DNS is the abbreviation for the “Domain Name System” and is essentially the phonebook system of the internet. It translates domain names such as “xyz.com” — human-readable queries that we type into browsers — into numerical IP addresses such as 154.6.147.47 (IPv4) or 2001:0db8:85a3:0000:0000:8a2e:0370:7334 (IPv6). The system is what allows internet users to access any of the billions of web pages daily — and DNS encryption ensures that any data they exchange remains private and secure.
This article will explain how encryption works, its benefits, and how to know if DNS encryption is configured on your browser and computing devices.
Table of Contents
The evolution of DNS encryption
In the nascent days of the internet when it was referred to as Advanced Research Projects Agency Network (ARPANET), address translation was achieved via a simple text file known as HOSTS.TXT. However, with the rapid growth of the internet, it quickly became apparent to researchers that the addressing system was finite. This scenario led to the birth of the modern DNS in 1983.
Initially, DNS was not built with network security in mind. And there is good reason for this — after all, there was no e-commerce, online banking, or pervasive data theft like we have today. Its original design was simply meant to address the problem of address scalability.
However, upon the realization of the internet’s potential and the dangers an insecure DNS posed, computer scientists scrambled to find a solution. The result was multiple standards and practices, the DNSSEC (Domain Name System Security Extensions), being retrofitted into the system to make it more secure.
Almost four decades after the invention of the DNS, two DNS encryption protocols were developed: DNS over TLS (DoT) and DNS over HTTPS (DoH).
How DNS encryption works: 2 different types
DNS encryption works by converting plain text DNS information into an encrypted version that only two parties engaged in the exchange of data — the DNS client (i.e., your browser or network devices) and the DNS resolver — can decipher.
DNS over TLS (DoT)
DoT is a security protocol created in 2016 to encrypt and protect DNS queries and responses using the Transport Layer Security (TLS) channel that secures HTTPS websites.
In this type of DNS encryption, the DNS resolver server authenticates itself to the client device through a certificate ensuring that no third party can impersonate the server. This authentication process guarantees the integrity and confidentiality of DNS traffic.
The main purpose of DoT is to enhance user privacy and security by preventing man-in-the-middle attacks, which could compromise or eavesdrop on DNS traffic. DoT operates over what is known as the user datagram protocol (UDP). It adds a layer of TLS encryption to secure DNS queries. The typical port for DoT is port 853.
While DoT provides security features, it’s important to note its potential limitations in jurisdictions with restricted freedom of speech. Enabling DoT encryption may inadvertently attract attention from authorities. Thus, it might not offer the intended protections against hostile or authoritarian regimes. Despite these considerations, supporters of the DoT protocol argue that it is better suited for addressing human rights concerns in challenging environments.
DNS over HTTPS (DoH)
Introduced in 2018, DoH is another protocol designed to make DNS queries more secure. Unlike DoT, DoH utilizes port 443 for HTTPS connections. It allows DoH clients and resolvers to connect to a DoH server that hosts a query endpoint.
Similar to DoT, DoH also relies on TLS for encryption. However, since it operates over HTTPS it seamlessly integrates with existing web infrastructure. This makes it less noticeable and potentially harder to block or filter in restricted environments.
Top risks of unencrypted DNS
To understand the importance of DNS encryption, it can help to examine the top risks of unencrypted DNS. Some of the original security threats identified by the Internet Engineering Task Force include:
- Packet interception: Because DNS queries and responses are often transmitted without encryption in text, unauthorized individuals can easily intercept data packets, thus giving attackers the ability to eavesdrop on the network and capture information. This includes the domain names being accessed, which can provide insights into user behavior or corporate activities.
- ID guessing and query prediction: DNS uses transaction IDs to match queries with their corresponding responses. In an insecure configuration, attackers can attempt to guess the transaction ID of a DNS query and, if successful, they can then send a response that redirects users to a malicious website.
- Name chaining: This tactic involves attackers querying for domain names under their control but appending the target domain as a suffix. The DNS resolver caches this information. When a genuine user subsequently queries the target domain the resolver mistakenly returns the attacker’s IP address instead, redirecting the user there without their knowledge.
- Trusted server betrayal: In this scenario, attackers gain control over a DNS server that is trusted by the targeted network. DNS resolvers inherently trust responses from these servers, which means that if any malicious data is sent it will be accepted and stored in the cache. This can lead to types of attacks such as cache poisoning or data theft.
- Denial of service (DoS): DNS servers are infrastructure components. An attacker can overwhelm a DNS server with a high number of queries, causing it to become unable to process legitimate requests. The result is that the ability to resolve domain names is disrupted, effectively making web services unavailable.
- Authenticated denial of domain names: This type of attack is more advanced, as the attacker not only floods the DNS server but also utilizes different authentication mechanisms to make it appear legitimate. Mitigating this attack is more challenging because it is extremely difficult to distinguish between legitimate queries.
- Wildcards: In DNS, wildcards are used to handle subdomains that have not been explicitly defined. An attacker can exploit this by injecting wildcard entries into a DNS server. When a user queries for an undefined subdomain, they are directed to the IP address specified in the malicious wildcard entry.
Other, more contemporary risks include:
- Cache poisoning: In these attacks, an attacker can manipulate the DNS resolver cache by inserting an unauthorized DNS entry. Consequently, users may unknowingly be redirected to other websites they had not actually visited.
- DNS amplification attacks: The lack of encryption in DNS opens the door for attackers to forge the source IP address in a DNS query. By doing so they can send a large volume of responses to a target IP address, intensifying the attack and overwhelming the target system.
- DNS tunneling: This involves encapsulating DNS traffic within DNS protocols. This allows bypassing network security measures since the DNS queries are not encrypted and can carry payloads that are difficult to detect using standard security tools.
- Zone transfers: These transfers expose all the DNS records for a domain. Attackers can use this information as a resource for further attacks or reconnaissance activities.
- DNS hijacking: Attackers can modify unencrypted DNS configurations on a user’s device. This enables them to redirect users towards websites and potentially capture sensitive information during the process.
- Subdomain takeover: When unencrypted DNS records direct to resources that are no longer active (like a cloud service that has been decommissioned), an attacker can exploit it to gain control over that resource, and consequently the subdomain associated with it, to serve harmful content.
- Information disclosure: Unencrypted DNS queries can unintentionally reveal details about network structure. Attackers may exploit this information for reconnaissance purposes, enabling them to plan precise and targeted attacks.
6 benefits of DNS encryption
The benefits of DNS encryption are numerous for enterprises, small and mid-sized organizations, and even individuals. These benefits extend from financial and identity protection to superior defense against a variety of cyberattacks.
Financial protection
According to a 2023 report by IDC, the average financial impact of DNS attacks has escalated to $1.1 million per incident. DNS encryption serves as a financial safeguard by reducing the risk of costly data breaches and unauthorized data access.
Enhanced security against sophisticated attacks
Radware’s threat advisories indicate a rise in DNS flood attacks, which aim to overwhelm DNS servers with high volumes of requests. DNS encryption adds a layer of security that makes it more challenging for attackers to manipulate or intercept DNS traffic, helping to protect against such sophisticated attacks.
Integrity and confidentiality
DNS encryption ensures the integrity and confidentiality of DNS data. This is particularly crucial due to the emergence of advanced HTTP and DNS DDoS attacks employing techniques previously exclusive to nation-state actors. By encrypting DNS queries, organizations can be assured that they are interacting with the intended servers.
Mitigation of DNS spoofing and man-in-the-middle attacks
DNS spoofing and man-in-the-middle attacks are common techniques used in advanced DNS attacks, whereby the client is directed to a facsimile of the intended web page, where they then enter important data such as passwords or payment information. DNS encryption effectively mitigates the risks associated with these attacks by ensuring that DNS queries can’t be intercepted, read, and redirected by malicious actors.
Proactive defense strategy
As DNS attacks continue to evolve in complexity and scale, DNS encryption offers a proactive measure to secure DNS queries. It is not just an optional feature but a necessary component in a comprehensive cybersecurity strategy.
Reputation management
The reputational damage following a DNS attack can be devastating for enterprises. DNS encryption helps in maintaining the trust and credibility of an organization by ensuring the security and integrity of its DNS queries.
How to check and adjust your DNS encryption
Most modern web browsers, like Chrome, Firefox and Edge have a feature that lets users customize their DNS encryption settings. Typically you can find these settings by going to the “Settings” menu and then selecting “Privacy and Security.” It is important to note that the exact steps might be slightly different depending on the specific browser you are using.
For operating systems such as Windows 10 and newer versions, macOS, and Ubuntu, it’s often possible to configure DNS encryption settings at the system level. This means you can secure your DNS queries beyond web browsing activities. To adjust these settings it’s best to refer to your operating system’s documentation or support resources for detailed instructions.
Both Android and iOS smartphones have built-in support for DNS encryption. You can usually access these settings through the network or privacy options on your device.
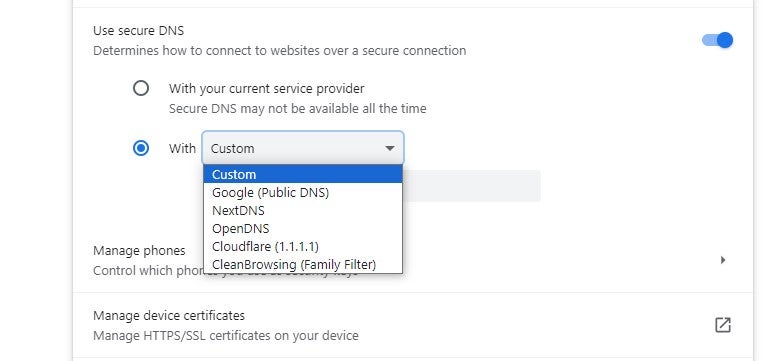
Google Chrome
Google Chrome supports DoH and allows users to enable it manually. However, it is important to mention that Google Chrome employs a unique approach to DoH implementation. It doesn’t automatically switch to DoH but rather checks if the user’s existing DNS provider supports DoH. If it does, Chrome upgrades the DNS queries to DoH while retaining the user’s chosen DNS provider. This ensures a seamless transition to more secure DNS queries without altering user settings.
To manually check and activate DoH in Chrome:
- Navigate to Settings.
- Go to the Privacy and Security tab.
- Scroll down to Advanced.
- Where it says “Use secure DNS,” enable the feature by choosing a DNS provider from the dropdown menu or adding a custom provider.
Chrome comes preconfigured with several DoH providers such as Google DNS, Open DNS, and CloudFlare.
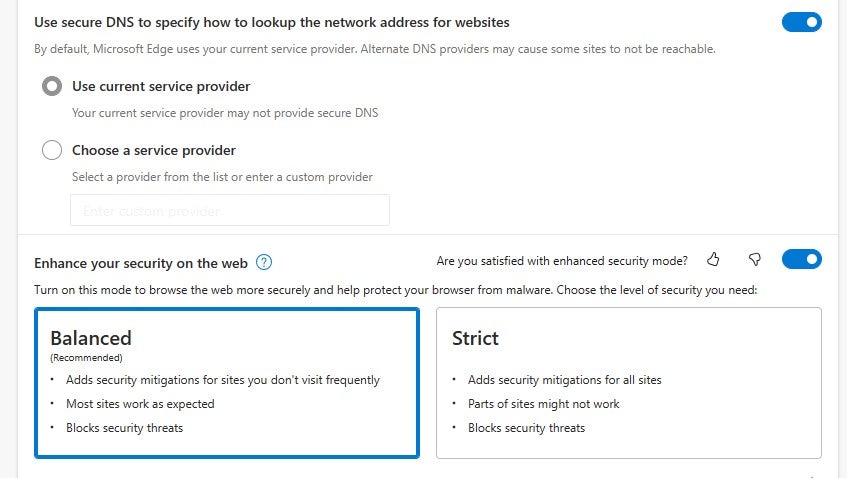
Microsoft Edge
Edge also allows users to manually configure DoH. To do so:
- Navigate to your browser’s settings under the “Privacy, search, and services” section.
- Select a custom DoH provider or disable the feature altogether.
Note that Edge is also preconfigured with several DoH providers.
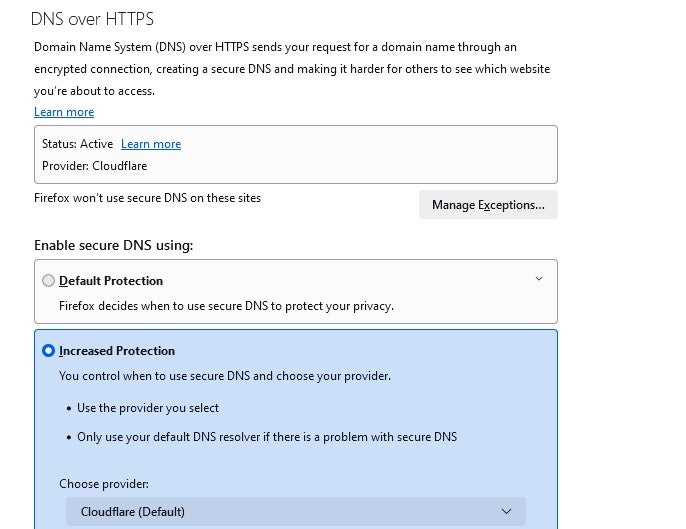
Firefox
Mozilla Firefox was one of the first browsers to implement DoH and even made it the default for users in several countries. You can enable or disable it through the browser’s settings under “Network Settings.” When you choose increased protection, Firefox defaults to a specific DoH provider, Cloudflare, although users can change this in the settings.
- Navigate to Settings.
- Go to the Privacy & Security tab.
- Scroll down to DNS over HTTPS.
- Select Increased Protection under “Enable secure DNS using.”
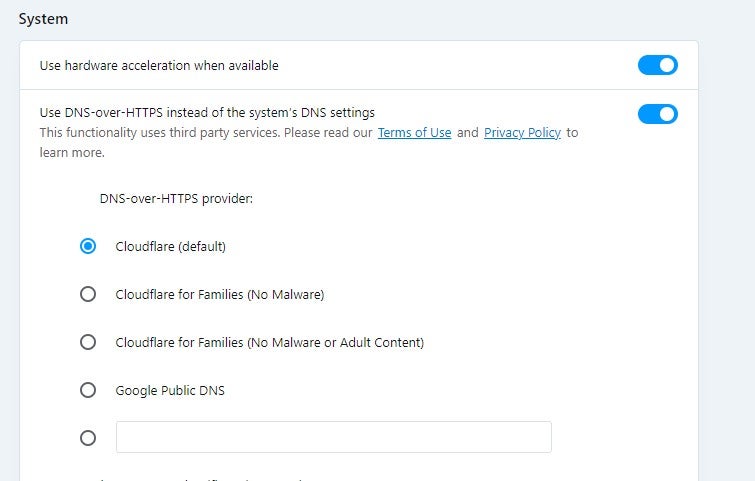
Opera
Users can enable DoH in Opera through the browser’s settings under the “Privacy & Security” section. This allows users to either use the default DoH provider or input a custom one. To check your DNS encryption settings:
- Navigate to Settings.
- Go to the Privacy & Security tab.
- Scroll down to System.
- Toggle the radio button.
Opera also uses Cloudflare by default for DoH.
Operating systems
- Windows: Support for DoH is being developed by Microsoft for Windows 10 and above. While users can currently configure DoH in the OS settings, this feature is still in its early stages and not yet widely adopted.
- macOS: For macOS users Apple has introduced encrypted DNS options starting with macOS Big Sur. Users can enable DoH in the system settings under network options, allowing system support for DoH.
- Ubuntu: Ubuntu users have the option to install and configure a DNS resolver like dnscrypt proxy to enable DoH. This provides a technical approach suitable for users comfortable with command-line interfaces.
Implementing DoH at the OS level ensures that all applications benefit from DNS queries, extending security beyond just web browsers. However, setting it up may require technical expertise.
DNS encryption on Android
In Android you can implement DNS encryption by using either DoT or DoH. Starting from Android 9 (Pie) the OS comes with built-in support for DNS over TLS. This means that all DNS queries made from the device can be encrypted, regardless of the app generating those queries.
To enable this feature users can navigate to Settings >. Internet > Advanced > Private DNS.
From there they have several options to choose from, including automatic selection (where Android will try to use DoT with your current DNS server), turning it off completely (which disables DoT), or entering the hostname of a DNS server that supports DoT.
DNS encryption on iOS
With iOS 14, Apple introduced support for DNS. Users now have the option to use either DoH or DoT to encrypt their DNS queries.
Configuring the settings for DNS encryption on iOS is not as straightforward as it is on Android. Generally, these settings are configured through profiles that are often installed via mobile device management (MDM) solutions or manually set up using a configuration profile.
Some third-party apps also provide methods for setting up encrypted DNS on iOS devices. After installing a profile or setting up an app, the DNS settings are applied throughout the system, providing a layer of security that benefits all apps.
Bottom line: DNS encryption is a critical component of cybersecurity
DNS encryption is an indispensable security measure in today’s cyber landscape. It offers a robust defense against various cyberthreats, including DNS spoofing, man-in-the-middle attacks, and data exfiltration. The adoption of DNS encryption protocols like DoT and DoH is increasingly becoming a standard best practice, not just an optional feature.
Given the escalating threats targeting DNS, as evidenced by recent cyber threat intelligence reports referenced earlier, implementing DNS encryption is not merely advisable but essential for any organization committed to safeguarding its network and data.
Don’t stop at DNS: get to know the best encryption software for protecting data across your network.





