Encryption software is a crucial cybersecurity tool that protects data by converting it into an unreadable format, requiring a decryption key for access. It acts as a digital lock, safeguarding sensitive business information like customer data, financial records, and proprietary knowledge from potential cyberthreats.
Unauthorized access to confidential data can result in severe financial losses and harm a company’s reputation. Investing in encryption software will help enhance your organization’s security and aid compliance with data protection regulations. Encryption tools are an indispensable asset for safeguarding business assets and maintaining customer trust.
Here’s our selection of the best encryption software data protection in 2023:
- ESET: Best overall encryption software. (Read more)
- NordLocker: Best for secure file storage. (Read more)
- LastPass: Best for password protection. (Read more)
- Carbonite: Best for cloud backup. (Read more)
- Trend Micro Endpoint Encryption: Best for diverse media encryption. (Read more)
- AxCrypt Premium: Best for file encryption. (Read more)
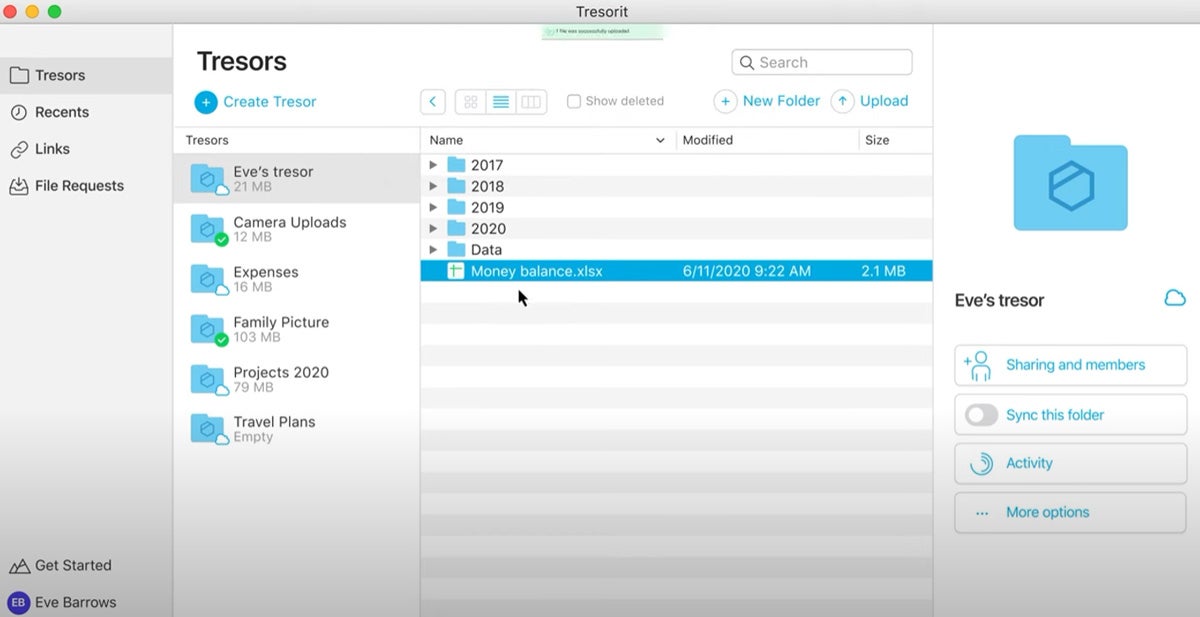
- Tresorit: Best for end-to-end encryption in regulated industries. (Read more)
Table of Contents
Top encryption software comparison
Below is a comparison table with an overview of the top encryption software for 2023. It presents each solution’s supported platforms, encryption algorithms, free version availability, and types of encryption it performs to give you an idea about the capabilities of each encryption software.
| Supported platforms | Encryption algorithms | Free version | Encryption types | Starting price | |
|---|---|---|---|---|---|
| ESET | Windows, macOS, Android, Linux | AES-256 | No | • File and folder encryption • Full disk encryption • Email encryption | $211/yr. for 5 devices |
| NordLocker | Windows, macOS, Android, iOS | AES-256, 4096-bit RSA, Argon2 | Yes | • File and folder encryption • Cloud storage data encryption • Database encryption | $11.88/yr. per user (100GB) |
| LastPass | Windows, Mac, iOS, Android, Linux, Chrome OS, Darwin, FreeBSD, OpenBSD | AES-256, PBKDF2 with SHA-256 | Yes, but very limited features | • Encryption within its password management services | $4/mo. per user |
| Carbonite | Win 7+, macOS 10.12+. Vault: Azure, Win Server 2019-2012 R2, SQL Server 2016-2012 | AES-128 to AES-256 | No | • File and folder encryption • Email encryption • Cloud storage data encryption | $24.00/mo. per user for up to 25 devices |
| Trend Micro Endpoint Encryption | PCs and Macs, laptops and desktops, USB drives, and other removable media | FIPS-compliant XTS-AES | No | • File and folder encryption • Full disk encryption • Email encryption • Cloud storage data encryption • Database encryption | Contact sales |
| AxCrypt Premium | Windows, macOS, Android, iOS | AES-256 | Yes, but limited features | • File and folder encryption • Cloud storage data encryption | $45/yr. per user |
| Tresorit | Windows 7 or later, Mac OS X 10.13 or later, Ubuntu 16.04+, Android 5.0 or later, iOS 12.2 or later | AES-256 in OpenPGP CFB mode | Yes | • File and folder encryption • Email encryption • Cloud storage data encryption | $14.50/mo. per user |

ESET
Best overall encryption software
Overall rating: 4/5
- Cost: 3.75/5
- Core features: 3.75/5
- Customer support: 4.75/5
- Ease of use: 5/5
- Integrations: 4.25/5
ESET encryption seamlessly integrates into the ESET PROTECT platform, providing a consolidated management environment for administrators. Its 256-bit AES encryption, validated under FIPS 140-2, ensures comprehensive data security for businesses of all sizes. This solution also simplifies management by letting admins oversee encryption on Windows machines and macOS (FileVault) from a single dashboard.
Additionally, ESET fortifies corporate network security by encrypting files, folders, emails, attachments, removable media, virtual disks, and entire disks. This holistic approach ensures the protection of sensitive data on corporate devices, reducing the risk of data breaches and loss.
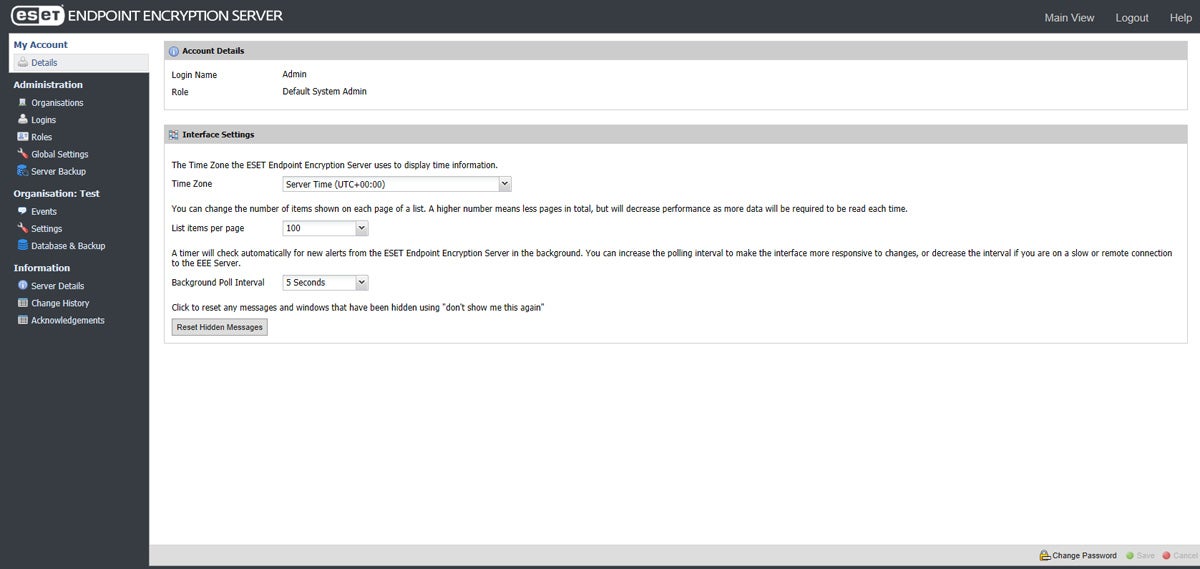
Pros and cons
| Pros | Cons |
|---|---|
| Multi-tenant management. | Infrequent updates. |
| User-friendly interface. | Complex setup for non-technical users. |
| Cross-platform coverage. | Device compatibility issues with Mac. |
| Supports email and attachment encryption through Outlook. |
Pricing
ESET offers four subscription plans and per-device pricing, with a minimum of five devices:
- Protect Entry: Starting from $211
- Protect Advanced: Starting from $220
- Protect Complete: Starting from $270
- Protect Elite (custom pricing for large enterprises): Minimum of 26 devices
For more details on pricing, contact their sales team.
Features
- Modern endpoint protection.
- Server security.
- Full disk encryption.
- Advanced threat defense.
- Cloud app protection.
- Mail security.
- Vulnerability and patch management.
- Detection and response.
- Multi-factor authentication (MFA).
NordLocker
Best for secure file storage
Overall rating: 3.25/5
- Cost: 4.75/5
- Core features: 3.5/5
- Customer support: 1.75/5
- Ease of use: 5/5
- Integrations: 1.5/5
NordLocker encrypts and stores your files in the cloud using advanced encryption standards like AES-256 and xChaCha20-Poly1305. It generates a random 256-bit key using Libsodium and secures that key with XChaCha20-Poly1305, using your master password.
This tool encrypts your files at all times, regardless of whether you store them locally or in the cloud. It operates on a zero-knowledge architecture, ensuring that only you and authorized individuals can access your files. NordLocker serves as a complete solution for securely storing and sharing files across various platforms.
Pros and cons
| Pros | Cons |
|---|---|
| User-friendly and convenient with drag-and-drop system to encrypt files. | Fewer features compared to competitors. |
| Automatic backup. | Limited customer service contact options. |
| Follows zero-knowledge architecture, limiting the risk of unwanted exposure. | Android and iOS apps are a bit clunky. |
| Has filename encryption. | Limited third party integrations. |
Pricing
NordLocker provides monthly and yearly plans. It has per-user pricing and cloud storage.
Monthly plans
- $3.29 per user/month (100GB)
- $13.29 per user/month (1TB)
- $15.69 per user/ month (2TB)
Yearly plans
- $11.88 per user/year (100GB)
- $47.88 per user/year (1TB)
- $56.28 per user/year (2TB)
This provider also has custom pricing. Get in touch with their sales department for full details on this.
Features
- Secure file sharing.
- Admin panel.
- Secure files from your web browser.
- Local and cloud lockers.
- Backup.
- Drag and drop functionality.
- Sync files across devices.

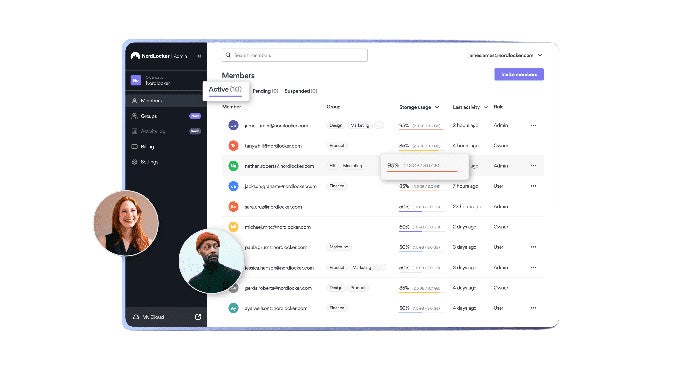
LastPass
Best for password protection
Overall rating: 3.5/5
- Cost: 4/5
- Core features: 1.25/5
- Customer support: 3.25/5
- Ease of use: 5/5
- Integrations: 5/5
LastPass, although not a traditional encryption software, incorporates solid encryption within its extensive password management services to boost online security. It securely stores and manages users’ passwords.
This software excels by allowing users to create complex and unique passwords for every online account. This feature eliminates the need to remember each password, a significant advantage in today’s digital age where an average internet user juggles numerous online accounts.
What sets LastPass apart is its advanced encryption technology. When you save a password in the system, your device encrypts it before sending it to LastPass servers. This process means that only your device can encrypt and decrypt your passwords. Your master password, which LastPass or anyone else does not know, is the key to this encryption. This encryption method adds an extra layer of security because even if someone gains access to the stored data, they cannot read it without the master password.
Pros and cons
| Pros | Cons |
|---|---|
| Compatibility with all major web browsers, as well as apps for Windows, iOS, Android, and macOS. | 24/7 email and phone support not available to all users. |
| Multi-device syncing. | Limited free version features. |
| Two-factor authentication. | Importing databases into LastPass is cumbersome. |
Pricing
LastPass has two monthly per-user pricing plans:
- Teams: $4 per user/month
- Business: $7 per user/month
Reach out to LastPass’s sales team to know more.
Features
- AES-256 encryption.
- Secure vault.
- File storage.
- Key management.
- Security dashboard.
- Form autofill.
- Secure digital wallet.
- Online password generator.
- Dark web monitoring.
- Online username generator.
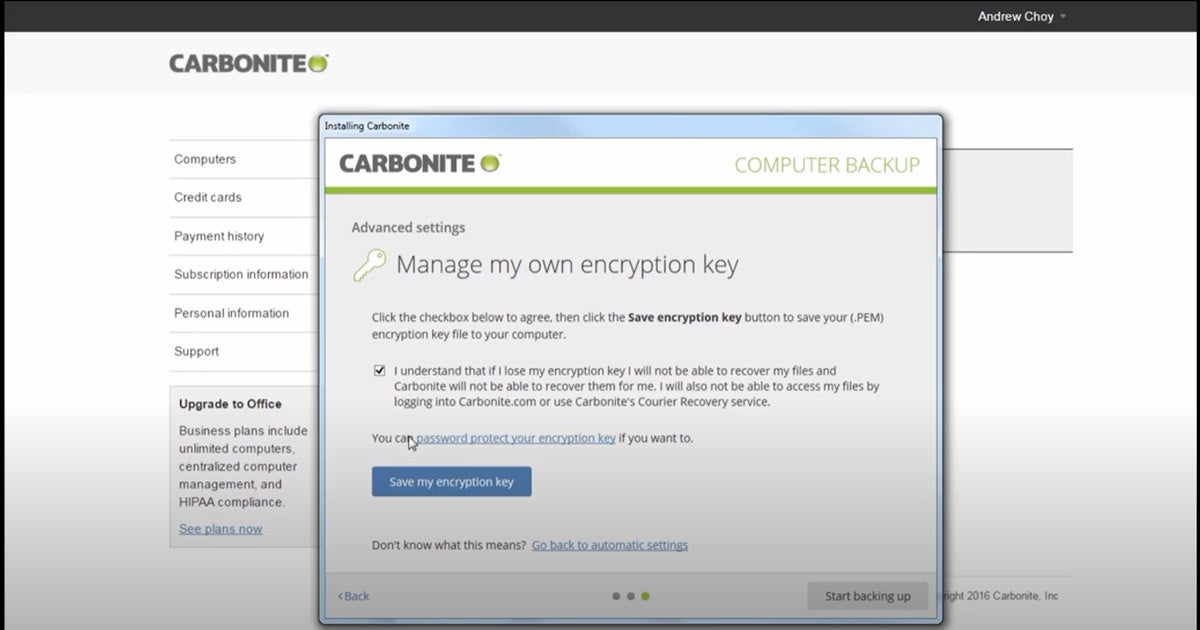
Carbonite
Best for cloud backup
Overall rating: 3.75/5
- Cost: 2.25/5
- Core features: 3.5/5
- Customer support: 3.5/5
- Ease of use: 5/5
- Integrations: 5/5
Carbonite, primarily a cloud backup service, prioritizes data security through its strong encryption features. Carbonite Safe Server Backup (CSSB) provides two encryption options: private key encryption and auto encryption.
The system enables auto encryption for all backups to the cloud by default. This process encrypts data before it leaves the user’s computer and then encrypts it again while it’s in transit to a Carbonite data center. This double layer of encryption secures data both at rest and in transit.
However, if you lose the encryption key file or forget the password, Carbonite cannot restore the data. Furthermore, you won’t be able to access files via Anytime Anywhere Access or the Carbonite Mobile app, nor can you request Courier Recovery.
Pros and cons
| Pros | Cons |
|---|---|
| Enterprise-grade backup solution. | Slow download speed when accessing data in the cloud. |
| Continuous backup. | Unlimited storage is only for one device. |
| Double encryption layer. | Data unrestorable by Carbonite in case of key loss. |
| Secure file access from any device, including mobile. |
Pricing
Carbonite has three pricing plans. All follow per user pricing and cover up to 25 computers.
- Carbonite Safe® – Core: $24.00 per user/month for up to 25 computers, external drives, and network attached storage (NAS).
- Carbonite Safe Server Backup – Power: $50.00 per user/month for one server and up to 25 computers.
- Carbonite Safe Server Backup – Ultimate: $83.33 per user/month for unlimited servers and 25 computers.
Book a consultation with the Carbonite sales team to find out more.
Features
- External hard drives and video backup.
- Courier recovery service.
- Configurable version control.
- Secure file access from any device.
- Protection for all file types.
- Private key encryption.
- Auto encryption.

Trend Micro Endpoint Encryption
Best for diverse media encryption
Overall rating: 3.75/5
- Cost: 0.75/5
- Core features: 5/5
- Customer support: 4.75/5
- Ease of use: 3.75/5
- Integrations: 5/5
Trend Micro Endpoint Encryption is a full data protection system that encrypts data on various devices, including PCs, Macs, laptops, desktops, USB drives, and removable media. It also brings encryption for full disks and files and folders. Moreover, it manages Microsoft BitLocker and Apple FileVault for added security.
This encryption software seamlessly integrates with other Trend Micro management tools, such as Control Manager and OfficeScan, delivering precise policy controls for better security management. It plays a key role in Trend Micro’s Smart Protection Suites, increasing data protection with features like data loss prevention (DLP), device control, and threat protection.

Pros and cons
| Pros | Cons |
|---|---|
| Centralized policy administration and transparent key management. | High resource consumption. |
| Protection for remote devices with tools to remotely lock, reset, or “kill” lost or stolen devices. | Time-consuming system boot. |
| Comprehensive data security for laptops, desktops, removable media, and mobile devices. | Unclear pricing. |
Pricing
Trend Micro Endpoint Encryption is part of Trend Micro’s integrated suites:
- Smart Protection for Endpoints
- Trend Micro Smart Protection Complete
However, the vendor does not provide clear pricing details on their page. Contact their sales team through this form to get full pricing information.
Features
- Integrated full disk, file folder, USB, and removable media encryption.
- Automated policy enforcement.
- Advanced reporting and auditing.
- Pre-boot authentication.
- Support for a consumerized environment.
- Regulatory compliance.
- Intellectual property security.

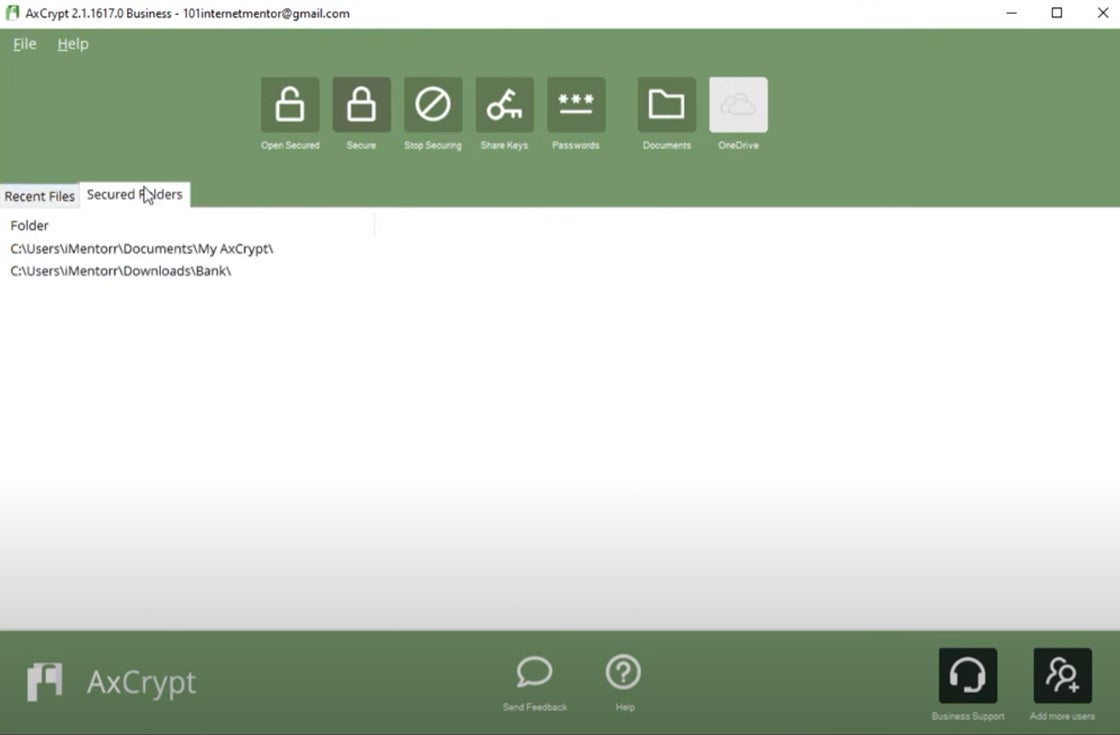
AxCrypt Premium
Best for file encryption
Overall rating: 3.75/5
- Cost: 5/5
- Core features: 3.5/5
- Customer support: 2.5/5
- Ease of use: 3.75/5
- Integrations: 3.75/5
AxCrypt Premium actively secures personal files across various platforms, including Windows, Mac, Android, and iPhone. It uses AES-256 encryption, the strongest variant of the AES algorithm, to safeguard sensitive and classified information.
This data encryption solution delivers key sharing for secure file sharing and works with cloud storage services like Dropbox, Google Drive, and OneDrive. Its hacker-proof encryption ensures your files are safe from cracking or theft.
The AxCrypt mobile app enables users to encrypt and decrypt files on their phones, providing security and accessibility anytime and anywhere. Furthermore, AxCrypt Premium comes with a password management feature and a password generator to guarantee the security of your passwords in the cloud.
Pros and cons
| Pros | Cons |
|---|---|
| Multi-platform support. | Manual adjustments needed for full security as default settings don’t encrypt all files. |
| Cloud storage awareness. | Limited features for free version. |
| Lock-tight password management. | Mobile editions can only decrypt files but can’t encrypt. |
| Multilingual. |
Pricing
AxCrypt has two subscription plans:
- AxCrypt Premium: $5 per user/month or $45 per year.
- AxCrypt Business: $12 per business user/month or $119 per year.
Set up an account to get started with AxCrypt.
Features
- Secured folders.
- Key sharing.
- Cloud storage awareness.
- Mobile encryption.
- Account key backup.
- Open shared keys.
- Password management.
- File wipe.
- Anonymous file names.
- Password generator.
Tresorit
Best for end-to-end encryption in regulated industries
Overall rating: 3.75/5
- Cost: 4.75/5
- Core features: 3.75/5
- Customer support: 3.75/5
- Ease of use: 1.25/5
- Integrations: 4.5/5
Tresorit, a cloud-based storage service, secures data using end-to-end encryption with AES-256 and TLS. It encrypts files on your device and maintains this encryption until the intended recipient receives them, preventing unauthorized access during transit.
Tresorit holds various compliance certifications such as GDPR, HIPAA, CCPA, TISAX, FINRA, and ITAR, making it an ideal choice for businesses in regulated industries.
In terms of usability, Tresorit works with several third-party tools and services like Microsoft Azure, Twilio, SendGrid, Zendesk, Salesforce, DocuSign Inc., and ProductBoard Inc. It also introduces an email encryption add-on for secure email communication.
Pros and cons
| Pros | Cons |
|---|---|
| Administrative reports and analysis. | More expensive compared to competitors. |
| Supports a wide range of platforms including Windows, Mac OS, Linux, Android, iOS, and major web browsers. | Complex setup. |
| Enables secure file exchange with external users. |
Pricing
Tresorit offers two pricing plans for teams with a minimum of 3 users.
- Business Standard: $14.50 per user/month.
- Business Plus: $19 per user/month.
This vendor also has custom pricing for enterprises with at least 50 users. Contact Tresorit sales team for exact details.
Features
- Encrypted storage.
- Multi-platform.
- Sync across devices.
- Offline access.
- Redundant storage.
- ISO 27001 certification, GDPR, TISAX, and FINRA compliance.
- Zero-knowledge system.
- Tresorit Drive integration to file manager.
- Data residency.
- Secure file sharing.
Key features of encryption software
Encryption tools must have critical features to ensure reliable data protection across various use cases, from individual files to entire databases and cloud storage. These core features include file and folder encryption, full disk encryption, email encryption, cloud storage data encryption, database encryption, encryption strength, key management, and security auditing and compliance.
File and folder encryption
This feature allows users to encrypt individual files or folders on their devices, adding an extra layer of security for sensitive data at rest. It makes sure that only authorized users with the decryption key can access private information, preventing unauthorized access and defending against identity theft.
Full disk encryption
Full disk encryption guarantees protection for all data on a storage device, such as a hard drive or SSD. This is imperative for data security if the device is lost or stolen because it makes it difficult for unauthorized individuals to access any stored data, thereby avoiding data breaches.
Email encryption
Email encryption safeguards the content of email messages and attachments, preventing illegal access during transmission. As a result, only authorized recipients can read the email’s content, averting data exposure of sensitive data to unauthorized parties.
Cloud storage data encryption
This protects data stored in cloud services, making sure that data remains safe even if the cloud provider’s infrastructure experiences a security breach. Cloud storage data encryption is particularly useful in protecting against corporate espionage.
Database encryption
Database encryption prevents unauthorized access to the data itself, adding a layer of protection beyond access controls. It ensures that even if an attacker gains access to the database, the data will remain unreadable without the proper decryption key. It effectively addresses data breaches, insider threats, and SQL injection attacks.
Key management
Effective key management is required for maintaining the integrity of encrypted data. It includes key generation, storage, distribution, rotation, and protection against unauthorized access. Safely storing and managing encryption keys is necessary for different organizations, like in financial institutions handling client data.
Security auditing and compliance
The ability to audit and demonstrate compliance with security policies and regulations is a must. Security auditing tracks access and changes to encrypted data, while compliance features help organizations meet legal and regulatory requirements. In addition, conducting regular security audits identifies system vulnerabilities and applies encryption requirements consistently across your organization.
Encryption strength
The strength of encryption algorithms and key lengths is a fundamental consideration. Strong encryption makes it computationally infeasible for attackers to decrypt data without the correct keys. Strong encryption is required to protect against cryptographic attacks, such as brute force attacks, cryptanalysis, and future-proofing. Additionally, it guarantees long-term data security.
How we evaluated encryption software
We identified and assessed the best encryption software for 2023 by conducting a thorough analysis focused on five key areas: cost, core features, customer support, ease of use, and integrations.
We defined specific criteria within each of these areas tailored to the unique requirements of a data encryption solution. We carefully examined and scored multiple encryption solutions against these criteria. Finally, we calculated overall scores for each encryption software systematically.
Cost – 25%
We evaluated the cost based on the availability and duration of a free trial and free versions of the software, subscription-based licensing, and per-user pricing options.
- Criteria winner: AxCrypt Premium
Core features – 30%
To assess the core features, we researched each solution’s encryption capabilities across various categories, including file and folder encryption, full disk encryption, email encryption, cloud storage data encryption, and database encryption. We also gauged each software’s encryption strength and availability of key management features.
- Criteria winner: Trend Micro Endpoint Encryption
Customer support – 15%
Several factors impact customer support scores, like the availability of customer support channels like live chat, phone, and email, along with an active user community and complete, user-friendly, and up-to-date documentation.
We also considered support response times and their availability for different customer tiers.
- Criteria winners: ESET and Trend Micro Endpoint Encryption
Ease of use – 10%
To determine the scores for this criteria, we collected both positive and negative feedback from numerous users from independent sites. We gathered reviews specifically from users of different technical skill levels to measure the user-friendliness and simplicity of implementation of the software.
- Criteria winners: ESET, NordLocker, LastPass, and Carbonite
Integrations – 20%
We meticulously assessed the integration capabilities of each software, considering factors such as the number of third-party tools it integrates with, its support for custom integrations, and the ease of the entire integration process.
- Criteria winners: LastPass, Carbonite, and Trend Micro Endpoint Encryption
Frequently asked questions (FAQs)
What file encryption is the strongest?
AES-256, which has a 256-bit key length, is the most robust encryption method. The key’s length heightens its security level to the point where current technology finds it virtually impossible to decrypt due to the required computational intensity.
What industries need encryption software the most?
Encryption software is necessary for several industries, but can be especially valuable for organizations handling sensitive data, like finance, healthcare, government, e-commerce, and technology.
What’s the difference between data encryption and network encryption?
Data encryption and network encryption are complementary security measures that work together to safeguard sensitive information. Both processes involve the use of cryptographic techniques to protect information, but they serve different purposes and operate at different levels within a computer network:
| Data encryption | Network encryption | |
|---|---|---|
| Purpose | Secures individual data at rest or in storage. | Secures data in transit over a network. |
| Scope | Focuses on securing specific files or data. | Applies to the entire network communication infrastructure. |
| Level of operation | Operates at the data storage or file level. | Operates at the network communication level. |
| Protection | Protects data from unauthorized access if it falls into the wrong hands. | Protects data as it travels between devices or nodes. |
| Encryption techniques | AES, RSA, DES. | SSL/TLS, IPsec, VPN. |
| Use cases | Encrypting files, databases, sensitive data at rest. | Securing web traffic, VPN connections, remote access. |
Bottom line: Not all data encryption solutions offer the same level of protection
Encryption software is a significant network security type that plays a pivotal role in protecting your data, files, and folders from unauthorized access, malware attacks, and data breaches. Whether you are an individual user or a business owner, you need to choose the best encryption software that suits your needs and preferences.
Choosing the best encryption software for your needs is not only important for your current data protection, but also for the future of your business. Data encryption solutions can help you comply with data privacy laws, prevent data loss, nurture customer trust, and improve your reputation. Therefore, you should invest in a high-quality encryption software that meets your expectations and requirements.
Some of the factors to consider when selecting an encryption software are encryption algorithm used, the ease of implementation and user-friendliness of the tool, its compatibility with third party devices and platforms, the features offered, and the price and customer support.
There are many encryption software solutions available in the market, but not all of them are equally reliable, efficient, and user-friendly. Compare the pros and cons of each option before making a final decision, and take advantage of free trials to get a closer look at your options.
Encryption software is a powerful tool for network security, but it’s just one piece of the puzzle. Get to know the many types of network security that work together to protect your data.


