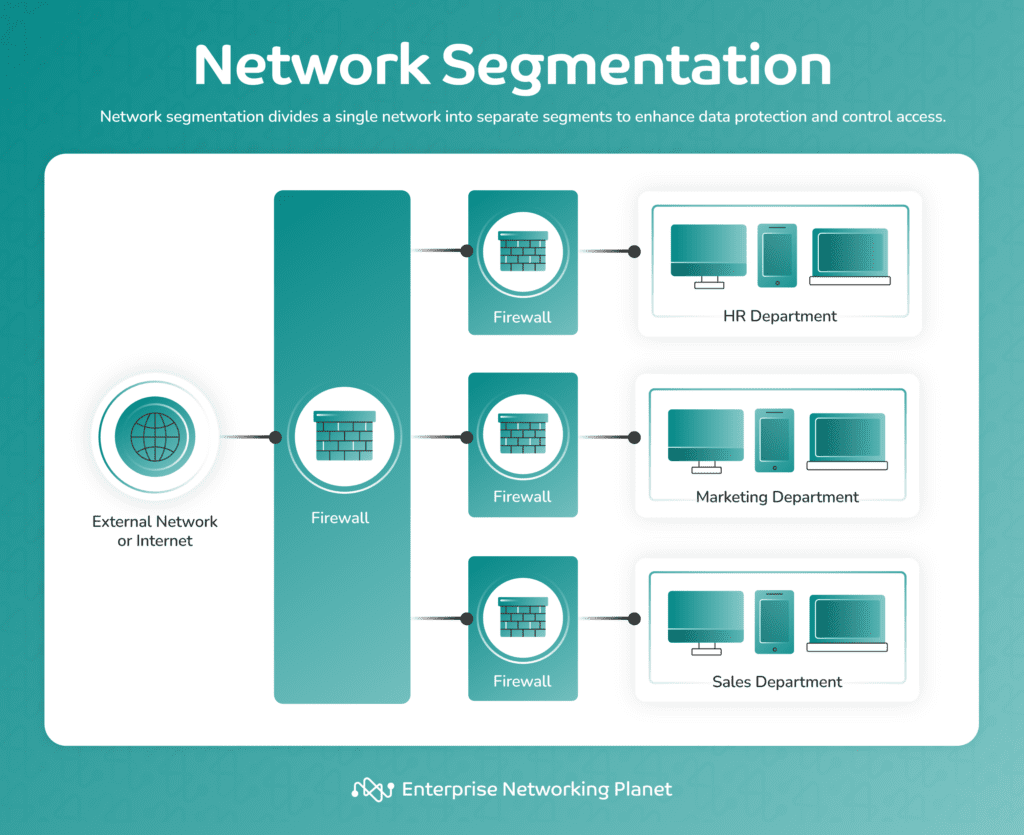
Network segmentation is a crucial security practice that minimizes the potential impact of security breaches and limits lateral movement by attackers by dividing a network into smaller, isolated segments. This process refines control access and allows for more precise management of resources and policies within each segment.
Table of Contents
1. Define clear objectives
Define why you need network segmentation and what specific goals you aim to achieve with it. Establishing goals will guide your strategy and make sure it aligns with your security objectives.
Clear objectives are the foundation of a successful segmentation strategy. They also ensure that segmentation efforts use resources effectively to protect your organization’s critical assets.
Things to consider in defining objectives:
- Prioritize objectives based on urgency and risk.
- Involve key stakeholders in defining objectives to align with organizational needs.
- Periodically revisit and update objectives as network and security requirements evolve.
How to implement clear objectives
Start by conducting a thorough risk assessment to identify your organization’s most important assets and potential threats. Determine whether your primary goal is to protect sensitive data, prevent lateral movement, or achieve compliance. Based on your objectives, develop a segmentation plan that outlines which segments to create, what they will contain, and how they will connect.
2. Follow least privilege access
Follow the principle of least privilege, verifying that users and devices have only the minimum level of access required to perform their functions. Regularly review and update permissions to maintain the principle.
This step minimizes the attack surface and the risk of unauthorized access. It limits the potential impact of security incidents by ensuring that users and devices only have access to what they need.
Things to consider in following least privilege access:
- Utilize monitoring and alerting systems to promptly detect and respond to unauthorized access attempts.
- Create a transparent procedure for managing exceptions and temporary access requirements, checking thorough documentation, and adhering to time limits.
- Use automated systems and identity access management (IAM) tools to enforce least privilege access.
How to implement least privilege access
Craft a role-based access control (RBAC) system that is compatible with your segmentation strategy. Assign permissions and access levels strictly based on job roles and responsibilities. Continue to regularly review and update permissions to ensure they match users’ current job functions.
3. Separate critical assets
According to a study published in SpringerLink, it is essential to identify and separate critical assets in a network as a proactive measure for effective cybersecurity risk management. With this in mind, segment integral assets into dedicated segments to decrease the risk of compromise.
This guarantees that if an attacker breaches one segment, you can limit their actions. This step strengthens security by preventing data breaches and minimizing associated disruptions.
Things to consider in separating critical assets:
- Enhance monitoring and logging for asset segments to detect and respond to threats promptly.
- Conduct penetration testing and security assessments to assess the effectiveness of isolation measures.
- Make sure that critical assets have backup and redundancy mechanisms in place for resilience.
How to implement critical asset separation
Find out which assets are the most important for your organization, for example, the servers that store your data, the controllers that manage your domains, or the systems that handle your finances. Separate these assets into different segments that have tight access controls. Use firewalls and network policies to limit the traffic that goes in and out of these segments, allowing only what is essential.
4. Avoid over-segmentation
Avoiding over-segmentation is imperative to guaranteeing that your network segmentation strategy remains manageable, cost-effective, and operationally efficient. Over-segmentation can lead to increased complexity, administrative overhead, and potential performance issues.
Things to consider in avoiding over-segmentation:
- Weigh the cost of implementing and maintaining additional segments against the security benefits they provide.
- Analyze the operational impact of segmentation, factoring in elements like performance, ease of management, and scalability.
- Streamline the number of segments to maintain a manageable and comprehensible network architecture.
How to avoid over-segmentation
Strike a balance between security and operational efficiency by avoiding creating an excessive number of segments. Define clear use cases and security requirements for each segment, prioritize based on risk, and regularly review and consolidate segments when necessary. In addition, consider using automation and orchestration to manage segments efficiently while monitoring network status to prevent performance degradation due to over-segmentation.
5. Administer network monitoring and logging
Leverage robust network monitoring and logging solutions to detect unauthorized access or suspicious activities within your segmented networks and ultimately respond to threats promptly.
Security information and event management (SIEM) systems can help with this step. These systems collect and analyze data from a variety of sources, including firewalls, intrusion detection systems, and security event logs. Then, they use this data to uncover potential threats and send alerts so that you can take action to mitigate them.
Things to consider in administering network monitoring and logging:
- Deploy network monitoring tools that offer comprehensive visibility across all segments and network traffic.
- Safeguard log data to prevent unauthorized access or tampering, as logs are required for post-incident analysis.
- Define log retention policies to guarantee vital data retention for an appropriate duration for analysis and compliance.
How to administer network monitoring and logging
Utilize intrusion detection systems (IDS) and intrusion prevention systems (IPS) to monitor traffic within your network segments. Also, employ comprehensive logging solutions and conduct regular log reviews. Set up alerts for suspicious activities, such as multiple failed login attempts or unusual traffic patterns.
6. Orchestrate regular audits and reviews
Reviews and audits help you address weaknesses, misconfigurations, and access control issues before attackers can exploit them. Periodically review and audit your network segmentation strategy to confirm its effectiveness and alignment with your security objectives. Adjust as needed to address new threats or changes in your network environment.
Things to consider in orchestrating regular audits and reviews:
- Remain vigilant about emerging threats and vulnerabilities to assess the relevance of your segmentation controls.
- Prepare to quickly adjust the segmentation strategy in response to new threats or significant changes in the network environment.
How to implement regular audits and reviews
Use vulnerability scanning tools to identify weaknesses in segment configurations as part of your review process. Revisit access controls and permissions to ensure they are up-to-date and in line with the principle of least privilege.
7. Enforce strong authentication
Apply strong authentication methods, such as multi-factor authentication (MFA) or biometrics, for accessing segmented resources to boost security. This adds an extra protection against unauthorized access. It safeguards sensitive resources and user accounts, decreasing the risk of credential-based attacks.
Things to consider in enforcing strong authentication:
- Determine the appropriate authentication strength based on the sensitivity of the segmented resources.
- Administer strong password policies in conjunction with other authentication methods to prevent weak passwords from compromising security.
- Consider adaptive authentication systems that adjust authentication requirements according to user behavior and risk factors.
How to implement strong authentication
Utilize MFA tools for accessing sensitive resources within segmented networks. Require users to give at least two authentication factors, such as a password and a mobile app token or a fingerprint scan. Additionally, verify proper MFA configuration and application for all relevant accounts and systems.
8. Build an incident response plan
Develop an in-depth incident response plan that includes procedures for addressing security incidents within segmented networks. This plan should outline steps for containment, investigation, and recovery. This plan guarantees a swift and effective response from your organization to contain and rectify security breaches occurring within network segments.
Things to consider in building an incident response plan:
- Set categories of incidents based on severity and potential impact on segmented networks.
- Assemble an incident response team with designated roles and responsibilities, including network and security experts.
- Develop clear escalation procedures for escalating incidents to higher levels of management or external authorities, if necessary.
How to implement an incident response plan:
Define roles and responsibilities for incident responders within each segment, and establish communication channels and incident escalation paths. Conduct regular tabletop exercises to ensure team preparedness to respond effectively to incidents.
9. Educate employees and users
Educate employees and users about the significance of network segmentation security best practices. Make them aware of the risks and their role in maintaining network security. This step reduces the likelihood of social engineering attacks, helps users recognize threats, and fosters a security-conscious culture within your organization.
Things to consider in educating employees and users:
- Use real-world examples and case studies to illustrate the impact of security incidents and the importance of segmentation.
- Conduct security awareness simulations or exercises to test how well employees respond to security incidents.
How to educate employees and users
Build comprehensive training programs on how to secure a network that include network segmentation awareness. In addition, conduct regular training sessions and refreshers to keep them up to date on security practices. Finally, create a feedback loop with users to gather input on training effectiveness and areas for improvement.
Bottom Line: Network segmentation best practices
Knowing how to segment a network properly is quickly becoming a necessity in today’s digital age. Network segmentation provides an effective defense-in-depth strategy, bolstering security, optimizing network performance, and ensuring regulatory compliance.
While the process may seem complex, the benefits far outweigh the initial effort. By following network segmentation best practices, you can create a comprehensive and protected network environment. A well-segmented network is your first line of defense against cyber threats. So, take the time to plan your strategy carefully, and maintain it continually.
Ready to put these practices into action? Explore our guide on top network segmentation tools and software to find the right one for you.


