Cultivating a strong security posture begins with the following patch management best practices. Promptly addressing known vulnerabilities helps organizations reduce the risk of unauthorized access, malicious code execution, and operational disruptions.
Let’s explore essential network patch management best practices, including establishing a patch management policy, automating deployment, prioritizing urgent vulnerabilities, testing patches thoroughly, maintaining an updated inventory, creating a rollback plan, enforcing least privilege access, monitoring and auditing compliance, and training employees.
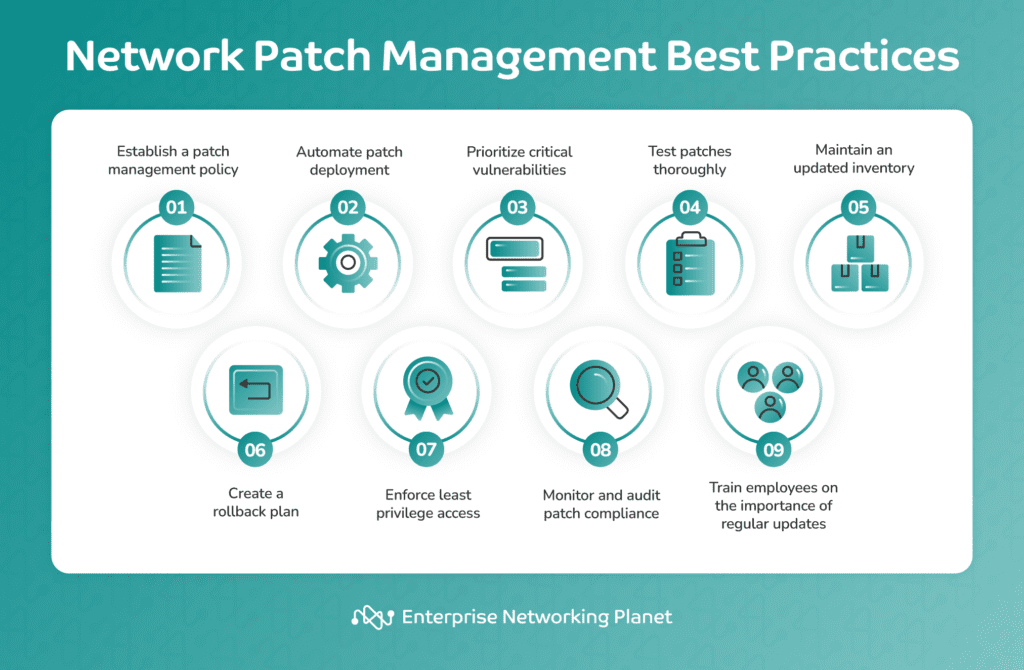
Table of Contents
1. Establish a patch management policy
A patch management policy gives a clear framework for how your organization will manage patches. It promotes consistency and accountability, and standardizes patch assessment and application procedures. It also aids in risk management, regulation compliance, and resource allocation. Furthermore, it facilitates communication and awareness regarding the entire patch management process.
Expert tips:
- Regularly review and update your patch management policy to check if it remains relevant and effective as your organization and technological needs evolve.
- Engage stakeholders in policy development.
- Clearly outline the roles and responsibilities of individuals involved in the patch management process.
2. Automate patch deployment
Using automated patch management tools for patch deployment supports the consistent and timely application of updates. Automation decreases the likelihood of human error and makes sure that security teams don’t miss any high-priority patches, thus improving the overall network security. Patch management software solutions like Acronis offer this feature.
Expert tips:
- Choose a software that fits your organization’s needs and scale. There are many reliable patch management solutions that can handle various types and system volumes you need to patch.
- Integrate patch deployment automation with SIEM systems to improve visibility.
- Develop and implement a test automation framework for patch deployment.
3. Prioritize critical vulnerabilities
By prioritizing the remediation of high-severity vulnerabilities, you ensure proper resource allocation to the most serious network security threats first. This minimizes the window of opportunity for potential attackers to exploit these vulnerabilities.
Expert tips:
- Use a vulnerability scoring system like the common vulnerability scoring system (CVSS) to help prioritize patching based on the severity of vulnerabilities.
- Form a cross-functional team involving members from IT, security, operations, and business units to collectively assess and prioritize critical vulnerabilities for a thorough understanding of both technical and business considerations.
- Adopt a risk-based approach to prioritize critical vulnerabilities based on their potential impact on the organization.
4. Test patches thoroughly
Rigorously testing patches in a controlled environment is vital before deploying them to production systems. This enables identifying potential conflicts, compatibility issues, or unintended consequences that could disrupt operations. Tools like ManageEngine Patch Manager Plus can help in this regard.
Expert tips:
- Conduct thorough testing in an environment that mirrors your production setup. This provides a realistic simulation of production conditions and helps meet compliance requirements in certain industries.
- Create detailed test cases and consider variations in operating systems, software configurations, and network environments within your organization.
5. Maintain an updated inventory
Keep a comprehensive inventory of all devices and software in your network, such as servers, workstations, and network appliances. Regularly update this inventory to reflect changes in your infrastructure to enhance the accuracy of targeting patches to the appropriate systems. SolarWinds Patch Manager can assist with maintaining an updated inventory.
Expert tips:
- Use automated asset discovery tools to ensure that you don’t overlook any devices during patching. These tools can greatly ease the manual effort required for inventory management, enabling IT teams to concentrate on tasks of higher strategic importance.
- Extend the inventory beyond a simple list of assets by capturing relationships and dependencies between different components.
- Integrate the inventory system with configuration management tools to maintain consistency and accuracy in asset information.
6. Create a rollback plan
A rollback plan is a set of procedures that will support reverting systems to their previous state in case a patch causes unexpected problems or conflicts. It cuts down downtime in the event of patch deployment issues, allowing for a quick recovery.
Expert tips:
- Routinely simulate rollback scenarios to verify the effectiveness of the plan. Conduct mock rollbacks in a controlled environment to uncover potential challenges or gaps in the process so the IT team can optimize the rollback plan for real-world situations.
- Document detailed rollback procedures to guarantee smooth execution.
- Define clear communication protocols to follow in the event of a rollback.
7. Enforce least privilege access
Limit user and system privileges to the minimum required for normal operation to control the potential impact of security vulnerabilities. Restricting access minimizes the attack surface. By granting only necessary permissions, your organizations can diminish the risk of unauthorized modifications to key systems during the patching process.
Expert tips:
- Implement a regular review process for user and system privileges to ensure they remain at the appropriate level even after job roles and responsibilities change.
- Employ role-based access control (RBAC) to assign permissions based on job roles, streamline access management, and reduce complexity.
- Track and audit user activity to detect any unusual or unauthorized access patterns.
8. Monitor and audit patch compliance
Continuously monitor your network to maintain patch compliance and frequently audit systems to confirm the application of patches aligns with established policies. This allows you to identify and rectify any deviations, thus maintaining a consistently secure and up-to-date network environment.
Expert tips:
- Use a centralized patch management dashboard to monitor patch compliance and get real-time visibility into your patching status.
- Segment your network into logical zones and monitor patch compliance within each segment.
- Set up thresholds for acceptable patch compliance levels and configure alerts for deviations from these thresholds.
9. Train employees on the importance of regular updates
Educating employees is crucial to emphasize the significance of regularly updating systems and software. Informed employees are less likely to make errors, contributing to heightened security awareness across your organization. This creates a culture of vigilance and responsibility in relation to software updates.
Expert tips:
- Provide training with real-world examples and scenarios to enhance employee understanding. Using real-world examples and scenarios contextualizes theoretical knowledge, making it more tangible and applicable for employees.
- Offer periodic refresher courses and updates to reinforce the training content.
Bottom line: Follow patch management best practices
The goal of network patch management is not just to fix problems but to proactively maintain the health and security of your network and systems. By following the best practices outlined in this article, your organizations can reduce vulnerability to cyberthreats.
Regular vulnerability assessments, prioritizing patches based on criticality, thorough testing in controlled environments, and automated deployment processes form the foundation of a robust strategy.
In addition, maintaining an updated inventory, a well-defined rollback plan, and enforcing least privilege access contribute to a secure infrastructure. Employee training boosts overall awareness and decreases the risk of human error, while continuous monitoring and audits ensure ongoing compliance.
It’s worth noting, though, that in order to achieve comprehensive network security, it’s imperative to integrate best practices for both networking devices and software applications. This involves adhering to software patch management best practices as well to bolster the security of the entire IT infrastructure.
These patch management best practices, coupled with expert tips, can strengthen your organization’s defense, creating a resilient and well-protected network.
Establishing a patch management policy is an important part of an effective patch management process. Learn how to create your own policy in our complete guide, complete with free template and examples.


