Enterprise Wi-Fi solutions facilitate seamless and secure communication across your organization, connecting devices and enabling employees to access critical resources, applications, and data without the limitations of wired infrastructure.
They go beyond traditional home setups to provide scalable wireless connectivity within your business and meet its demanding needs.
The following are our recommendations for the top enterprise Wi-Fi solutions:
- NETGEAR Business WiFi: Best overall enterprise Wi-Fi.
- Juniper Mist: Best for large enterprises.
- Ubiquiti UniFi: Best for small to medium businesses.
- Sophos Wireless: Best for mixed device environments.
- Cisco Meraki MR: Best for challenging enterprise environments.
- HPE Aruba WLAN: Best for hybrid environments.
- Cambium Enterprise Wi-Fi: Best for service providers.
- ExtremeWireless: Best for high-density environments.
- Fortinet Secure Wireless LAN: Best for remote work.
Top enterprise Wi-Fi solutions comparison
Below is an overview of the best business Wi-Fi solutions today. It shows their speed, range of hardware selection, free trial availability, and pricing details.
| Speed | Hardware selection | Free trial | Pricing | |
|---|---|---|---|---|
| NETGEAR Business WiFi | Up to 6 Gbps | Extensive | 3 months | Starts at $0.83/device/month |
| Juniper Mist | Up to 1.7 Gbps | Extensive | 90 days | Subscription-based pricing |
| Ubiquiti UniFi | Up to 4.8 Gbps | Extensive | No free trial | Starts at $279.00 |
| Sophos Wireless | Up to 8.3 Gbps | Adequate | 30 days(requires Sophos AP purchase) | Per appliance pricing |
| Cisco Meraki MR | Up to 5 Gbps | Adequate | 30 days | Lacks transparent pricing |
| HPE Aruba WLAN | Up to 5.3 Gbps | Adequate | 90 days | Lacks transparent pricing |
| Cambium Enterprise Wi-Fi | Up to 2.9 Gbps | Extensive | No free trial | Lacks transparent pricing |
| ExtremeWireless | Up to 10 Gbps | Extensive | No free trial | Lacks transparent pricing |
| Fortinet Secure Wireless LAN | Up to 9.9 Gbps | Extensive | No free trial | Lacks transparent pricing |
Table of Contents

NETGEAR Business WiFi
Best overall enterprise Wi-Fi
Overall rating: 4.75/5
- Cost: 5/5
- Core features: 5/5
- Integrations: 4.75/5
- Customer support: 4.75/5
- Ease of use: 5/5
NETGEAR Business WiFi is a comprehensive solution providing a range of products customizable to your exact business needs. It delivers high performance with its Wi-Fi 6 technology feature that enables high-speed, reliable, and efficient connections.
This enterprise Wi-Fi comes with advanced Instant VPN, Instant Captive Portal, Instant Mesh, and Instant Wi-Fi features that let your business maximize your network’s potential effortlessly.
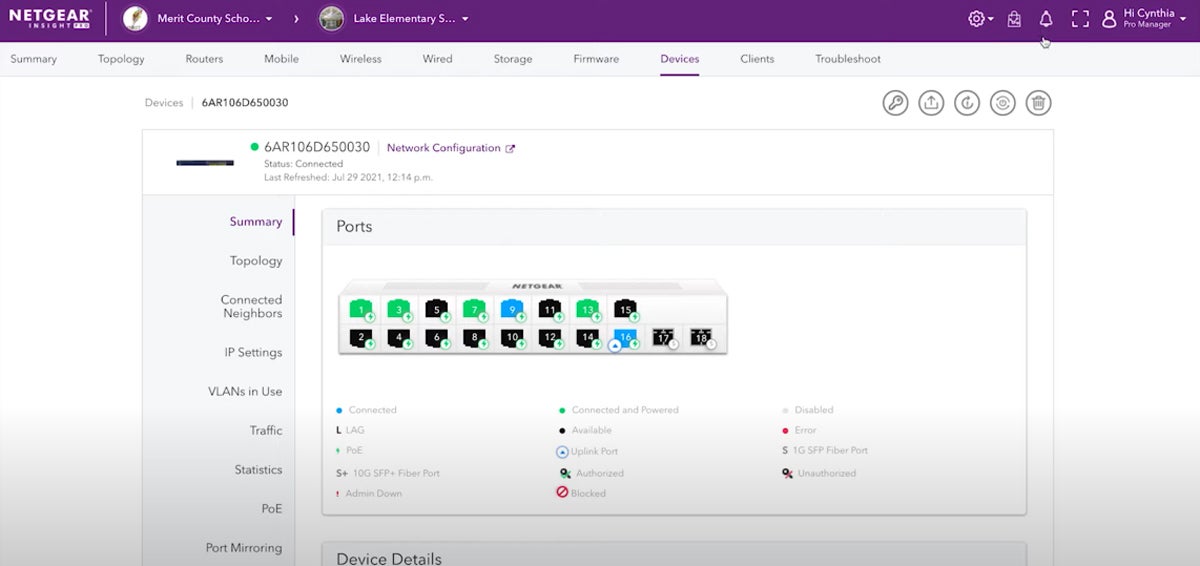
Product design: NETGEAR Insight is a cloud-based platform for the remote management of NETGEAR Business WiFi. Its well-organized dashboard shows a clear overview of your network status and device information, making it easier for you to handle different aspects of your network. It also allows you to customize your summary views so you can control what you want to see.
Product development: NETGEAR has added the S3600 Series to its Smart Switch lineup. These switches aim to address the growing networking demands of high-bandwidth applications and devices in the workplace through high-speed connectivity, and ease of setup and configuration. This product line expansion demonstrates NETGEAR’s dedication to continually enhancing their offerings to meet the evolving needs of their customers.
Why we picked NETGEAR Business WiFi
NETGEAR Business WiFi is our best overall enterprise Wi-Fi because it is cost effective, packed with sophisticated features, and has broad integration capabilities. It also has advanced security features such as WPA3 encryption, robust authentication mechanisms, and secure key management, ensuring the safety of your network.
On top of that, it is user-friendly, offers a wide selection of Wi-Fi hardware appliances, and has solid customer support.
Pros and cons
| Pros | Cons |
|---|---|
| Transparent pricing | 24/7 support only free for the first 90 days |
| Generous trial period of 3 months | NETGEAR Insight software has limited compatibility with older NETGEAR hardware |
| High-speed connectivity | |
| User-friendly |
Pricing
NETGEAR Business WiFi has two pricing plans:
- Insight Premium: Starts at $0.83/device/month
- Insight Pro: Starts at $1.83/device/month
Get in touch with their sales team to find out more.
Features
- High-speed connectivity.
- Wi-Fi 6 technology.
- Supports WPA3 encryption and authentication mechanisms.
- Remote network management.
- Advanced device profiling.
- User role management.
- Analytics and reporting features.
- Network segmentation.
- Dynamic mesh networking.
- Auto-configuration and provisioning.
- Guest access capabilities.
- Insight Instant Captive Portal.
- Support for multiple locations and devices.
- Quality of service (QoS) packet scheduling.
- Distributed denial of service (DDoS) prevention.

Juniper Mist
Best for large enterprises
Overall rating: 4.75/5
- Cost: 3.75/5
- Core features: 5/5
- Integrations: 5/5
- Customer support: 5/5
- Ease of use: 5/5
Juniper Mist is a modern, cloud-based wireless network solution that leverages AI and machine learning (ML) to deliver high-performance Wi-Fi while maintaining visibility and control. It offers features such as AI-driven operations, cloud portal, and automation capabilities, making it an excellent choice for large enterprises with complex networks.
Juniper Mist’s AI-driven operations give optimized configurations, maximum performance, and optimized packet scheduling for increased capacity. Additionally, its cloud portal and automation capabilities streamline network management, simplifying management at a large scale.
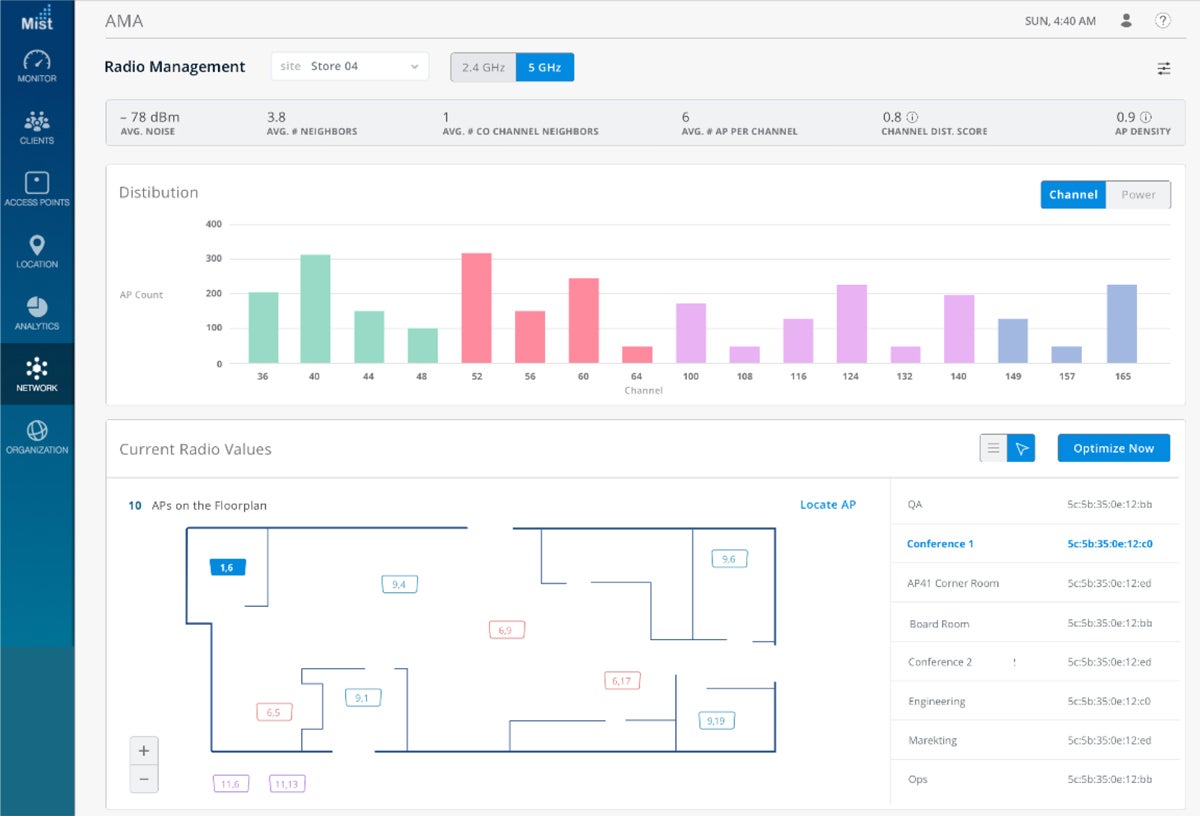
Product design: The Juniper Mist has an intuitive and straightforward interface that’s easy on the eyes. It presents a holistic view of your network with simple tabs and menus that separate different components. The uncluttered design can aid you to quickly identify and fix any network issues, thereby minimizing business downtime and ensuring a smooth user experience.
Product development: Since acquiring Mist Systems in 2019, Juniper Networks continues to focus on AI and cloud services. In 2023, it unveiled a series of enhancements to its AI-driven enterprise portfolio, including integration of ChatGPT with Marvis, Juniper’s unique AI-driven virtual network assistant.
Marvis now allows you to conveniently access knowledge base information using advanced Large Language Models (LLM). This means users can pose technical queries to Marvis and receive not only precise answers, but also a curated list of relevant documents.
Why we picked Juniper Mist
Juniper Mist is one of our choices of top commercial Wi-Fi solutions because of its innovative use of AI and ML for efficient troubleshooting and decision-making. These intelligent capabilities improve overall network performance as well as end-user experience.
Pros and cons
| Pros | Cons |
|---|---|
| User friendly | Limited pricing details |
| Simple configuration | Integration capabilities need improvement |
| AI-driven operations | |
| Generous 90-day free trial duration |
Pricing
Juniper Networks states that Juniper Mist has a subscription-based licensing model, but does not reveal actual pricing. Contact their sales team to request a call.
Features
- AI-driven operations.
- Cloud portal.
- Automation capabilities.
- Asset tracking and room utilization.
- Visitor segmentation and trends.
- Network segmentation.
- Monitoring and behavior reports.
- WAN visibility.
- Secure guest access.
- Customizable guest portal.
- External captive portal integration.
- Single Sign-On (SSO) with identity provider.
- Template-based configuration.
- Dynamic mesh networking.
- Auto-configuration and provisioning.
- Self-healing network.
- WPA3 encryption.
- Advanced authentication mechanisms (802.1X, EAP).
- Secure key management.
- On-premises deployment support.

Ubiquiti UniFi
Best for small to medium businesses
Overall rating: 4.25/5
- Cost: 2.5/5
- Core features: 5/5
- Integrations: 4.75/5
- Customer support: 4/5
- Ease of use: 4.25/5
Ubiquiti UniFi has a range of devices such as access points, switches, and routers, all managed through a single software interface. Some of its key features are high-performance Wi-Fi, advanced device profiling, user role management, and support for dynamic mesh networking.
Ubiquiti UniFi is well-suited for SMBs due to its scalability and cost-effectiveness. The system is designed to grow with your business, allowing you to add devices as needed without significant increases in management complexity. What’s more, the absence of licensing fees for its management software makes it a cost-effective choice for small to medium organizations.
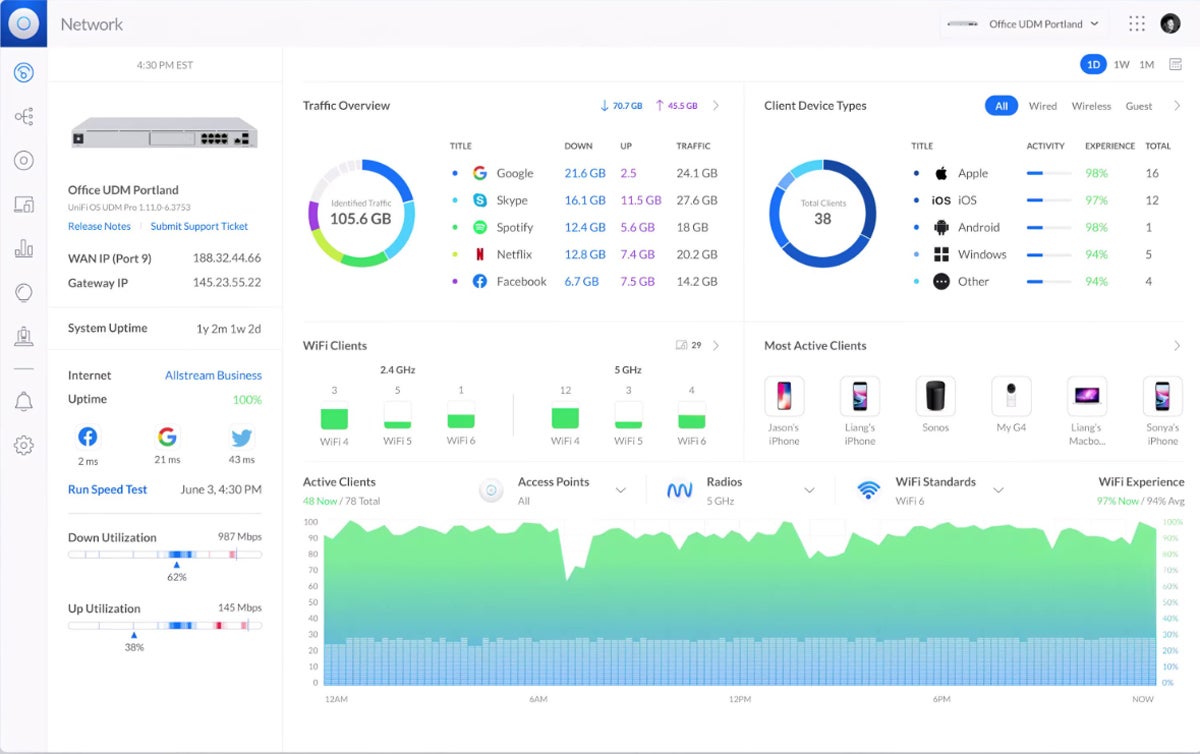
Product design: The UniFi Controller software shows a visual overview of your network’s status and performance. It displays real-time data on network traffic, connected devices, Wi-Fi experiences and clients, as well as APs. The extensive details shown on the dashboard could be confusing and intimidating to some users.
Product development: Ubiquiti’s release of the UniFi Network Application 8.0.24 introduces Admin Settings Change Logs for tracking changes, raises the network limit to 255 for managing larger networks, and includes stability fixes for a more reliable network.
Why we picked Ubiquiti UniFi
We selected Ubiquiti UniFi because it combines performance, scalability, and affordability. Its extensive hardware selection also makes it a smart choice for businesses looking to build and manage their own networks.
Pros and cons
| Pros | Cons |
|---|---|
| Clear pricing | No free trial |
| Cost-savings from being license free | Poor customer support quality |
| Remote management capabilities | Steep learning curve |
| Scalable |
Pricing
Ubiquiti’s software license is free and bundled with the Wi-Fi hardware product. UniFi Enterprise Wi-Fi device prices start at $279.00.
Features
- High-performance Wi-Fi.
- Advanced device profiling.
- Network segmentation.
- User role management.
- Dynamic mesh networking.
- Auto-configuration and provisioning.
- Self-healing network.
- WPA3 encryption.
- Secure key management.
- Guest access capabilities.
- Secure guest networks.
- Captive portal support.
- Remote management.
- License-free software.
- Advanced QoS.
- Per-user rate limiting.
- Real-time traffic dashboards.
- Visual topology maps.
- Support for admin settings change logs.

Sophos Wireless
Best for mixed device environments
Overall rating: 4.5/5
- Cost: 3.75/5
- Core features: 4.5/5
- Integrations: 5/5
- Customer support: 4.75/5
- Ease of use: 5/5
Sophos Wireless is a high-performance Wi-Fi solution managed through Sophos Central, a cloud-based security management platform. It comes with a range of functionalities, such as centralized management, advanced analytics and reporting, guest access capabilities, and advanced device profiling.
The adaptive nature of Sophos Wireless guarantees seamless integration and support for a diverse set of devices, like various operating systems and device types. This adaptability is crucial in environments where users utilize different devices, such as laptops, smartphones, and tablets. Moreover, it enables a smooth and uninterrupted user experience as devices move within the network through the Fast Transition feature.
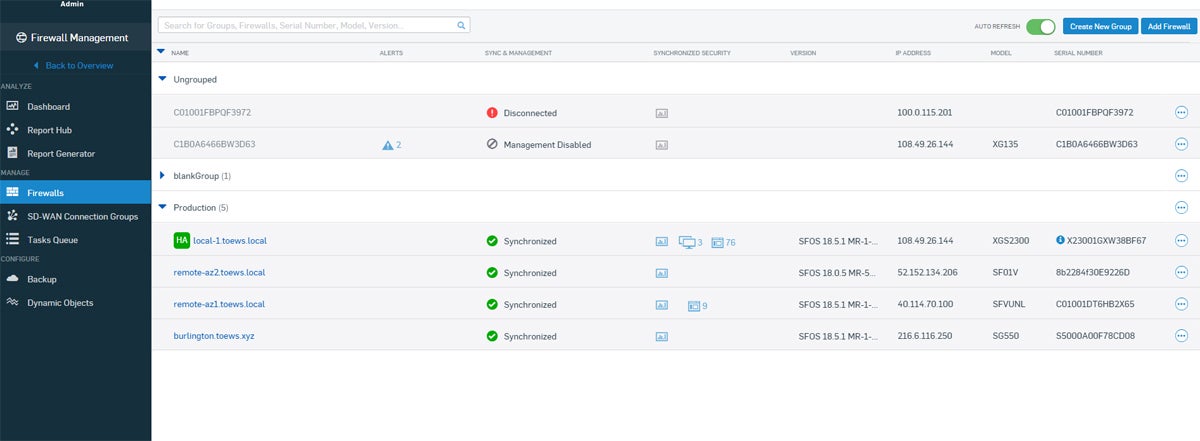
Product design: The Sophos Central lets you manage your Wi-Fi alongside your firewalls and switches, endpoint and server security and operations, and email protection. It offers at-a-glance insights into your enterprise network without looking complex and overwhelming. The dashboard is well-rounded, user-friendly, and provides deeper intelligence into network activity through analytics.
Product development: Sophos launched the AP6 Series, which supports Wi-Fi 6/6E, improves performance, and reduces latency. This series comprises various models designed for diverse environments, including indoor and outdoor settings. This means customers can
Why we picked Sophos Wireless
We picked Sophos Wireless as one of our recommended business Wi-Fi solutions for its advanced security features, high performance, and centralized management capabilities. It comes with strong security measures, including advanced threat protection, secure access controls, and encryption. With high-speed connectivity reaching up to 8350 Mbps, Sophos Wireless meets the demands of high-density networks. Finally, the centralized management interface simplifies administration tasks for businesses.
Pros and cons
| Pros | Cons |
|---|---|
| User-friendly | Limited pricing details |
| Simple deployment | Free trial only available after purchasing Sophos AP |
| Centralized management | Poor customer support quality |
| Rogue AP detection |
Pricing
Sophos mentions on its licensing guide that Sophos Wireless has per-appliance-pricing but does not provide exact prices. Contact their sales for additional details.
Features
- Centralized management.
- Local user interface.
- Scheduled firmware upgrades.
- Mesh networking.
- Dynamic VLAN and RADIUS.
- Web categorization.
- Network segmentation.
- Application visibility.
- Synchronized security.
- Multiple SSIDs.
- Time-based SSIDs.
- Client load balancing.
- Auto channel selection.
- Channel width selection.
- Band steering.
- Airtime fairness.
- Keep broadcasting SSID.
- Roaming assistant.
- Fast Transition feature.
- Captive portal.
- Auto power.
- Enterprise-level authentication.
- Rogue AP detection.
- Voucher authentication.
- Social login.

Cisco Meraki MR
Best for challenging enterprise environments
Overall rating: 4/5
- Cost: 2.5/5
- Core features: 4.75/5
- Integrations: 3.75/5
- Customer support: 3.75/5
- Ease of use: 5/5
The Cisco Meraki MR series is a line of cloud-managed access points with simplified deployment and troubleshooting, making it an ideal solution for challenging enterprise environments that require end-to-end network management.
Additionally, they use advanced Wi-Fi 6 technologies, including orthogonal frequency-division multiple access (OFDMA) and multi-user, multiple input, multiple output (MU-MIMO), beam forming, and channel bonding, delivering the throughput and reliable coverage required by demanding business applications.
This enterprise Wi-Fi also supports auto-configuration and provisioning, ensuring a self-healing network that can adapt to changes and failures in challenging network environments.
Product design: It has a simple dashboard with components neatly grouped together in a sidebar. However, this extreme simplicity lacks granularity in terms of data shown.
Product development: Cisco Meraki recently added a new Callbacks feature in the Meraki Dashboard API, focusing on providing tools that offer automation, efficiency, and convenience. This feature lets you initiate pinging a device or executing a phased deployment, and step back. You receive a notification at your specified webhook URL once it completes the operation.
Why we picked Cisco Meraki MR
We selected Cisco Meraki MR series because of its versatility and ability to adapt to complex network environments, coupled with robust security measures and extensive integration capabilities.

Pros and cons
| Pros | Cons |
|---|---|
| Easy to configure | Unstable mobile app |
| Automatic remediation | Software updates have occasional issues |
| Self-learning RF optimization | Lacks clear pricing |
| Highly-scalable |
Pricing
Cisco Meraki doesn’t display the pricing details on their website. Get in touch with their sales team to learn more.
Features
- Self-configuring plug-and-play deployment.
- 802.11ax MU-MIMO with up to eight spatial streams built for voice and video.
- Dedicated radio for security and RF optimization with integrated spectrum analysis (indoor models).
- Advanced security to protect against malware, ransomware, and C2 callbacks with Umbrella integration.
- Integrated intrusion detection and prevention system (WIDS/WIPS).
- Intelligent firmware upgrades.
- Network segmentation.
- AI/ML-powered analytics for root cause analysis and Wi-Fi troubleshooting.
- Advanced application visibility with Cisco Network-Based Application Recognition (NBAR).
- Flexible group policy engine.
- Wi-Fi personal network (WPN) on any shared network.
- Integrated Bluetooth IoT radio.
- IoT ready (ESL integration).
- Self-healing, zero-configuration mesh.
- Role-based administration.
- Email and text message alerts upon power loss, downtime, or configuration changes.
- FIPS-140-2 compliant, IPv6 compatible, WFA-certified APs.

HPE Aruba WLAN
Best for hybrid environments
Overall rating: 4/5
- Cost: 2.5/5
- Core features: 4.75/5
- Integrations: 5/5
- Customer support: 5/5
- Ease of use: 2.5/5
HPE Aruba WLAN is a business-grade wireless LAN solution with cloud-native, microservices architecture that streamlines IT operations, boosts agility, and reduces costs by unifying the management of all network infrastructure. This enterprise Wi-Fi is well-suited for hybrid environments due to its scalability, seamless integration with hybrid cloud services, unified management capabilities for wired and wireless networks.
HPE Aruba WLAN has the latest Wi-Fi 6 and Wi-Fi 6E standards for high-speed and stable connectivity. Furthermore, it uses artificial intelligence (AI) to power its network operations and proactively identify and resolve network issues. It also comes with advanced security features, including encryption, authentication, and access controls, bolstering overall network security.
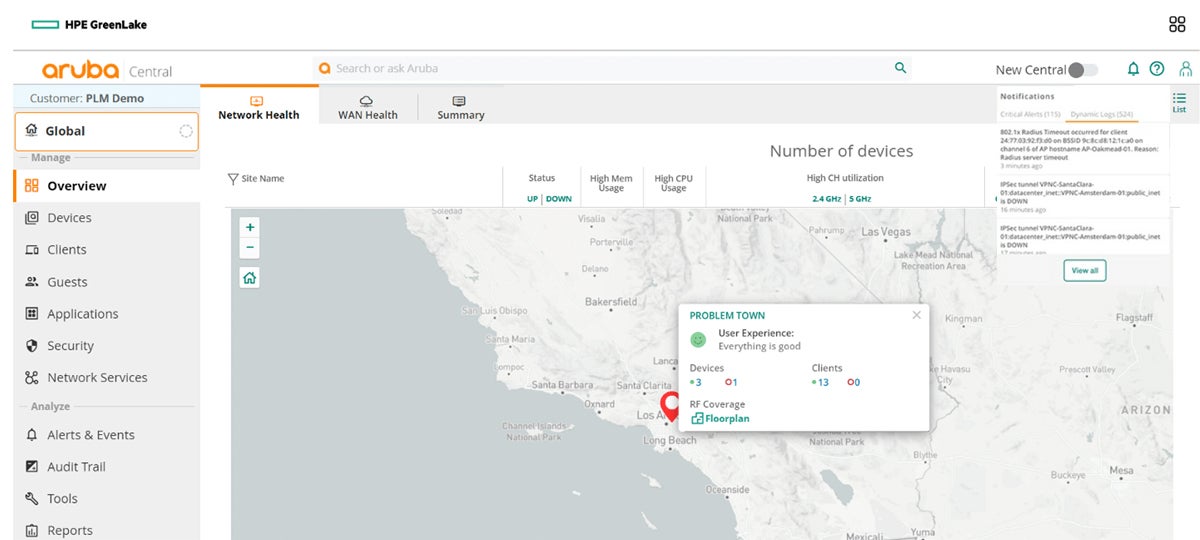
Product design: The Aruba Central dashboard gives a unified view of wired and wireless local area networks (LANs), WANs, and virtual private networks (VPNs) across multiple locations. It offers AI-powered insights, visualizations, workflow automation, and edge-to-cloud security, to ease network management. That said, it has numerous options and settings that may require time and effort to fully understand and navigate.
Product development: HPE Aruba Networking introduced the Aruba Instant On AP22D and the Aruba Instant On 1960 stackable switch to enable small to medium businesses (SMBs) to improve networks with faster speeds, increased capacity, and strengthened security.
Why we picked HPE Aruba WLAN
We chose HPE Aruba WLAN because of its state-of-the-art functionalities combined with high high security levels and dependability. In addition, this enterprise Wi-Fi It is compatible with the latest Wi-Fi 6 and Wi-Fi 6E protocols, guaranteeing better efficiency and bandwidth.
Pros and cons
| Pros | Cons |
|---|---|
| Generous 90-day free trial duration | Lacks transparent pricing |
| AI-powered device profiling | Complex setup |
| Highly-scalable | Steep learning curve |
| Location analytics |
Pricing
HPE Aruba doesn’t publish pricing information on their page. Connect with their sales department for full pricing details.
Features
- Wi-Fi 6 and Wi-Fi 6E support.
- Support for digital transformation and IoT.
- Cloud-managed networking.
- AI-powered network operations.
- Security for the Intelligent Edge.
- Guest encryption.
- Aruba WLAN Portfolio with indoor, outdoor, ruggedized, and remote access points.
- Gateways and controllers.
- OFDMA.
- Target wake time (TWT).
- Dynamic mesh networking.
- Auto-configuration and provisioning.
- Self-healing network.
- Location analytics.

Cambium Enterprise Wi-Fi
Best for service providers
Overall rating: 3.5/5
- Cost: 0/5
- Core features: 4.5/5
- Integrations: 4/5
- Customer support: 3.5/5
- Ease of use: 5/5
Cambium Enterprise Wi-Fi supports the latest Wi-Fi standards, including Wi-Fi 6 and Wi-Fi 6E, delivering high-performance wireless network connections. The solution offers built-in security features and guest access capabilities. In addition, it supports dynamic mesh networking, auto-configuration and provisioning, and self-healing network capabilities, boosting scalability.
This scalability is particularly advantageous for service providers, like broadband service providers or network-as-a-service (NaaS) providers dealing with diverse network sizes and customer needs, as it allows for smooth expansion as demand grows. Of course, this enterprise Wi-Fi also has security features, including encryption and authentication, addressing the concern of data security.
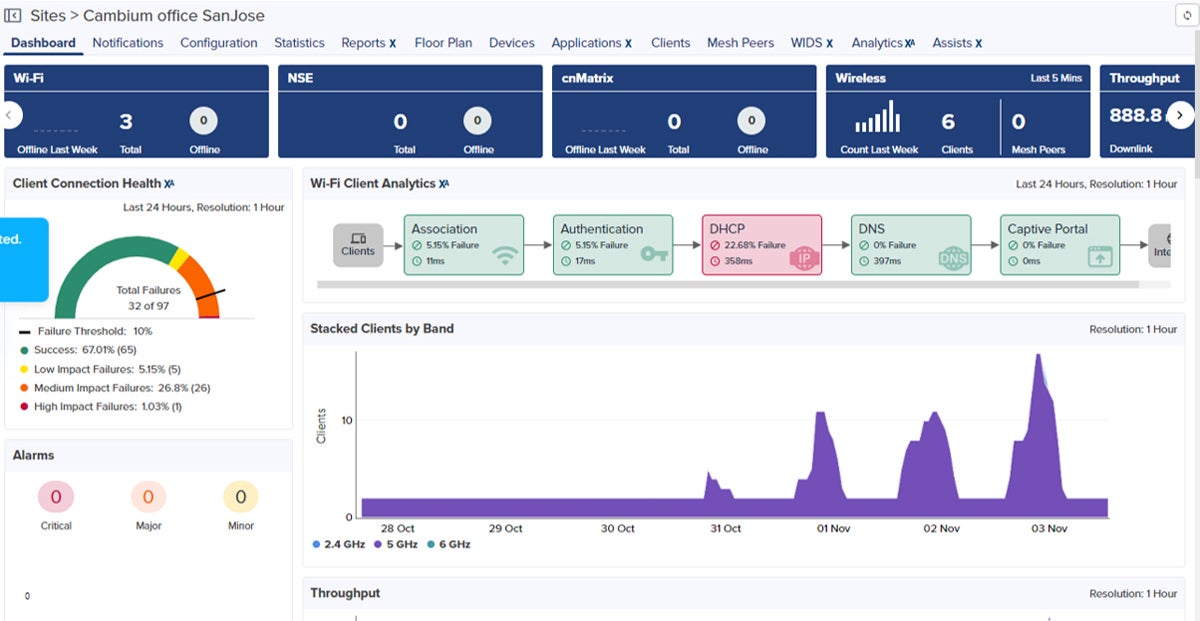
Product design: Cambium’s cnMaestro dashboard brings a single-pane-of-glass view of all network devices and their performance. It includes network statistics, channel utilization graphs, and remote troubleshooting tools. Real-time and historical analytics give insights into network performance, usage patterns, and potential issues.
Product development: Cambium Networks updated its network management system, cnMaestro 4.1, elevating automation and analytics and reducing costs. The new feature, cnMaestro X Assurance, uses analytics to identify and resolve network issues quickly. Other features include Personal Wi-Fi for secure connectivity across campus networks, and Network Service Edge for security and SD-WAN services.
Why we picked Cambium Enterprise Wi-Fi
We picked Cambium Enterprise Wi-Fi for its scalability, comprehensive feature set, and support for the latest Wi-Fi standards that promotes fast and efficient wireless network connections. Its analytics and reporting features also provide valuable insights for network optimization.
Pros and cons
| Pros | Cons |
|---|---|
| Automated device profiling and segmentation | Lacks clear pricing |
| Zero-touch provisioning and maintenance | No free trial |
| User friendly | Hardware products lack durability |
| Simple configuration |
Pricing
Cambium doesn’t disclose pricing details on their official website. Contact their sales representative for a quote.
Features
- Wi-Fi 6 and Wi-Fi 6E support.
- Cloud-first architecture.
- Zero-touch provisioning and maintenance.
- Policy-based access.
- Built-in security features.
- Network segmentation.
- Guest access capabilities.
- Analytics and reporting features.
- Dynamic mesh networking.
- Self-healing network.
- cnMaestro management system.
- Network service edge.
- Advanced device profiling and segmentation.
- Seamless roaming.
- Automatic RF optimization and interference avoidance.
ExtremeWireless
Best for high-density environments
Overall rating: 3.5/5
- Cost: 0/5
- Core features: 5/5
- Integrations: 4.25/5
- Customer support: 3.75/5
- Ease of use: 4.25/5
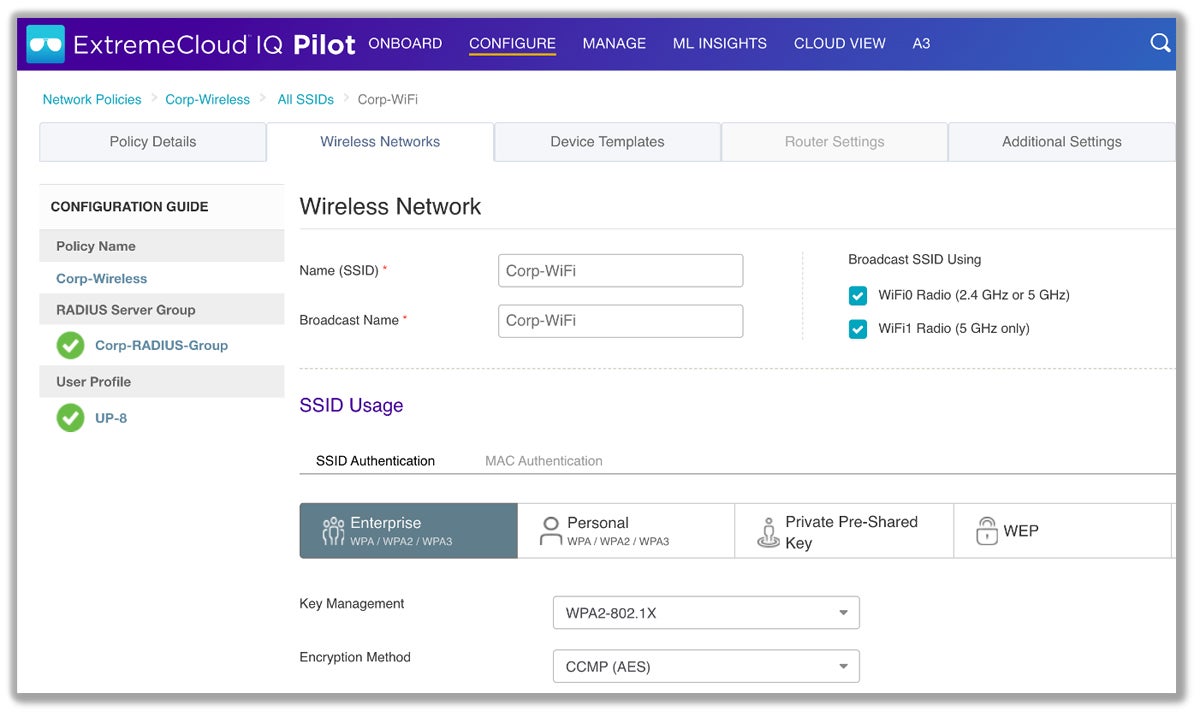
ExtremeWireless by Extreme Networks leverages explainable machine learning (ML) to increase IT efficiency and secure the network with Universal Universal Zero Trust Network Access (ZTNA). This enterprise Wi-Fi solution also uses ExtremeCloud IQ for management, bringing end-to-end visibility and data-driven AIOps for faster network issue resolution.
ExtremeWireless excels in high-density environments thanks to its tri-radio indoor universal APs offering Wi-Fi 6E coverage. These APs can run multiple operating systems for on-premises and/or cloud management, making ExtremeWireless a top choice for environments that need high-speed, high-capacity networks like stadiums, large venues, and conference centers. The high data rates ensure seamless connectivity even in areas with a large number of concurrent users, elevating user experience.
Product design: The ExtremeWireless dashboard gives a detailed insight of the network status with elaborate charts to help monitor the overall status of the wireless network. However, it presents many tabs, sections, and subsections that can make it challenging for some users to locate certain capabilities.
Product development: Extreme Networks has presented the ExtremeCloud Universal ZTNA, a groundbreaking solution that integrates network, application, and device access security into one platform. This will provide a consistent security policy across the entire network and make it easier for IT teams to manage and secure user access across multiple locations. The solution is set to be available in early 2024.
Why we picked ExtremeWireless
We selected ExtremeWireless because its high data rates and reliability promotes consistent and stable wireless connectivity. Its scalability allows organizations to easily expand their networks to accommodate growth.
Pros and cons
| Pros | Cons |
|---|---|
| Uses ML to analyze and interpret millions of network and user data points | Lacks clear pricing |
| AI-driven Wi-Fi architecture | No free trial |
| Easy to configure | Load balancing isn’t ideal for roaming |
Pricing
Extreme Networks doesn’t disclose pricing structure for ExtremeWireless. For updated prices, get in touch with their sales team.
Features
- Cloud management.
- Explainable ML secures networks with Universal ZTNA.
- End-to-end visibility.
- Data-driven AIOps.
- Context-based optimization.
- Advanced captive portal support.
- Full-stack management of access points, switches, and SD-WAN through ExtremeCloud IQ.
- Advanced device profiling.
- User role management.
- Analytics and reporting.
- Dynamic mesh networking.
- Auto-configuration and provisioning.
- Tri-Radio access points.
- Software-selectable operating systems.
- Interference-free spectrum.
- Extended temperature range.
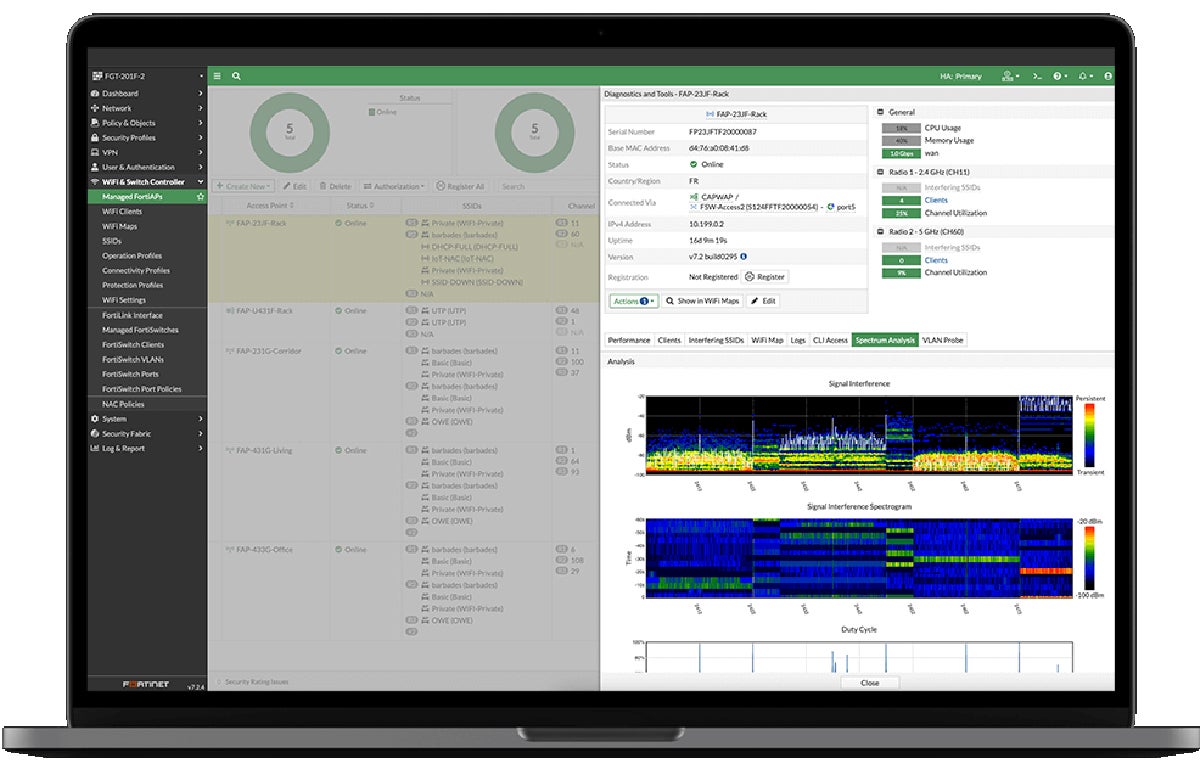
Fortinet Secure Wireless LAN
Best for remote work
Overall rating: 3.25/5
- Cost: 0/5
- Core features: 4.5/5
- Integrations: 4/5
- Customer support: 4.75/5
- Ease of use: 2.5/5
Fortinet Secure Wireless LAN integrates wireless and wired access, security, authentication, switching, and management into a single system. Some of its key features include secure networking, end-to-end network visibility, automated threat response, unified management, and flexible deployment options. It also supports zero-touch deployment, making it fast and simple to deploy without needing on-site tech support.
Fortinet Secure Wireless LAN is best for remote work environments because of its specific features for encryption and wireless connection security, safeguarding sensitive data and communications as remote employees access corporate networks. Additionally, its focus on integrated security policies makes sure that remote workers benefit from advanced threat protection, reducing the risk of cyber threats.
Product design: This enterprise Wi-Fi solution has a highly-detailed software interface with graphs and intricate details for status, analysis, and diagnostics. This abundance of in-depth information can be overwhelming for some users.
Product development: Fortinet launched high-performance FortiSwitch 600 and 2000 to cater to the growing connectivity needs of campuses. These products have embedded intelligence and readily integrate with Fortinet’s AIOps management tool and FortiGuard AI-Powered Security Services.
Why we picked Fortinet Secure Wireless LAN
Despite losing some points for its lack of transparent pricing or free trial, Fortinet Secure Wireless LAN made it to our list because of its solid security features and flexibility.
It incorporates threat protection, encryption, and consolidated security policies, fortifying wireless networks against potential threats. Furthermore, it has tight integration with other Fortinet security products, forming a cohesive security infrastructure.
Pros and cons
| Pros | Cons |
|---|---|
| Built-in security | Lacks clear pricing |
| Automated threat response | No free trial |
| SASE-ready | Complex setup |
| High-speed connectivity | Steep learning curve |
Pricing
Pricing information is not available on Fortinet’s website. For updated pricing, reach out to their sales department.
Features
- Secure networking.
- Integrates with the Fortinet Security Fabric.
- End-to-end network visibility.
- Automated threat response.
- Unified management.
- Flexible deployment.
- Zero-touch deployment.
- Network segmentation.
- Secure access service edge (SASE).
- Wireless presence analytics.
- Device profiling.
- Role-based access control (RBAC).
- Wireless mesh network.
- IoT segmentation.
- Captive portal.
Key features of enterprise Wi-Fi solutions
Enterprise Wi-Fi solutions should have features for security, high-performance, guest access, device management, scalability, and integrated hardware selection.
Security
Security is a critical feature of an enterprise Wi-Fi solution that includes measures to safeguard the network from unauthorized access and data breaches. This entails implementing access controls, encryption protocols to protect data during transmission, and mechanisms to prevent unauthorized users from gaining access. Wi-Fi network security is a must, especially in the age of advanced connectivity and the proliferation of 5G network providers.
High-performance capability
Enterprise Wi-Fi performance refers to the speed, reliability, and overall efficiency of the network. A high-performance Wi-Fi network contributes to productivity by guaranteeing quick and uninterrupted access to resources and applications. It also positively influences the user experience for employees, customers, and guests.
Guest access
Guest access lets non-employees connect to the Wi-Fi network with restricted privileges. This functionality gives convenience for visitors and clients to access the internet while visiting the enterprise. Simultaneously, it segregates guest traffic from the internal network, mitigating potential security risks.
Device management
Device management involves monitoring, controlling, and handling devices connected to the Wi-Fi network. It aids in inventory management by keeping track of all connected devices, facilitating troubleshooting efforts, and equipping administrators to enforce security policies. Effective device management strengthens network integrity and optimizes the operation of connected hardware devices.
Scalability
Scalability determines the ability of the enterprise Wi-Fi solution to adapt to the growing demands of an expanding enterprise. It supports business growth by accommodating an increasing number of users and devices. This feature aids in the addition of new access points and network infrastructure as needed and prevents congestion and performance degradation as the network expands.
Integrated hardware selection
The selection of hardware is another key aspect of an enterprise Wi-Fi solution, and vendors often offer a comprehensive hardware ecosystem tailored to complement their Wi-Fi software. This encompasses access points, controllers, switches, firewalls, and antennas for smooth integration.
How we evaluated enterprise Wi-Fi solutions
We thoroughly analyzed various options available in the current market to identify the best-performing enterprise Wi-Fi solutions today.
Our evaluation concentrated on five key criteria: cost, core features, integrations, customer support, and ease of use. We systematically assessed the performance of each enterprise Wi-Fi based on these criteria, assigning ratings and subsequently calculating their overall scores.
Cost – 20%
For this category, we considered the pricing transparency and the availability of free trial, as well as its duration.
Criterion winner: NETGEAR Business WiFi.
Core features – 30%
To determine scores for core features, we researched if each enterprise Wi-Fi solution has built-in features for security, high-performance, guest access, device management, and analytics and reporting. We also measured if the solution is scalable and checked the extensiveness of their selection of hardware devices.
Criterion winners: NETGEAR Business WiFi, Juniper Mist, and Ubiquiti UniFi.
Integrations – 20%
To calculate scores for this category, we considered if the enterprise Wi-Fi supports direct integration with third-party tools for network management and monitoring, security information and event management (SIEM), identity and access management (IAM), and cloud services and applications. We also considered support for custom integrations.
Criterion winners: HPE Aruba WLAN, Juniper Mist, and Sophos Wireless.
Customer support – 15%
We checked the availability of 24×7 customer support services to compute scores for this category. We verified whether support is accessible via live chat, phone, and email, and if the vendor has an active user community and in-depth documentation. Customer feedback is also taken into account in calculating the scores for this criterion.
Criterion winners: HPE Aruba WLAN and Juniper Mist.
Ease of use – 15%
For ease of use, we factored in the user-friendliness of the enterprise Wi-Fi’s software as well as the simplicity of its configuration/setup for all users, regardless of technical expertise. We looked into feedback from independent sources to find out how users feel about the solution.
Criterion winners: Cisco Meraki MR, Cambium Enterprise Wi-Fi, Juniper Mist, and Sophos Wireless.
Frequently Asked Questions (FAQs)
Who needs an enterprise Wi-Fi solution?
Enterprise Wi-Fi solutions are important for businesses and organizations that operate in environments where a substantial number of users rely on wireless connectivity, such as corporate offices, educational institutions, and healthcare facilities.
These solutions are also valuable if your business involves extensive data transmission, multiple devices accessing the network concurrently, or demands stringent security measures.
What are good office Wi-Fi solutions?
Based on our extensive evaluation, NETGEAR Business WiFi and Juniper Mist are the top two best office Wi-Fi solutions in terms of core features.
Bottom line: Keep your business connected with the top Wi-Fi solutions
The top enterprise Wi-Fi solutions on this list are designed to give you an idea of the top players in the market and what you should expect from commercial Wi-Fi solutions. In selecting the best enterprise Wi-Fi for your business, don’t forget to check its security features, scalability, customer support quality, integration capabilities, and ease of use, in addition to its speed and cost.
This guide serves as a reference to help you decide which solution to choose for your organization, depending on your budget, business size, and specific needs.
Enterprise Wi-Fi solutions and network switches work together to enhance your organization’s connectivity. Read our guide on the best network switches to find out our top recommendations and further bolster your network infrastructure.


