Network vulnerability scanning tools play an integral part in successful vulnerability management by proactively identifying and evaluating security weaknesses within a network. By pinpointing vulnerabilities like outdated software or misconfigured settings, these tools empower businesses to bolster their network security, thereby reducing the risk of data breaches and cyberattacks.
Network vulnerability scanning software also contributes to cost savings, ensures compliance requirements to various regulations and industry standards, and enables business continuity by minimizing the chances of network disruptions caused by security incidents.
Investing in network vulnerability scanning software can foster customer trust, as it showcases a commitment to security and can lead to more business opportunities.
Here are our selections for the best network vulnerability scanning tools for 2023:
- Qualys Vulnerability Management (VMDR): Best overall network vulnerability scanning software. (Read more)
- SolarWinds Network Vulnerability Detection: Best for large-scale network performance monitoring and management. (Read more)
- Tenable Nessus: Best for comprehensive network and web application scanning. (Read more)
- Nmap: Best free, open source network vulnerability scanning software. (Read more)
- ManageEngine Vulnerability Manager Plus: Best for IT management, including network and security. (Read more)
- Burp Suite: Best for web application security testing. (Read more)
Table of Contents
Top network vulnerability scanning software comparison
Below is a comparison table with an overview of what each vulnerability scanning software has to offer:
| Vulnerability scanning software | Types of scanning | Accuracy | Free version | Free version limitations | Starting price for paid version |
|---|---|---|---|---|---|
| Qualys Vulnerability Management (VMDR) | Network, Applications, OS | High | Yes | Full features (Community Edition) | Contact sales |
| SolarWinds Network Vulnerability Detection | Network, OS | High | No | N/A | $1,894 (period unclear) |
| Tenable Nessus | Network, Applications, OS | High | Yes | Limited features (Nessus Essentials) | $3,390/yr. |
| Nmap | Network | Moderate | Yes | Full features (Community) | N/A |
| ManageEngine Vulnerability Manager Plus | Network, Applications, OS | Moderate | Yes | Limited features (Free Edition) | $695/yr. for 100 workstations |
| Burp Suite | Applications | High | Yes | Limited features (Community) | $449/yr. per user |
Featured Partners

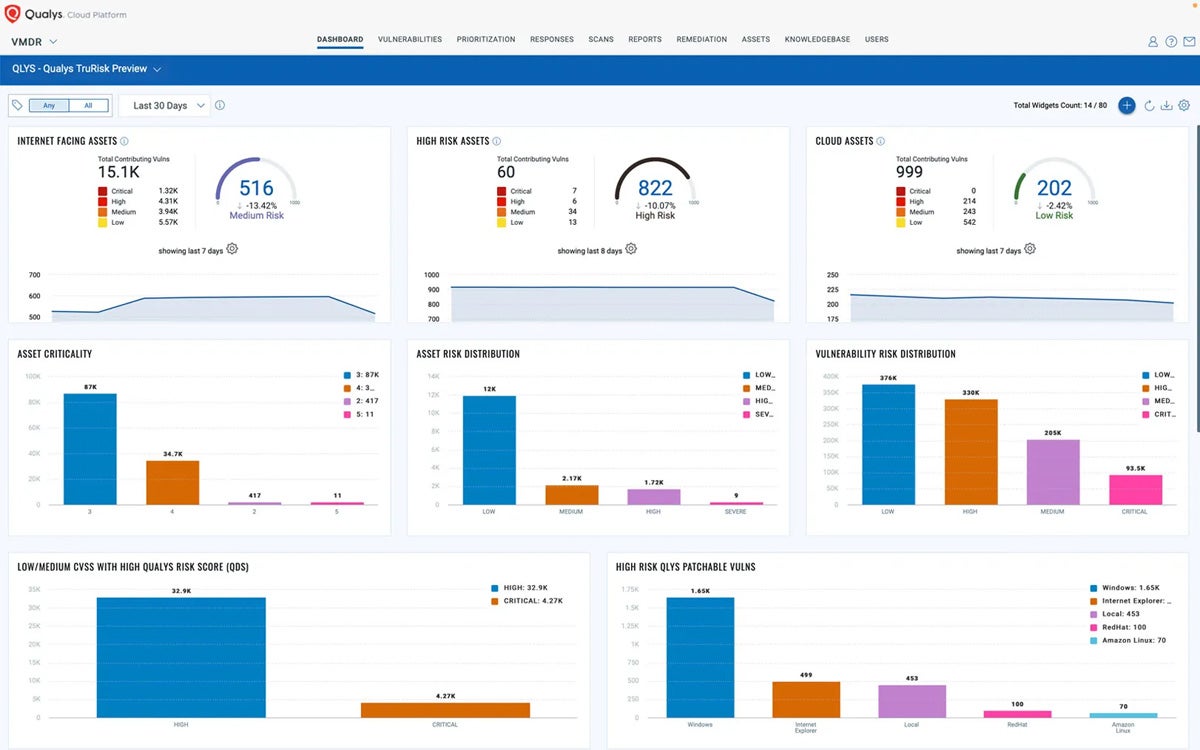
Qualys Vulnerability Management (VMDR)
Best overall network vulnerability scanning software
Overall rating: 4/5
- Cost: 2/5
- Core features: 4.5/5
- Customer support: 5/5
- Integrations: 4.25/5
- Ease of use: 3.75/5
Qualys VMDR is a key element of the Qualys suite, which offers a range of security solutions.
The primary function of Qualys VMDR is to scan your IT infrastructure for vulnerabilities by leveraging the Qualys Knowledgebase. This Knowledgebase continuously updates with thousands of Common Vulnerabilities and Exposures (CVEs) to make sure you’re always aware of the latest threats.
The tool provides detailed insights into your cyber risk exposure, allowing you to prioritize vulnerabilities based on business risk. This makes it easier for security and IT teams to align their efforts and quickly remediate risks.
In addition to vulnerability scanning, Qualys VMDR also offers asset visibility, giving IT teams a clear view of their global IT assets, both known and unknown. This integrated approach helps organizations measure their true risk and track risk reduction over time.
Pros and cons
| Pros | Cons |
|---|---|
| Simple implementation and deployment. | Requires technical knowledge to use. |
| Detailed explanations of the vulnerabilities and respective resolutions. | The interface is confusing for some users. |
| Wide range of features. | Unclear pricing. |
| SaaS offering. |
Pricing
Qualys VMDR has free (Community Edition) and paid versions. Its pricing depends on your selection of Cloud Platform Apps, the number of network addresses (IPs), web applications, and user licenses.
However, Qualys does not publish pricing details on its site and encourages customers to reach out to its sales team.
Features
- Asset discovery and inventory.
- Automatically scans internal and external networks.
- Adds threat and risk context to identify high-risk vulnerabilities.
- Performs risk scoring for suspicious activity and vulnerabilities.
- Delivers pre-built and custom reports and dashboards.
- Security testing tools.
- Ensures compliance with network security standards.
- Workflow automation.
- Perimeter scanning.

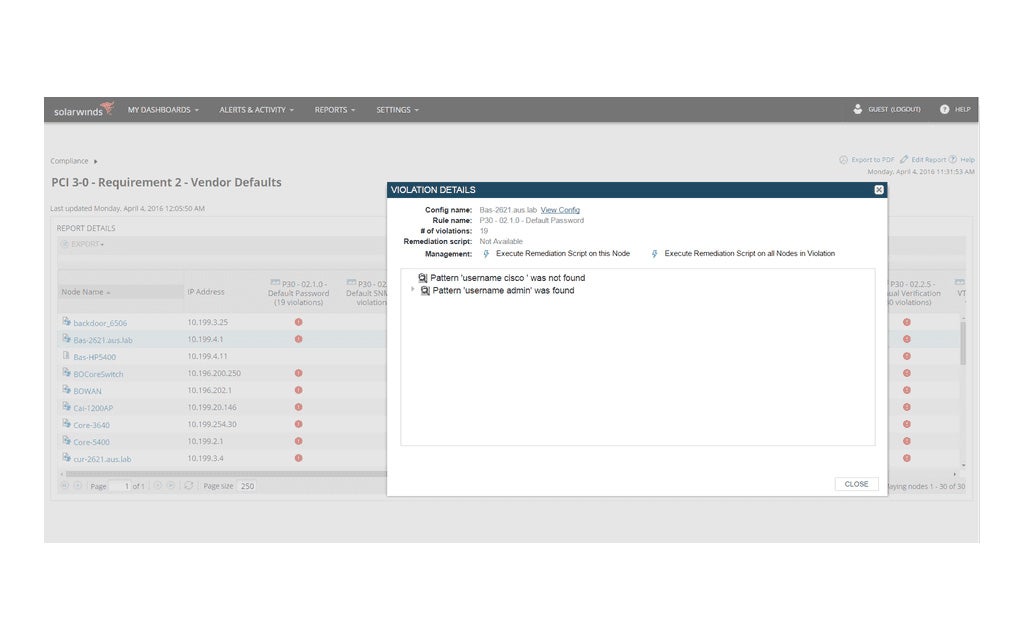
SolarWinds Network Vulnerability Detection
Best for large-scale network performance monitoring and management
Overall rating: 3/5
- Cost: 2.5/5
- Core features: 3.25/5
- Customer support: 4.5/5
- Integrations: 2/5
- Ease of use: 3.75/5
SolarWinds Network Vulnerability Detection, a feature of the Network Configuration Manager, specializes in enhancing network security and compliance. It scans network devices’ firmware for reported CVEs, helping to identify potential network vulnerabilities. The tool also uses network automation to quickly deploy firmware updates, so devices are always up-to-date.
If it detects vulnerabilities in multiple devices, it allows users to build, test, and administer a configuration change to all affected devices. It also delivers configuration backups and monitors configurations for changes, alerting users of any modifications and identifying the login ID used to make the change.
In addition, SolarWinds Network Vulnerability Detection blocks malicious IPs, patch vulnerabilities, and presents real-time actionable insights from your servers, endpoints, and applications.
Pros and cons
| Pros | Cons |
|---|---|
| Network automation rapidly deploys firmware updates to network devices. | Fewer third party integrations compared to competitors. |
| Prevents unauthorized network configuration changes. | Limited dashboard customization options. |
| Continuously audits configurations for any change that makes a device non-compliant. | Expensive compared to competitors. |
| Fast disaster recovery. | No free version. |
Pricing
SolarWinds Network Vulnerability Detection provides two licensing options:
- Subscription-based license: Starts at $1,894.
- Perpetual license: Starts at $3,671.
Get in touch with their sales team for a direct quote.
Features
- Scans network devices’ firmware for reported CVEs.
- Utilizes network automation to rapidly deploy firmware updates to network devices.
- Continuously audits configurations for any change affecting device compliance.
- Fast configuration updates.
- Builds configuration backups and monitors configurations for change, sending alerts on any configuration changes and the login ID used to make the change.
- Supports remediation script creation.
- Configuration change monitoring and alerting.
- Device configuration auditing.
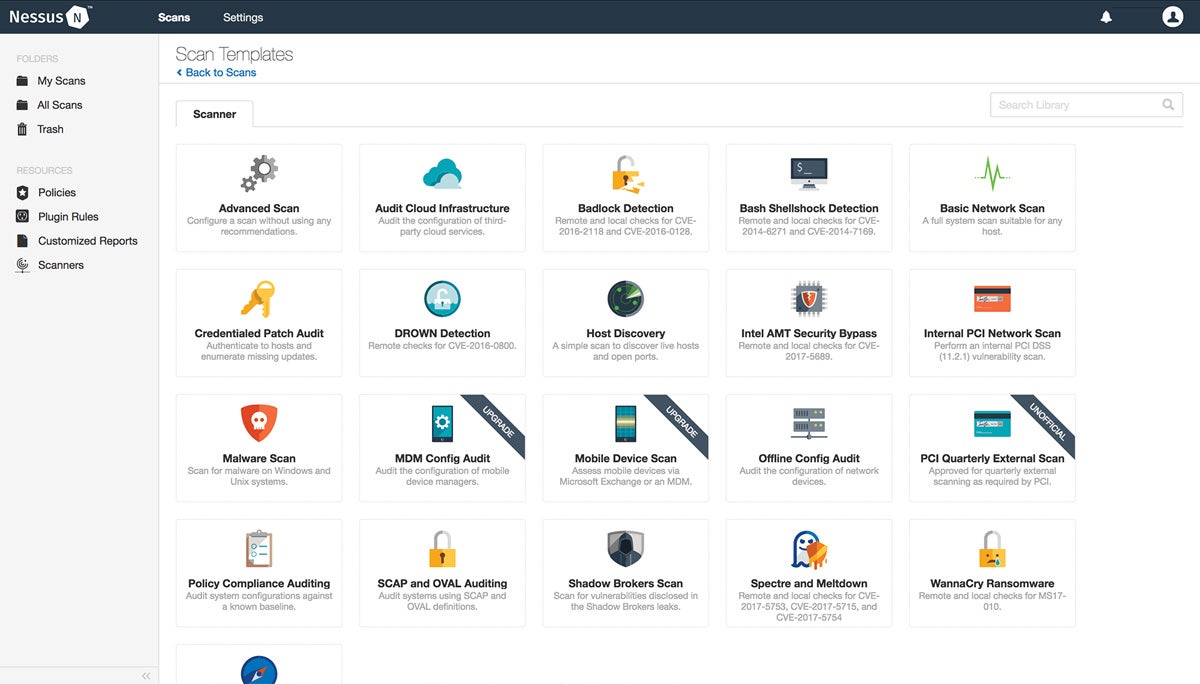
Tenable Nessus
Best for comprehensive network and web application scanning
Overall rating: 3.5/5
- Cost: 1.75/5
- Core features: 4.5/5
- Customer support: 3.5/5
- Integrations: 3/5
- Ease of use: 5/5
Nessus, developed by Tenable Network Security, is a network vulnerability scanner that allows organizations to find vulnerabilities, misconfigurations, and malware that attackers could exploit to penetrate their networks.
This network vulnerability scanning software works by testing each port on a computer, determining what service it is running, and then testing this service for any potential vulnerabilities. This thorough approach lets Nessus provide a detailed assessment of potential security risks.
Pros and cons
| Pros | Cons |
|---|---|
| Thorough scanning. | Support via email, chat, and phone are only available at additional costs. |
| Simple deployment and maintenance. | Integration capability depends on the subscription plan. |
| Highly scalable and can handle a large number of systems. | False positives in Ubuntu. |
| Extensive CVE coverage. | Scanning and reporting are time-consuming. |
Pricing
Nessus Tenable has a free version and two paid versions.
Nessus Essentials: This is available as a free download for students and educators and scans up to 16 IPs3.
Nessus Professional (Pro):
- 1 Year: $3,390 or $3,790 with advanced support.
- 2 Years: $4,660 or $5,460 with advanced support.
- 3 Years: $6,811.50 or $8,011.50 with advanced support.
Nessus Expert:1 Year: $4,990 or $5,390 with advanced support.
You can request a price quote from Tenable by getting in touch with their sales team.
Features
- Performs automated and scheduled security audits.
- Identifies security weaknesses in local and remote hosts.
- Conducts simulated attacks to uncover vulnerabilities.
- Detects missing security updates and patches.
- 500 prebuilt policies for exhaustive scans.
- Runs detailed scans on web applications.
- Scans and assesses your external attack surface.
- Facilitates scanning cloud infrastructure.

Nmap
Best free, open source network vulnerability scanning software
Overall rating: 2.75/5
- Cost: 5/5
- Core features: 2.5/5
- Customer support: 2/5
- Integrations: 1.5/5
- Ease of use: 2.5/5
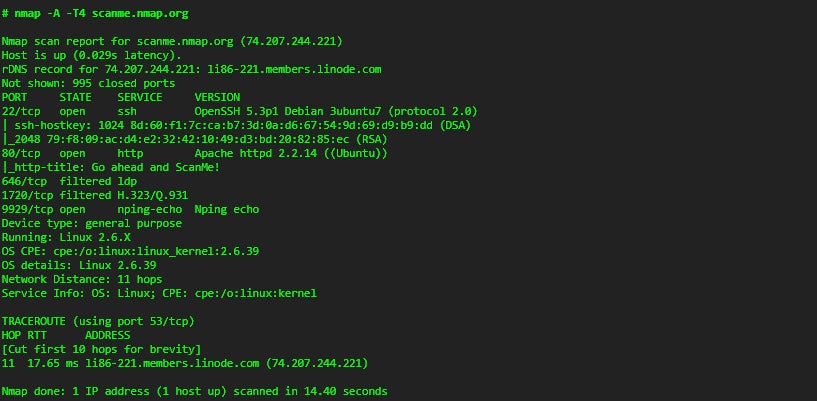
Nmap, short for “Network Mapper,” is a powerful and versatile open-source tool used for network discovery and security auditing. Security experts and ethical hackers typically use this vulnerability scanning tool.
Nmap uses scripts to scan for known weaknesses that cybercriminals could potentially leverage. These scripts are sets of instructions that the system executes. While Nmap comes with some scripts, you have the option to write your own scripts using a language known as Lua.
Pros and cons
| Pros | Cons |
|---|---|
| Complete vulnerability scanning. | Occasionally generates false positives in scan results. |
| Advanced reporting and remediation suggestions. | Steep learning curve. |
| Intuitive workflows. | Regular updates required for the latest vulnerability checks. |
| Supports most operating systems, including Solaris, Linux, Microsoft, and Amiga. |
Pricing
- Free and open source
Features
- Quickly identifies all devices, including servers, routers, switches, and mobile devices on a single or multiple networks.
- Scans and discovers open ports in a network.
- Pinpoints services running on a system, including web servers, DNS servers, and other common applications.
- Detects application versions with reasonable accuracy, aiding in identifying existing vulnerabilities.
- Presents detailed information about the operating system running on devices for penetration testing.
- Includes a scripting engine that allows users to write scripts for network discovery and vulnerability detection.
- Graphical user interface called Zenmap to show visual mappings of a network for better usability and reporting.

ManageEngine Vulnerability Manager Plus
Best for IT management, including network and security
Overall rating: 3.25/5
- Cost: 3.25/5
- Core features: 3.75/5
- Customer support: 4/5
- Integrations: 0.25/5
- Ease of use: 5/5
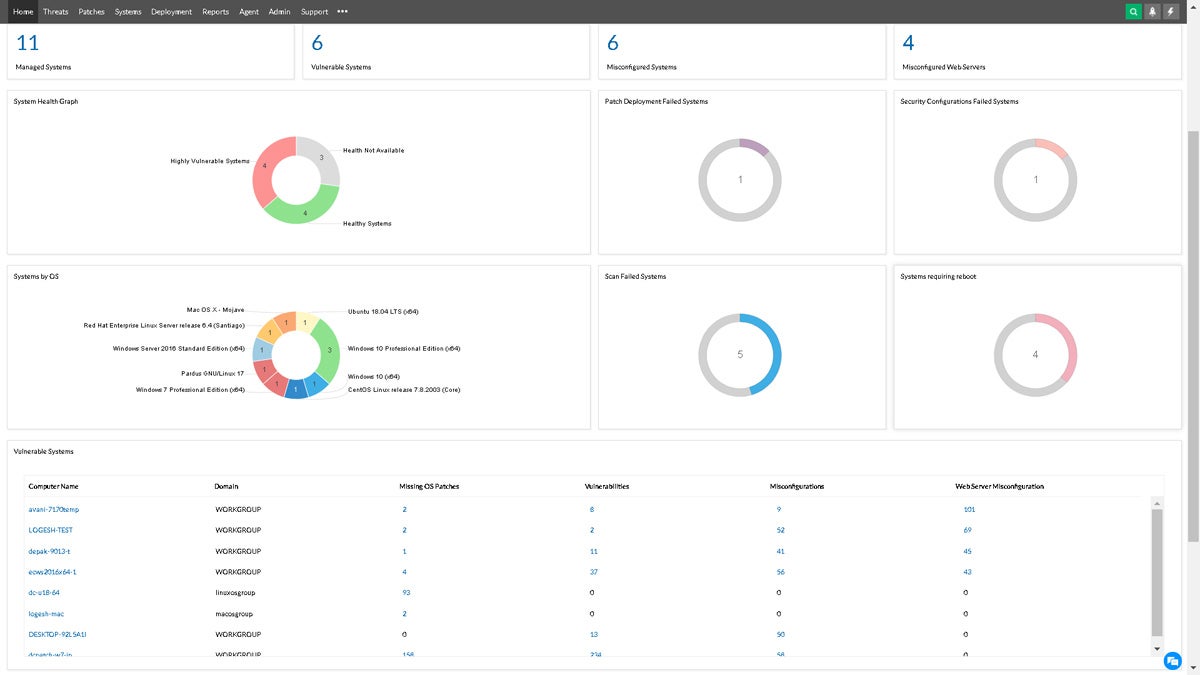
ManageEngine Vulnerability Manager Plus is an integrated vulnerability management and compliance solution that has end-to-end coverage of threats and vulnerabilities. It has built-in remediation and works across multiple operating systems.
The tool provides continual visibility into your security exposure, threat assessment, and vulnerability remediation from a single console. It can scan and discover exposed areas of all your local and remote office endpoints as well as roaming devices.
This vulnerability scanning software prioritizes vulnerabilities based on exploitability, severity, age, affected system count, and the availability of the fix. Additionally, it comes with patch management to customize, orchestrate, and automate your entire patching process.
Moreover, ManageEngine Vulnerability Manager Plus can harden web servers by supplying details on the cause, impact, and remedies of web server security flaws. It also audits high-risk software to identify and uninstall unsafe software from your endpoints.
Pros and cons
| Pros | Cons |
|---|---|
| Feature-rich freemium edition. | Only scans up to 50 clients for immediate patch deployment, impacting the vulnerability management speed |
| User-friendly. | SQL knowledge required for custom reports. |
| Zero-day vulnerability mitigation. | System has outdated patches that users must manually deploy for auto-updates. |
| Broad coverage. |
Pricing
ManageEngine Vulnerability Manager Plus is available in free and paid versions.
- Free version: Ideal for small businesses with up to 20 workstations and five servers.
- Professional: Annual subscription price of $695 for 100 workstations.
- Enterprise: Annual subscription price of $1195 for 100 workstations.
More pricing details are available here.
Features
- Discovers network devices, scans for firmware vulnerabilities, and remediates identified threats.
- Out-of-the-box policies to comply with over 75 CIS benchmarks, instantly identifies violations, and gives detailed remediation insights.
- Patch management for multiple Operating Systems and 250+ 3rd-party applications.
- Discovers network devices.
- Scans for firmware vulnerabilities.
- Keeps track of configuration drifts and deploys secure configurations.
- Identifies and mitigates zero-day vulnerabilities with prebuilt, tested scripts.
- Detects and remediates expired SSL, inappropriate web root directory access, and other web server flaws.
- Analyses and uninstalls unsafe, unauthorized, and unsupported software.
- Performs antivirus audit.
- Monitors the ports in use and processes running and uncovers unintended ports that may be activated by malware or unknown applications.

Burp Suite
Best for web application security testing
Overall rating: 3/5
- Cost: 3.5/5
- Core features: 3.75/5
- Customer support: 3/5
- Integrations: 2.25/5
- Ease of use: 2.5/5
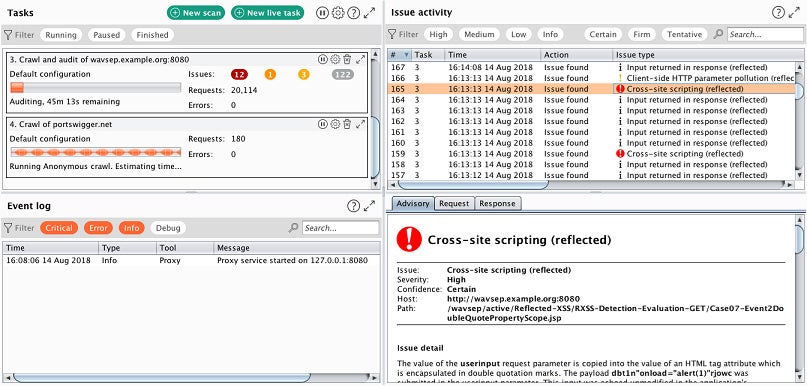
Burp Suite, an extensive platform developed in Java by PortSwigger, mainly concentrates on web application security penetration testing. It stands out in this context due to its unique features and strengths. Notably, the Burp Scanner, an essential part of the suite, is a robust automated tool that actively detects and exploits vulnerabilities in web applications.
What sets the Burp Scanner apart is its ability to mimic a human user’s actions, navigating through challenges like CSRF tokens and dynamic content. It demonstrates remarkable versatility, handling a wide array of API definitions and the large-scale complexity of modern web applications, even in less-than-ideal internet conditions.
Proactively sending numerous requests to the target application, the Burp Scanner excels at identifying and exploiting common vulnerabilities such as SQL injection, XSS, and CSRF. Over 70,000 users from more than 16,000 organizations actively attest to its reliability by placing their trust in this tool.
Pros and cons
| Pros | Cons |
|---|---|
| Powerful automated tools and workflows. | Primarily designed for web application security testing, not for network or OS scans. |
| Advanced reporting and remediation suggestions. | Steep learning curve. |
| Navigates and scans JavaScript-heavy single-page applications (SPAs) and APIs. | Resource-intensive. |
| Out-of-band application security testing (OAST) can find many otherwise invisible issues. | Limited OS support (compatibility issues with Linux and macOS). |
Pricing
Burp Suite has a free edition with basic features for manual security testing. For more features, two paid versions are available:
- Burp Suite Professional: $449 per user per year.
- Burp Suite Enterprise: $9,236 per year which includes five concurrent scans. Each additional concurrent scan will cost $659 per year.
Visit their pricing page for more details and discounts.
Features
- Intercepts and manipulates HTTP traffic between a web application and the client.
- Automated vulnerability scanning capabilities for identifying common web application security issues quickly.
- Web spidering tool that automatically navigates through a website, discovering and mapping its structure.
- Its Intruder tool automates the process of testing multiple payloads or inputs on a target.
- Its Repeater tool enables manual and iterative testing of individual requests.
- Collaborative testing features that facilitate communication among security professionals.
- Extensibility through BApps.
- Automated Out-of-band Application Security Testing (OAST) for finding a wider range of vulnerabilities.
- DOM Invader for simplified testing of DOM XSS vulnerabilities.
- Token strength assessment.
- Advanced/Custom automated attacks for deploying custom sequences of HTTP requests containing multiple payload sets.
- Automatically modifies HTTP messages.
Key features of network vulnerability scanning software
Network vulnerability scanning tools must have reliable scanning capabilities, accurate vulnerability detection, scheduled scanning, remediation guidance, and asset management features for them to work efficiently.
Broad scanning capabilities
A vulnerability scanning tool that features broad coverage thoroughly assesses an organization’s entire IT infrastructure. It scrutinizes network devices, software applications, and operating systems. By ensuring comprehensive coverage, the tool actively detects every potential vulnerability. This reduces security blind spots and minimizes the risk of exploitation.
Accurate vulnerability detection
Accurate vulnerability detection is critical for eliminating false positives and false negatives. It provides assurance that the identified vulnerabilities are legitimate security risks, which saves valuable time and resources. Reliable detection also helps in prioritizing and addressing the most urgent vulnerabilities first, improving overall security.
Scheduled scanning
Scheduled scanning automates the process, making it regular and consistent. This consistency is imperative for staying ahead of evolving threats and new vulnerabilities. By setting up regular scans, your organization can detect and address security weaknesses promptly, reducing the window of opportunity for potential attackers.
Remediation guidance
Network vulnerability scanning tools that bring remediation guidance are invaluable because they don’t just identify issues; they also offer actionable recommendations for fixing them. This guidance simplifies the process of resolving vulnerabilities, even for users who may not have extensive cybersecurity expertise, which ultimately leads to a more secure network.
Asset management
Asset management is vital for understanding the organization’s digital landscape. It helps in tracking all devices and software in use. This knowledge is foundational for effective vulnerability management as it guarantees that no asset goes unmonitored, letting you address vulnerabilities across the entire infrastructure.
How we evaluated network vulnerability scanning tools
We conducted extensive research and analysis to identify the top network vulnerability scanning tools for security teams in 2023.
First, we categorized our assessment into five primary areas: cost, core features, customer support, integrations, and ease of use.
We then broke down each criterion to define specific requirements and expectations for an ideal network vulnerability scanning software.
Afterward, we assessed and scored each tool based on its ability to meet the sub-criteria within each category. Finally, we computed the total scores for each software.
Cost – 20%
For this criteria, we considered a range of financial aspects to provide a clear understanding:
We assessed the duration of any available free trial, the availability of a free version of the software, as well as the usability of the free version without needing to transition to a paid plan.
Additionally, we considered the diversity of pricing models offered by the vendor, including subscription-based, perpetual licensing, and pay-as-you-go options. To complete this assessment, we examined the actual pricing and cost of the tool compared to competitors in the market.
- Category winner: Nmap
Core features – 25%
This category encompasses an in-depth assessment of various significant aspects of network vulnerability scanning, including scanning capabilities, vulnerability detection accuracy, built-in scanning scheduling, remediation guidance, penetration testing features, asset management, patch management capabilities, vulnerability management as a service features, vulnerability database update frequency, and the extensiveness of compliance support.
These factors collectively shape the core functionalities and capabilities of the network vulnerability scanning tools we evaluated, delivering a holistic view of their capability in addressing security challenges.
- Category winners: Qualys VMDR, Tenable Nessus
Customer support – 15%
In assessing customer support, we carefully examined the available support options, which include Live Chat, Phone, Email/Ticketing system, Community/Forums, and Knowledge Center/Documentation.
Our evaluation extended to factors such as the accessibility of each support type to all users, irrespective of their paid or free status. We also took into account the activeness of community resources and documentation. Moreover, we considered response times to check if customer support is prompt.
- Category winners: Qualys VMDR, SolarWinds Network Vulnerability Detection
Integrations – 20%
For integrations, we analyzed each network vulnerability scanning tool’s compatibility with a range of third-party tools, including Security Information and Event Management (SIEM) Systems, Ticketing and Issue Tracking Systems, Configuration Management Databases (CMDBs), Threat Intelligence Feeds, Patch Management Systems, Cloud Security Platforms, Network Scanners and Discovery Tools, and Web Application Scanners.
We also examined the tool’s support for custom integrations to measure flexibility for specific organizational needs. User feedback played a key role in our research, particularly regarding the ease of integration, offering insights into the practicality of connecting the tool with existing systems and applications.
- Category winners: Qualys VMDR
Ease of use – 20%
In our evaluation of ease of use, we explored the tool’s overall user experience, with a keen focus on its adaptability and simplicity in both deployment and operation.
We considered how approachable the tool is for users with varying levels of technical expertise, aiming to ensure that it has an intuitive and accessible experience. This criterion allowed us to determine the tool’s practicality across a diverse user spectrum.
- Category winners: ManageEngine, Tenable Nessus
Frequently Asked Questions (FAQs)
What is vulnerability scanning software?
Vulnerability scanning software is a specialized cybersecurity tool that probes an organization’s IT infrastructure, including network devices, software applications, and operating systems. Its main role is to systematically detect and assess weaknesses or vulnerabilities that malicious entities could exploit.
The software pinpoints these vulnerabilities and empowers organizations to enhance their security by addressing and rectifying these issues. This proactive identification and mitigation process reduces security blind spots and minimizes the risk of exploitation.
What are examples of common network vulnerabilities?
Common network vulnerabilities include:
- Unpatched or outdated software.
- Weak or default passwords.
- Insufficient access control.
- Misconfigured network services.
- Lack of encryption.
- Open ports and services.
- Phishing attacks.
- Denial-of-service (DoS) attacks.
- Inadequate firewall rules.
- Social engineering threats.
Bottom line: Network vulnerability scanning software is your security backbone
Network vulnerability scanning tools act as the critical backbone of any organization’s cybersecurity strategy. The extensive range of vulnerabilities, from common weaknesses to the most sophisticated exploits, calls for the use of reliable and advanced scanning software to safeguard sensitive information, systems, and networks.
Just like choosing other network security tools for your organization, selecting the right network vulnerability scanning software is a decision you should make with utmost care and consideration. Prioritize broadness, accuracy, and frequency of updates to make sure it can deal with emerging threats.
By making informed, strategic choices and investing in robust, up-to-date software, you can effectively fortify your network’s defenses, ensuring a safer and more secure digital future.
Vulnerability scanning is just the first step in securing your network. Dive deeper into the process with our guide to vulnerability management, and be sure to review our network vulnerability assessment checklist.





