Patch management is the systematic process of identifying, testing, and applying updates called patches to software, operating systems, and applications within an organization’s IT infrastructure. It is a crucial aspect of cybersecurity and IT maintenance.
Software vendors develop and distribute patches to address a variety of issues in their software. These issues can range from minor bugs that affect the software’s functionality to major security vulnerabilities. Attackers could exploit these vulnerabilities, posing a significant risk. In applying these patches, your organization actively enhances your protection against such vulnerabilities, reducing the risk of a cyberattack.
Patch management serves as a proactive defense mechanism against known vulnerabilities. It empowers organizations to reduce the risk of security breaches, data theft, and system compromise.
Table of Contents
Patch management process explained
While patch management varies from business to business, the general process consists of inventory and assessment, patch identification, risk prioritization, testing, deployment, monitoring and validation, documentation and reporting, and lifecycle management.
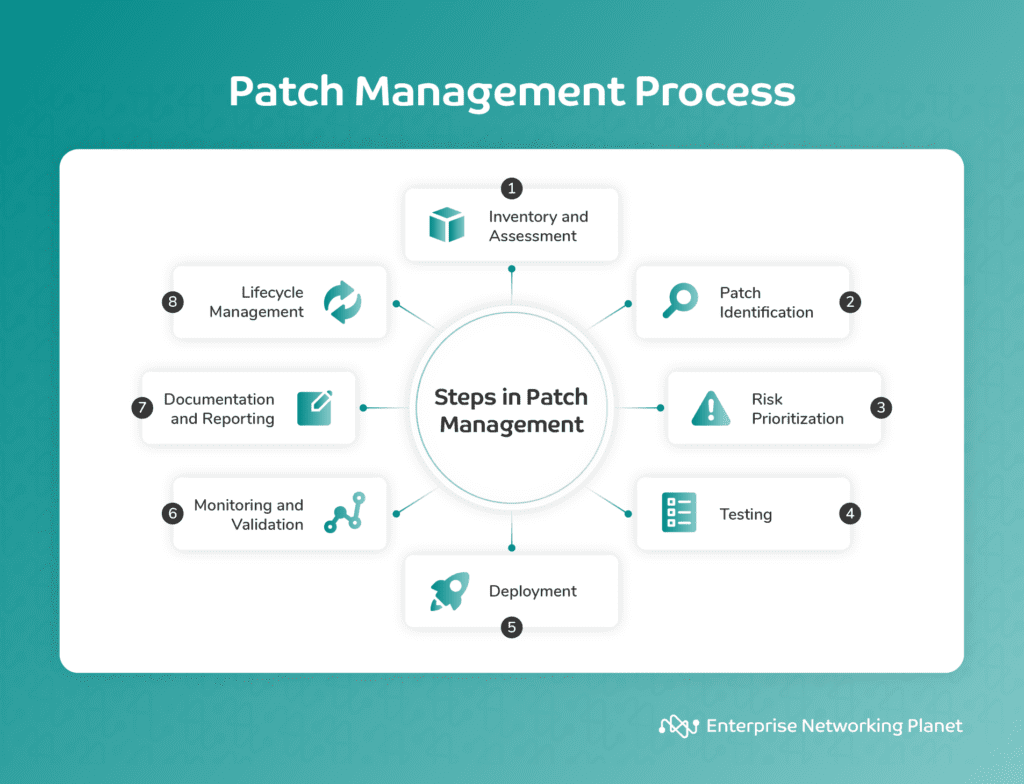
1. Inventory and assessment
The first step in the patch management process involves creating an inventory of all the software, hardware, and systems within your organization to clearly understand what you need to patch and secure. Simultaneously, you must assess these systems for vulnerabilities by conducting regular scans using automated tools or services. This initial step sets the foundation for effective patch management.
2. Patch identification
The next step is to identify the specific patches necessary to address the discovered vulnerabilities. This may entail closely monitoring sources like security mailing lists, vendor websites, and other reliable channels to stay informed about available patches. Your goal is to gather the updated patches from vendors, open-source communities, or patch-management-as-a-service providers.
3. Risk prioritization
Vulnerabilities don’t all carry the same level of significance, and some may pose a more substantial threat to your organization than others. In this step, prioritize the patches based on the severity of the vulnerabilities. It ensures addressing the most serious issues promptly, reducing the risk of exploitation by potential attackers.
4. Testing
Before deploying patches to your production environment, make sure you test them thoroughly. Establish a controlled, non-production environment, often referred to as a sandbox or test server, where you can apply the patches to determine if they cause any issues or conflicts with existing software or configurations. Successful testing helps mitigate the risk of disrupting your live systems.
5. Deployment
After thoroughly testing and validating patches in the controlled environment, it’s time to deploy them to your production systems. Manual deployment is possible for smaller environments, but automated patch management tools are often more ideal for larger, more complex systems for efficient and uniform distribution.
6. Monitoring and validation
Continuous monitoring is a vital step in successful patch application. Following deployment, monitor your systems for any irregularities, performance issues, or unintended consequences that may arise as a result of patching. Validation helps confirm that your systems remain secure and stable.
7. Documentation and reporting
Maintain accurate and comprehensive records of all patch management activities, including specific patches applied, when they were applied, and any issues encountered during the process. Generate compliance reports to track progress and alignment with industry regulations and internal policies.
8. Lifecycle management
The patch management process is not a one-time event but an ongoing, evolving effort. Regularly review and update your patch management process as new vulnerabilities and patches become available. This step also involves retiring unsupported software and replacing it with more secure alternatives. Educating your employees and users about the importance of promptly installing updates to maintain a secure and resilient IT environment is also part of lifecycle management.
Patch management security benefits
Patch management comes with many benefits, including reduced attack surface, malware spread prevention, automated security fixes, vulnerability mitigation, enhanced cyberattack resistance, data protection and network security, business continuity, and regulatory compliance.
1. Reduced attack surface
Patch management helps diminish the number of potential entry points or attack surfaces that a hacker could exploit. By regularly updating and patching software, you can fix known vulnerabilities, making it harder for hackers to gain unauthorized access. This applies to both proprietary and open source patch management solutions.
2. Malware spread prevention
Many types of malware take advantage of software vulnerabilities to infect systems and spread across networks. Regular patching can fix these vulnerabilities, making it much harder for malware to take hold and propagate.
3. Automated security fixes
Manual patching can be time-consuming and error-prone. Automated patch management reaffirms consistent and prompt patch application, decreasing the risk of human error. It implements security fixes as soon as they’re available, keeping systems secure.
4. Vulnerability mitigation
By applying patches as soon as possible, you close security gaps that could be vulnerable to attackers. Without this proactive approach from patch management, these vulnerabilities remain open doors for potential cyberattacks.
5. Improved resistance to cyberattacks
Timely patching makes it more challenging for cybercriminals to infiltrate your systems. By eliminating known vulnerabilities, you minimize the attack surface, making it harder for malicious actors to breach security protocols.
6. Data protection and network security
Securing a network and protecting sensitive data are fundamentally dependent on patch management. Without an effective patch management process, the likelihood of data breaches increases, which could lead to costly legal and reputational consequences.
7. Business continuity
Everything from bugs and errors to security breaches and cyberattacks can disrupt business operations, resulting in downtime and financial losses. Patch management helps maintain business continuity by making sure that your systems remain functional, available, and reliable, even when facing security threats.
8. Regulatory compliance
Many industries and regulatory bodies impose requirements on organizations to maintain compliant and secure networks. Patch management ensures adherence to these regulations. Non-compliance can lead to penalties and legal consequences.
7 patch management challenges for security teams
Security teams face some challenges in patch management, like patch prioritization, diverse systems and applications, legacy systems, user education and compliance, patch rollbacks, ongoing monitoring, and remote work.
1. Patch prioritization
With the rapid increase in IT vulnerabilities, security teams must decide which patches to apply first. This decision mostly depends on the severity of the vulnerability, the cruciality of the system, and the potential impact of the patch.
Accurately assessing these factors, fully understanding what patch management is, and making informed decisions requires expertise and resources. Furthermore, teams must balance the urgency of patching with the need to maintain system stability and avoid disruptions.
2. Diverse systems and applications
Organizations typically use a wide range of operating systems and third-party applications, complicating the process of managing and implementing patches, especially when it comes to Linux patch management.
Linux systems have distinct requirements and processes for patch management, which can be different from other operating systems like Windows or macOS. Ensuring that all systems receive the required patches is important for comprehensive security.
3. Legacy systems
Legacy systems frequently operate on outdated software, which heightens the risk of cyberattacks. These systems may also host major business applications, making updates or replacements costly and sometimes nearly impossible. The lack of vendor support for these systems means new patches may not be available.
In addition, organizations might not even be aware of the presence of these systems, complicating their management and patching processes.
4. User education and compliance
Educating users about the seriousness of timely patch installation is paramount, but often difficult due to a lack of understanding or awareness about cybersecurity risks. Users may also neglect or delay installing patches, which can leave systems vulnerable.
On the compliance side, verifying that all users adhere to patch management policies is a daunting task, especially in large organizations or those with remote or non-technical employees. Consistent communication and training are usually necessary.
5. Patch rollbacks
Sometimes, a newly applied patch may cause system instability or conflicts with other software. In such cases, security teams need to roll back or reverse the patch, which can be a complex process.
This requires having robust backups and procedures in place for reversing patches and upgrades. Moreover, the need to make sure that the rollback doesn’t affect system functionality or user experience adds to the complexity.
6. Ongoing monitoring
After assessing risks, testing, and performing vulnerability patching, continuous monitoring is necessary. You need visibility into any unpatched devices and ongoing protection from a vulnerable device. The steady influx of new patches and the need to keep an eye on a variety of devices and applications make this a challenging task.
7. Remote work
The increase in remote work means that many systems only connect to a domain occasionally. It can be difficult to check if the devices brought by employees or contractors receive patches before they access the organization’s resources.
How to implement patch management in 7 steps
Implementing patch management involves setting up inventory, creating a patch management policy, setting up testing environment, developing a deployment strategy, user education and training, compliance and auditing, and optimization.
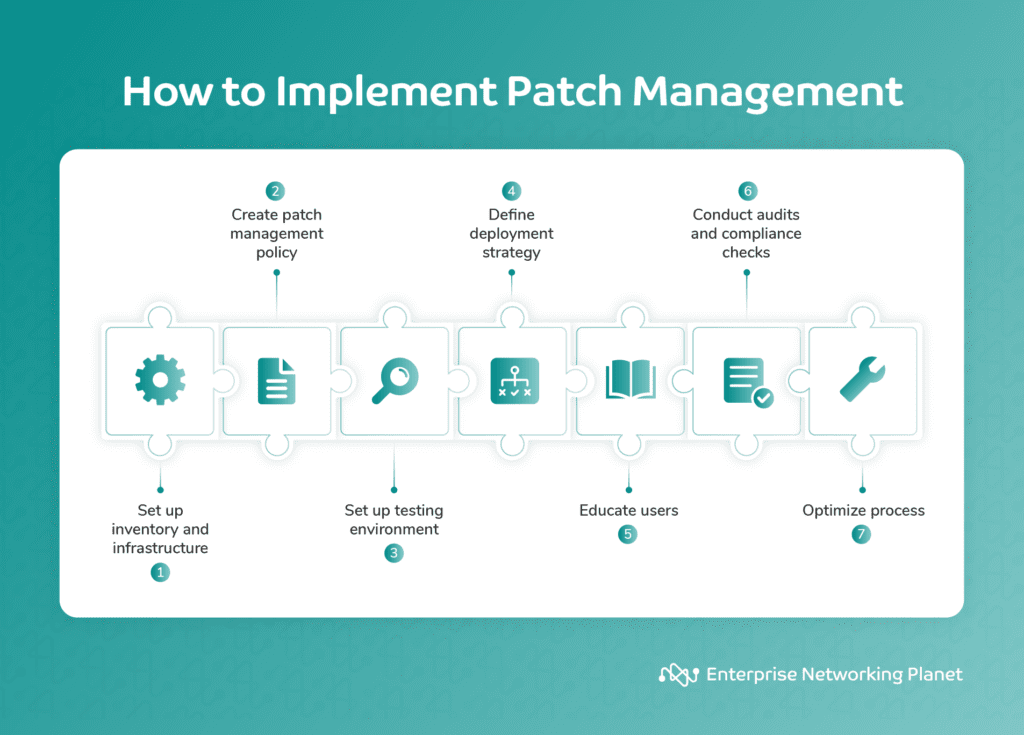
1. Set up inventory and infrastructure
First and foremost, your organization needs to create a comprehensive inventory of all software and systems in use. This includes desktops, servers, applications, and any other devices or platforms. You must also establish the required infrastructure to support your patch management efforts. This might involve acquiring the necessary hardware, software tools, and resources for effective patch management.
2. Create a patch management policy
A well-defined patch management policy is a prerequisite for clear guidelines and governance. Your organization should develop a detailed policy that outlines what patch management is in cybersecurity and how you will execute patch management.
This policy typically includes procedures for patch testing, deployment, and rollback. It should also define roles and responsibilities within your organization, specifying who is responsible for different aspects of the patch management process.
This way, everyone involved understands their roles and responsibilities, contributing to a more organized and efficient patch management process.
3. Testing environment setup
Creating a controlled testing environment or sandbox is indispensable for safely testing patches before deployment to production systems. This environment should mirror your production setup as closely as possible. It allows your team to assess how patches may affect your actual systems without risking disruptions or unexpected issues.
4. Build deployment strategy
A clear deployment strategy, clearly aligned with patch management best practices, defines the application of patches to production systems. Consider factors such as the organization’s size and complexity and the criticality of patches when determining your deployment strategy.
It’s also imperative to select the best patch management software for your organization to facilitate smooth and secure patch distribution.
5. User education and training
Educating end users and employees about the patch management process and its significance is another key component of successful implementation. Clear communication and training programs should be set to inform users about the significance of prompt updates and compliance with patch management policies.
6. Compliance and auditing
Careful examination of applicable regulations and the development of strategies to meet compliance criteria is a mandatory step. By preparing for audits and assessments, your organization can demonstrate its commitment to adhering to industry standards, potentially reducing the risk of penalties for non-compliance.
7. Optimization
Ongoing enhancement is the key to the long-term success of patch management. Evaluate the process and identify areas for improvement after each patch cycle. Fine-tuning your process could entail optimizing procedures and streamlining workflows. This guarantees that your organization’s patch management practices remain functional and evolve with changing security requirements and technologies.
Patch management vs. vulnerability management
While patch management and vulnerability management both pertain to computer or network security, they serve distinct purposes. Below is a comparison chart with an overview of how they differ in focus, objective, responsibilities, lifecycle, user involvement, compliance, dependency, frequency, and scope:
| Aspect | Patch management | Vulnerability management |
|---|---|---|
| Focus | Applying patches to known vulnerabilities | Identifying and mitigating vulnerabilities |
| Objective | Close security gaps through patching | Proactively find and address weaknesses |
| Responsibilities | Patch identification, testing, deployment | Vulnerability scanning, assessment, remediation |
| Lifecycle | Continuous and cyclical | Ongoing and continuous |
| User involvement | Emphasizes user compliance | Requires user awareness and reporting |
| Compliance | Required for regulatory compliance | Supports compliance but broader in scope |
| Dependency | Relies on vulnerability identification for effective patching | Independent, complements patch management |
| Frequency | Frequent (after every patch release) | Continuous with periodic vulnerability scans |
| Scope | Specific software and systems | Wide range of software and systems |
Top 3 patch management software
There are many reputable patch management software providers with advanced capabilities and integrated functionalities that can help your organization streamline the patching process. Here are some of the best patch management software solutions in 2023:
Automox
Automox is a well-regarded IT automation platform that excels in patch management, securing, and updating Windows, macOS, and Linux endpoints. It stands out for its ability to automate the process of scanning and cataloging devices within a unified platform.
This solution is user-friendly with a quick start-up time. It also supports multiple platforms, simplifying patching and software deployment tasks. As a cloud-based solution, it enforces OS and third-party patches along with security configurations globally.
However, Automox has some areas for improvement, including issues with time syncing between the server reports and the Automox console. Furthermore, the software doesn’t always always follow patching schedules.

ManageEngine Patch Manager Plus
ManageEngine Patch Manager Plus automatically deploys patches for Windows, macOS, and Linux endpoints and over 950 third-party applications. The software scans endpoints to find missing patches, tests them before deployment, automates deployment, and comes with in-depth auditing features for better visibility and control.
One of the key strengths of ManageEngine Patch Manager Plus is its scalability. It also has a remote push feature that manages multiple main and subsites. It covers nearly all end devices, simplifying monitoring the hardware status of devices.
However, there are some areas where it could improve. It offers limited customization options and has a complex agent deployment process.
Atera
Atera is an all-in-one IT management platform that delivers a wide range of features, including patch management. It provides IT professionals with access, visibility, and control over their networks and devices from anywhere.
This patch management solution brings real-time monitoring and automated patch management. It also displays information in a visual chart format for both servers and desktops, showing agents that are up-to-date and those that are not, as well as the number of missing patches in each agent.
Strengths of Atera include its one-stop-shop feature set, remote access, and intuitive ticketing management. It also integrates with third-party apps like Ninite Pro, IT Glue, and QuickBooks Online to expand its support features.
But just like other patch management software, Atera has some weaknesses, like having compatibility issues with some versions of Windows and Linux. It also gives limited control over the patching process.
Bottom line: Patch management explained
Patch management can be a complex and time-consuming process, but it can help keep your organization’s IT infrastructure secure. It is not just about closing security gaps; it’s about maintaining a strong overall defense against evolving cyberthreats.
Patch management comes with some challenges that security teams need to address too, like patch prioritization, diverse systems and applications, legacy systems, and remote work. To overcome these, you must develop a solid patch management strategy that includes everything from clear prioritization and diverse system support, to isolating legacy systems and adapting to remote work needs.
Fortunately, there are a number of patch management tools and resources you can use to aid with effective patch management, including automated patch management systems and network vulnerability scanning tools.
Patch management is not just a one-time task; it’s an ongoing commitment to reducing risks and proactively addressing security threats.
Selecting a reliable patch management software solution is as important as understanding the patch management process. Browse our analysis of the best patch management software solutions to learn more.


