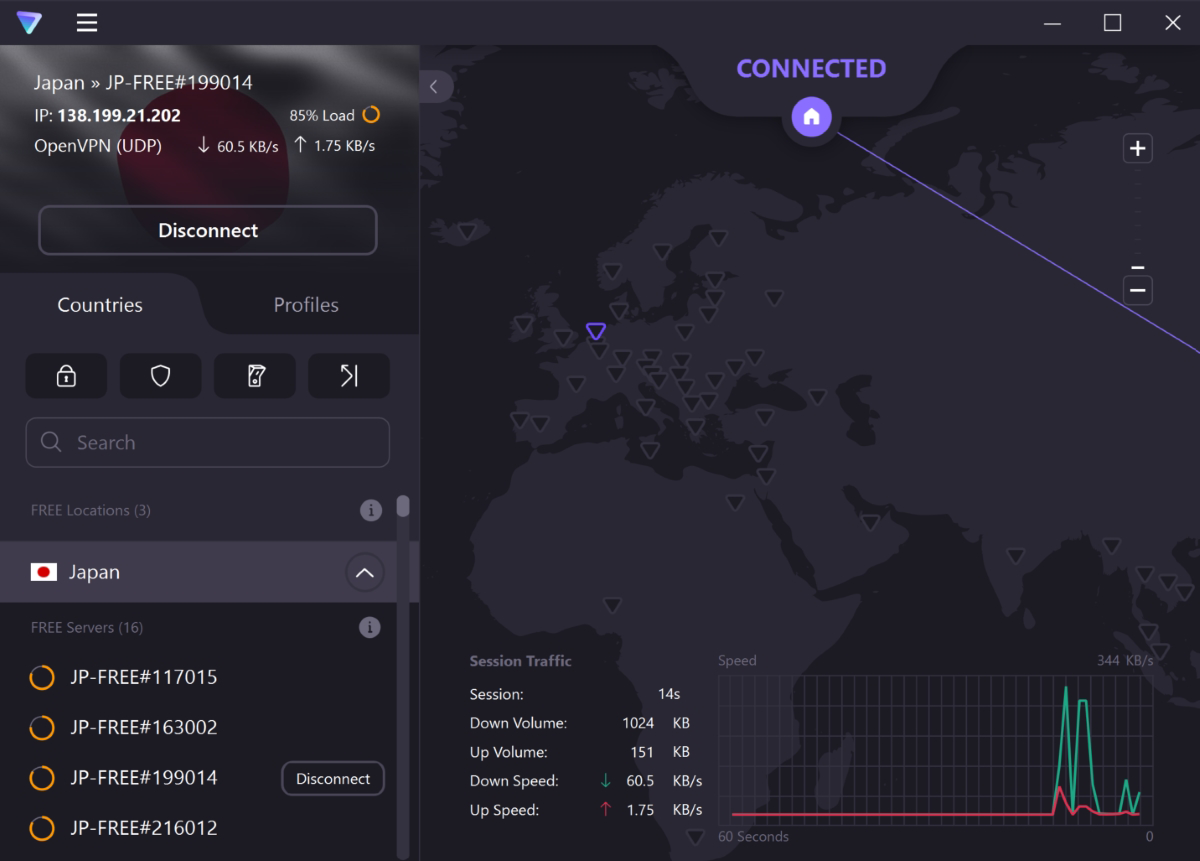
Pricing
Proton VPN has no free trial but does offer a free plan. Its 1-year plan costs about $6.55 per month.
Features
- No-logs policy to ensure internet activity isn’t tracked or recorded.
- VPN for streaming to access geo-blocked content and enjoy accessible, high-speed, and secure streaming.
- NetShield Ad-blocker for blocking ads, trackers, and malicious scripts.
- Tor over VPN allows you to connect to the Tor anonymity network.
Pros
- Free version available.
- Great VPN speeds.
- Swiss-based, meaning it’s outside EU and U.S. jurisdiction.
- Has phone customer support.
Cons
- Highest priced VPN on this list.
- Phone and email customer support can be improved.
- Not as many server countries as most of the other VPNs.
- With 2,988 servers, it doesn’t have as many servers as most competitors listed here.

NordVPN
Best for advanced privacy and security
NordVPN is a household name in the VPN industry, and for good reason. While it offers a plethora of features, its privacy and security features are particularly impressive.
These features include threat protection to deal with common internet threats; Meshnet to create a personal encrypted network for file sharing, LAN parties, and more; a dark web monitor; and dedicated IP capabilities. You can also obfuscate servers with NordVPN so that your ISP remains unaware that you’re using a VPN.
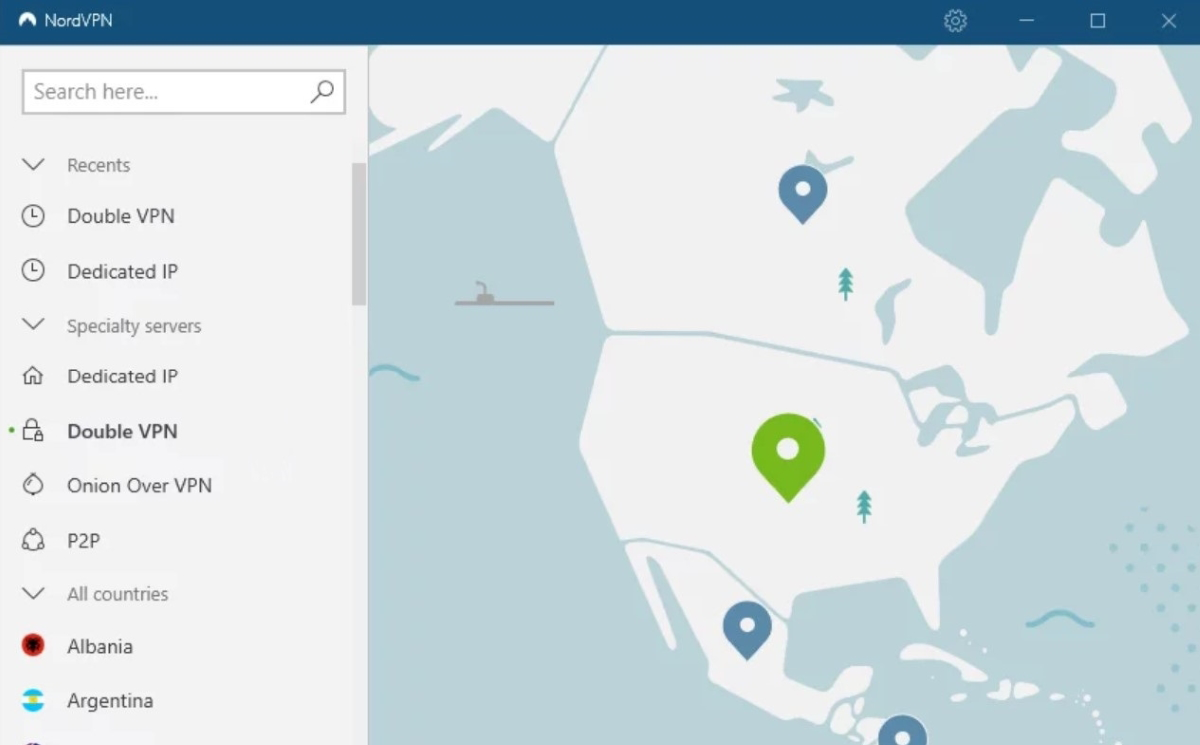
Pricing
Although it has no free plan, NordVPN offers a 30-day trial period. Its pricing for its 1-year plan starts at $4.99 per month.
Features
- Double VPN to add an extra layer of encryption.
- Split tunneling to choose between which apps to trust and which not to.
- Integrated kill switch to shield data in case of connection drops.
- Onion over VPN to combine Tor benefits with extra VPN security.
Pros
- More than 5,000 servers.
- Available for individuals, SMBs, and enterprises.
- User-friendly interface.
- No logging policy.
Cons
- Lower than average speed at 196 Mbps.
- Has only 60 server countries.
- Slightly more expensive than some competitors.
- Simultaneous connections are limited to only six users.

CyberGhost VPN
Best for a user-friendly interface
CyberGhost VPN is designed with the user in mind. It’s easy to install, set up, and manage and its intuitive interface ensures that even VPN newbies can navigate and utilize its features with ease.
Beyond this user-friendliness, CyberGhost offers a range of features tailored for different use cases, even having specialized features for streaming, torrenting, and gaming. It’s committed to no logs and delivers strong VPN encryption like 256-bit AES to make sure users can browse with peace of mind.
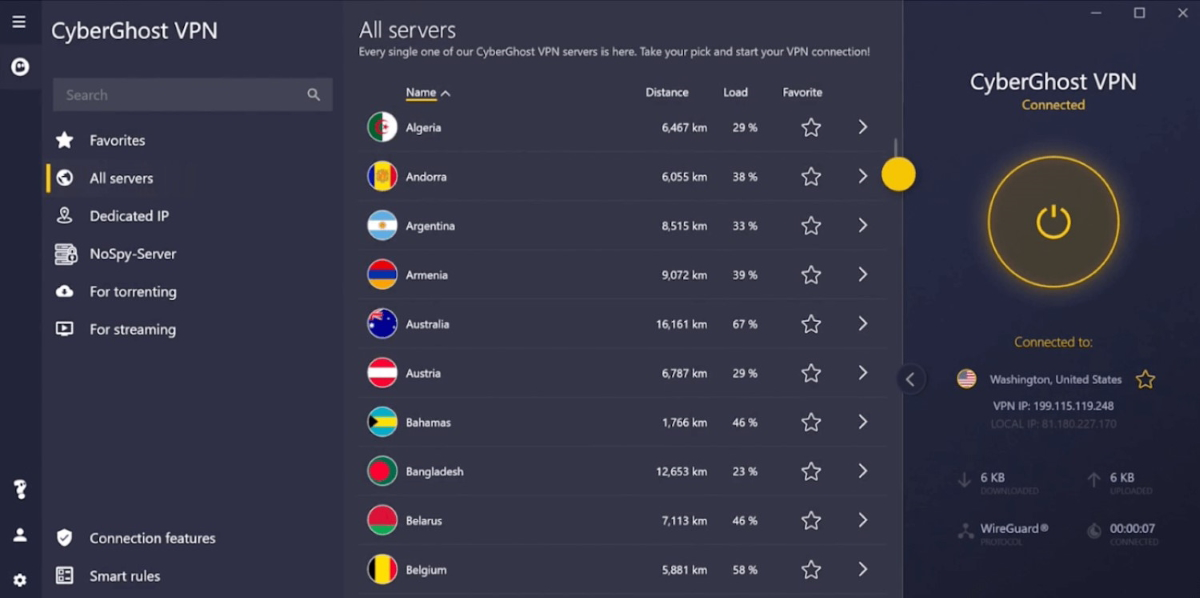
Pricing
Plan options are monthly, every 6 months, and every 2 years, with the two-year plan priced at $2.19 per month.
Features
- IP masking to allow users to change their IP addresses.
- Streaming-, torrenting-, and gaming-optimized servers.
- No logs VPN service.
- RAM-only servers that wipe data with every reboot.
Pros
- Intuitive interface suitable for all users.
- More than 9,000 servers.
- 24/7 live chat and email support.
- Vast integrations, including compatibility with PlayStation consoles.
Cons
- No business or enterprise plans available.
- Split tunneling is only available for Windows and macOS desktop apps.
- Only 7 simultaneous connections.
- Offers only a 1-day free trial.

IPVanish
Best customer support
IPVanish stands out for its expansive customer support, ensuring enterprises have the assistance they need when setting up, managing, or troubleshooting. Interestingly, it is one of only two tools on this list to offer phone support as part of its customer service.
Its feature set covers the features you’d expect to see from a VPN, plus advanced ones such as automatic startup, SOCKS5 proxy, and DNS leak protection, among others.
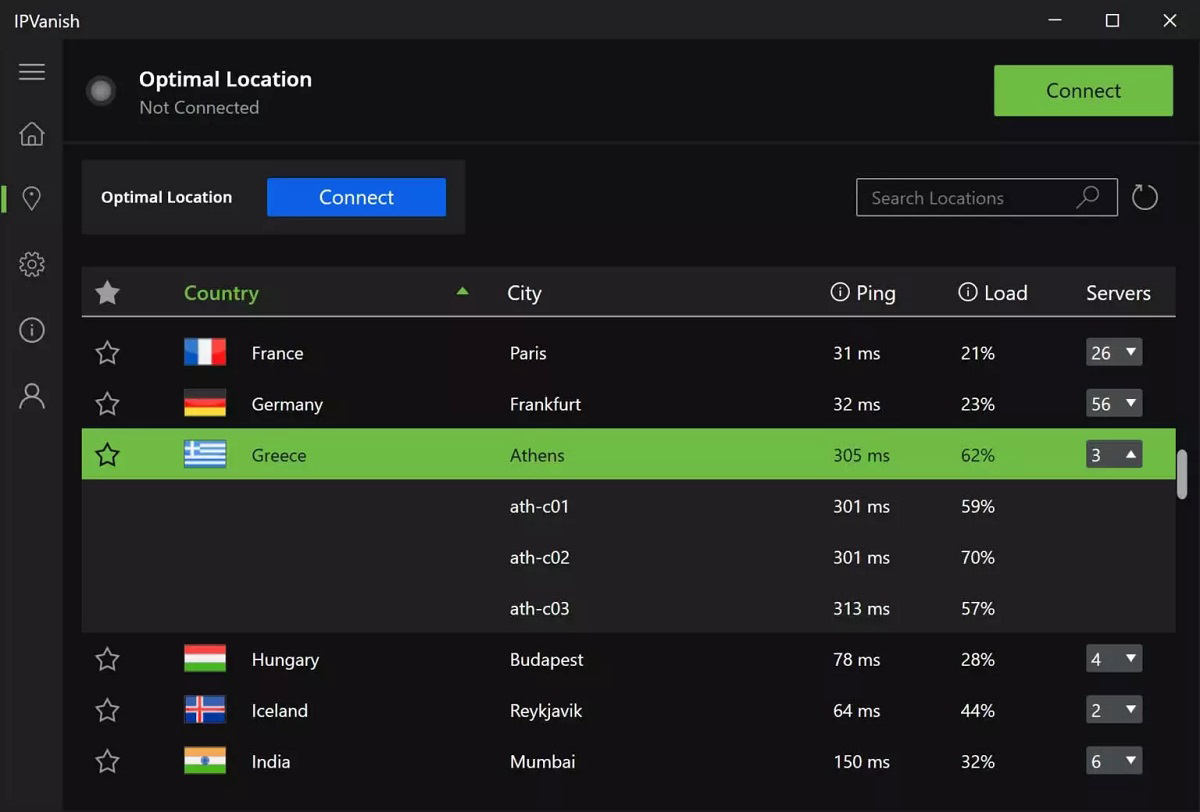
Pricing
Although IPVanish doesn’t have a free plan, it offers a 30-day free trial, and its pricing starts at $3.59 per month for its yearly plan.
Features
- 24/7 customer support with phone support.
- Independently verified no traffic logs policy.
- Encrypted web browsing to prevent man-in-the-middle attacks.
- Split tunneling for a customized connection setup.
Pros
- Extensive customer support.
- Unmetered number of connections.
- Servers in 75+ locations.
- VPN kill switch for added security.
Cons
- Only 2,200+ servers.
- Phone support is only available during business hours on weekdays.
- Email support may take up to 48 hours for a response.
- Limited global server coverage (50+ countries) compared to competitors.
Key features of enterprise VPN software
Enterprise VPN solutions come with a variety of features designed to enhance security, improve connectivity, and offer flexibility. Some of the key features to look for across the board include privacy protection, security protocols, high-speed connectivity, wide server availability, split tunneling, and a kill switch.
Privacy protection
A top-tier VPN makes sure your online activities remain private. This can be through masking your IP address and encrypting your data to make it unreadable to third parties. VPNs like Proton VPN excel in this area, offering features like NetShield Ad-blocker to block unwanted elements like ads and trackers and uphold user privacy.
Robust security protocols
Security is paramount for any VPN solution. Leading VPNs have advanced encryption standards and protocols like OpenVPN and IKEv2/IPsec to safeguard data. Surfshark, for instance, uses the aforementioned protocols with others like WireGuard.
High-speed connections
For businesses, speed is vital. A good VPN needs to offer fast connections. This makes sure that its users enjoy seamless browsing, streaming, and downloading, without interrupted productivity due to bandwidth bottlenecks.
Vast server coverage
Having a wide range of servers across various countries is what allows users to bypass geo-restrictions. VPNs like Surfshark (with 100+ server countries) and CyberGhost (with 91 countries) have extensive global server coverage to enable users to connect from almost anywhere.
Split tunneling
This feature empowers users to decide which part of their traffic accesses the internet directly and which part goes through the VPN. It provides flexibility, especially when certain apps or websites need a direct connection.
Kill switch
Last but not least, a kill switch is a security feature that cuts an internet connection if the VPN connection drops unexpectedly. This feature protects the user’s real IP address from being accidentally exposed.
How to choose the best enterprise VPN software for your business
As your VPN choice affects your business’s security, operations, and overall efficiency, choosing the right one cannot be taken as a light matter. You need to first determine your needs, whether they include enhanced security for remote workers or accessing geo-restricted content.
Privacy and security need to be at the forefront of any choice. But you also need to keep in mind speed and performance — for what good is having a VPN with great security and privacy if constant downtime keeps you from using it?
Also consider VPNs located in regions or countries with strong privacy laws to avoid the 5-Eyes, 9-Eyes, and 14-Eyes global surveillance alliances.
Additionally, you want a VPN with readily available customer support and great user experience. However, all these will depend on how much you’re willing to spend on a VPN.
How we evaluated enterprise VPN software
To get the best enterprise VPN, we used five weighted criteria that influence the effectiveness of VPN tools. Then we added weighted subcriteria to each criterion for a more granular level of scoring the VPNs and to help us understand what each tool is best for. Our winner was the VPN with the highest total score.
Core features – 30%
The criterion with the greatest weight was core features, as the features are arguably the greatest decision factors for these tools, followed by cost and integrations.
We examined the core features of each VPN tool by comparing how the features performed across privacy, security, speed, and logging, among other features.
Proton VPN was the best-performing software for this criterion.
Cost – 25%
As for cost, we first evaluated whether the VPNs offer free trials and what their durations were. We then learned whether each VPN had a full free version or not.
Our assessment went on to check the monthly costs of the tools, their billing options, and the variety of billing tiers they had.
Here we had two standout VPNs with tied scores: Surfshark and PIA.
Integrations – 20%
Next, we examined how integrable the VPNs are across desktop, mobile, IoT, and web extensions.
We found Proton VPN to be the only one that’s integrable across all four platforms.
Customer support – 15%
Our assessment involved noting how each VPN approaches customer support, whether through live chat, phone, email, forums, and documentation.
Even though all of the featured VPNs offer 24/7 live chat, only a couple of them offer phone support. IPVanish topped this criterion.
Ease of use – 10%
For ease of use, we considered two aspects: ease of installation and setup and ease of management. All the VPNs selected for this guide proved to be easy to use for a relatively experienced IT professional.
Frequently Asked Questions (FAQs)
FAQ #1: How do enterprise VPN solutions ensure secure remote access for employees?
Enterprise VPN solutions use advanced encryption protocols to secure data transmitted between an enterprise and a remote user. They typically also use multi-factor authentication (MFA) to verify the identity of users, ensuring that only authorized personnel can access the network.
FAQ #2: What are the key features to look for in an enterprise VPN solution?
Key features to consider include privacy protection, robust security, no-logs capabilities, split tunneling, and kill switch features, among the others listed above.
FAQ #3: Can enterprise VPN solutions support cloud connectivity and hybrid environments?
Yes, many enterprise VPN solutions are designed to support cloud connectivity, which enables employees to access cloud-based resources securely. They also cater to hybrid environments, ensuring that both on-premises and cloud resources are accessible and secure.
Bottom line: Improve privacy and protect data with a business VPN
Choosing the right VPN software for your business is a must if you want secure and private access. Through a combination of core features, cost, integration capabilities, the quality of customer support, and ease of use, businesses can find a tool that aligns with them and grants them the privacy they require.
A VPN is an important ingredient in a full network security stack — but it isn’t the only one. Read our in-depth guide to all the types of network security you might want to implement in your organization.


